What You’ll Learn
⏱️ 12 min read
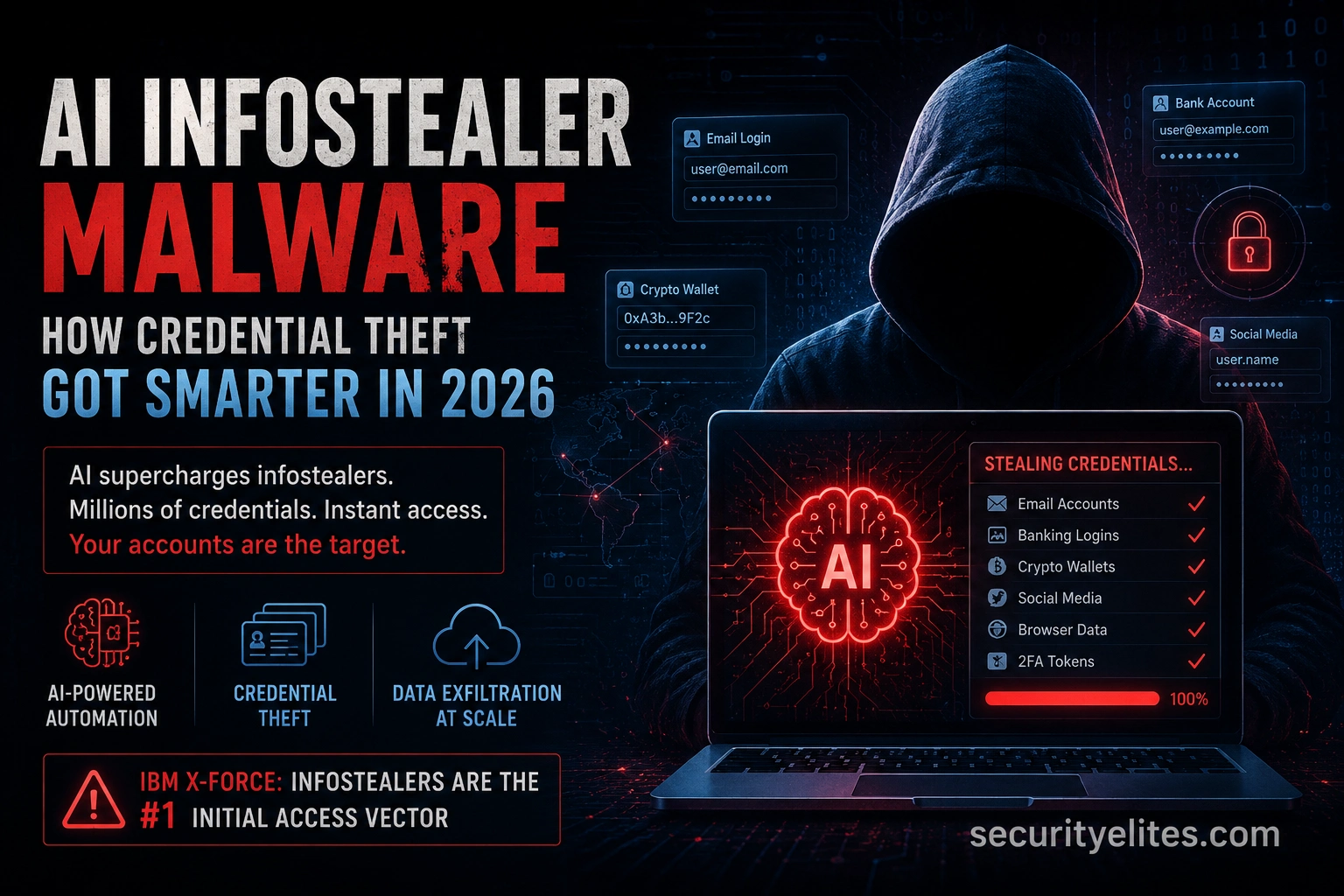
AI Infostealer Malware — 2026 Guide
Infostealers are the harvesting tool for the credentials that enable AI-powered phishing campaigns to succeed. Check your own credential exposure right now with the Email Breach Checker and Password Breach Checker. The broader AI attack landscape is in the AI agent attack guide.
What Infostealer Malware Is
Infostealers are the most economically significant malware category in 2026 from a pure credential-theft perspective — IBM X-Force confirmed this finding with data drawn from thousands of real-world incidents globally across multiple sectors. An infostealer is a category of malware designed specifically to harvest credentials and sensitive data from an infected machine and exfiltrate them to an attacker. Unlike ransomware — which announces itself — infostealers operate silently. The infected user typically has no idea anything has happened until credentials start appearing in breach databases or their accounts start being accessed. My classification of what a modern infostealer targets.
How AI Amplifies Infostealers
IBM X-Force noted in their 2026 report that “the growing use of AI chatbots and agents in business operations creates a new attack surface for infostealer malware.” My analysis of the three specific ways AI has made infostealers more dangerous in 2026.
Why Stolen Credentials Are So Dangerous
The question I get most often when presenting on infostealers: “why does my password matter if I use MFA?” My answer: infostealers don’t just steal passwords. They steal session cookies — and session cookies bypass MFA entirely because they represent an already-authenticated session. This is the critical misunderstanding that leaves MFA-protected accounts vulnerable to infostealer compromise.
Go to SecurityElites Email Breach Checker: /tools/email-breach-checker/
Enter every email address you use for work or important personal accounts
Step 2: Check your passwords
Go to SecurityElites Password Breach Checker: /tools/password-breach-checker/
Check the passwords you reuse across multiple accounts
Step 3: Check Have I Been Pwned
haveibeenpwned.com — check email addresses for known breach appearances
Note: which breaches? When? What data was included?
Step 4: Audit your browser’s saved passwords
Chrome: chrome://password-manager/passwords
Look for: reused passwords, old passwords, passwords for sensitive accounts
Count how many accounts use the same password
Step 5: Check for exposed developer credentials
If you’re a developer: grep -r “password\|api_key\|secret” ~/.ssh ~/ (be careful — read only)
Check: are any credentials stored in plaintext files on your machine?
Controls That Stop Infostealer Attacks
The Infostealer Underground Economy
My picture of the infostealer ecosystem in 2026 isn’t just about the malware itself — it’s about the economy that’s built around it. Infostealers are not typically used by the people who write them. They operate as Malware-as-a-Service products, sold or rented to operators who deploy them and then sell the harvested credentials in underground marketplaces. Understanding this economy helps defenders prioritise — the most valuable stolen credentials get resold fastest and used most aggressively.
Corporate Infostealer Risk — What Security Teams Miss
The individual credential theft risk is well-understood. My concern for corporate security teams is the organisational risk profile: employees working from personal devices, using personal browsers with corporate credentials saved, connecting to corporate systems from home networks. Every personal device an employee uses to access corporate resources is a potential infostealer exposure surface that the corporate security team has limited visibility into.
AI Platform Credentials — The New High-Value Target
IBM X-Force’s 2026 report specifically highlighted AI chatbot and agent credentials as a new high-value infostealer target. My concern about this category: an attacker who steals an employee’s ChatGPT or Claude session token doesn’t just gain access to the victim’s conversation history. They inherit the victim’s AI agent permissions — meaning any MCP servers, tool integrations, and autonomous capabilities the victim’s AI agent was granted.
AI Infostealers — Key Points
Check Your Exposure Now
Use the Email Breach Checker and Password Breach Checker to check your current exposure. If your credentials appear in breach data, change them immediately and enable MFA on the affected accounts.
Quick Check
Frequently Asked Questions
What is infostealer malware?
Does MFA protect against infostealers?
How do infostealers get onto devices?
AI Phishing 2026 — Multi-Persona BEC
Email Breach Checker
Further Reading
- Email Breach Checker — Check your email addresses against known breach databases immediately. If your credentials are in breach data, change the affected passwords and enable MFA on those accounts today.
- AI Phishing 2026 — The delivery mechanism that gets infostealers onto devices. How AI-generated phishing achieves 3–5x higher click rates and how multi-persona BEC campaigns work.
- How Password Attacks Work — The full methodology of credential-based attacks including credential stuffing, password spraying, and how stolen credential databases are used across services.
- IBM X-Force Threat Intelligence Index 2026 — The primary source identifying credential theft as the #1 initial access vector, with AI-amplified credential harvesting and the infostealer data cited above.