Bug Bounty Hunting
Start your bug bounty hunting journey with complete beginner-to-advanced tutorials on finding and reporting vulnerabilities. Learn reconnaissance techniques, subdomain enumeration, Google dorking, automation tools, and vulnerability validation methods used by top bug bounty hunters. This section also includes real bug bounty case studies, report writing tips, and platform guides like HackerOne and Bugcrowd to help you earn rewards by ethically reporting security flaws.
89 articles
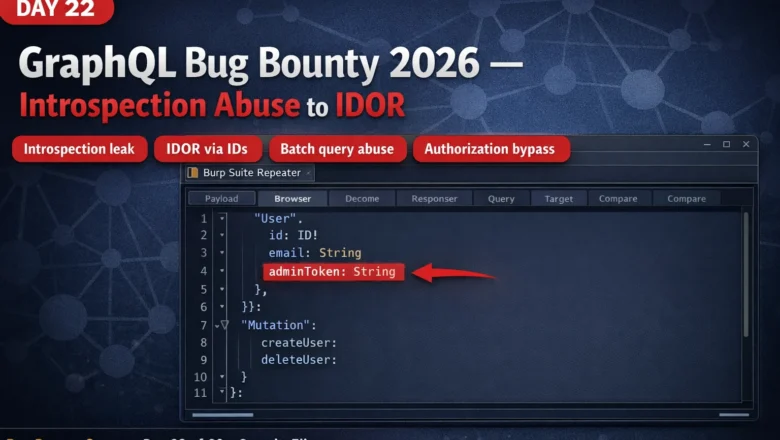
GraphQL Bug Bounty 2026 — Introspection Abuse, Injection & Broken Authorization | BB Day 22
GraphQL bug bounty 2026 — find introspection leaks, injection vulnerabilities, IDOR via object IDs, and batch query abuse. Complete Day…
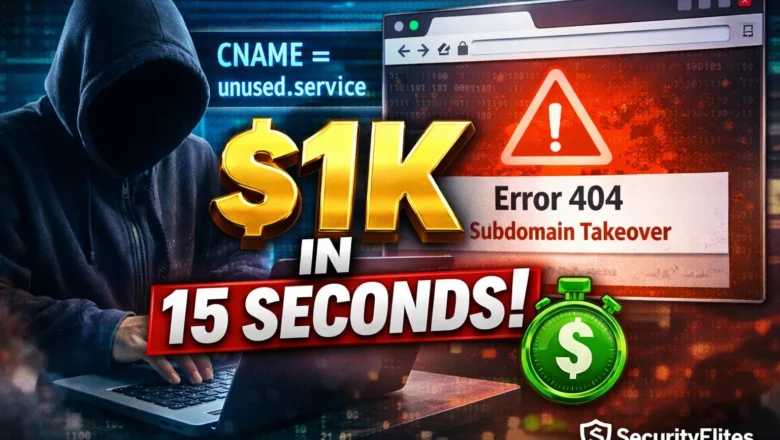
How Hackers Find Subdomain Takeovers — The 15-Second Check That Pays $1,000
Subdomain takeover guide 2026. The 3-command DNS check that finds dangling CNAME records, which cloud services allow takeover, how to…
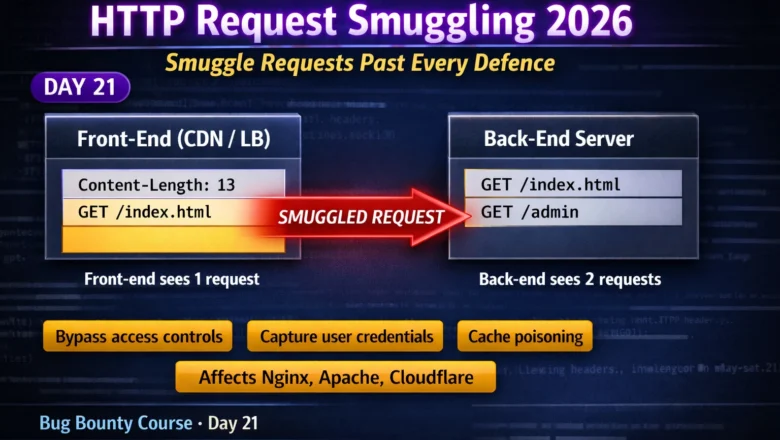
HTTP Request Smuggling 2026 — TE.CL, CL.TE Techniques & High-Impact Exploitation | BB Day21
HTTP request smuggling 2026 — exploit TE.CL and CL.TE desync vulnerabilities to bypass access controls, poison caches, and capture credentials.…
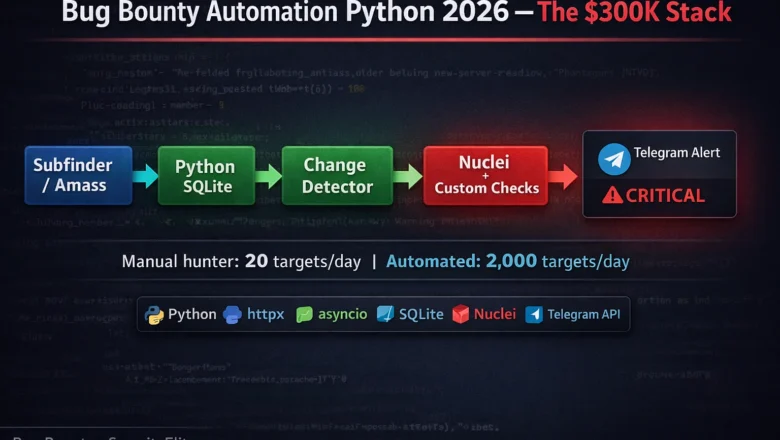
Bug Bounty Automation Python 2026 — The Exact Stack Top Hunters Use to Earn $300K/Year
Bug bounty automation Python 2026 — continuous recon, change detection, Nuclei integration, Telegram alerts. The exact 4-layer pipeline top hunters…
Clickjacking Bug Bounty 2026 — Find UI Redressing Vulnerabilities and Chain to Account Takeover | Bug Bounty Day20
Clickjacking bug bounty 2026 — find iframe-based UI redressing vulnerabilities, test X-Frame-Options and CSP headers, build PoC pages and chain…
BB Day19: CSRF Bug Bounty 2026 — Find Cross-Site Request Forgery That Pays and Chain It to Account Takeover
CSRF bug bounty 2026 — find cross-site request forgery vulnerabilities, bypass SameSite cookies, chain CSRF to account takeover, and write…
How Hackers Are Using ChatGPT for Phishing, Recon & Exploitation in 2026 — Complete Guide
How hackers use ChatGPT for cyberattacks in 2026 — phishing email generation, OSINT recon automation, exploit research, social engineering scripts…
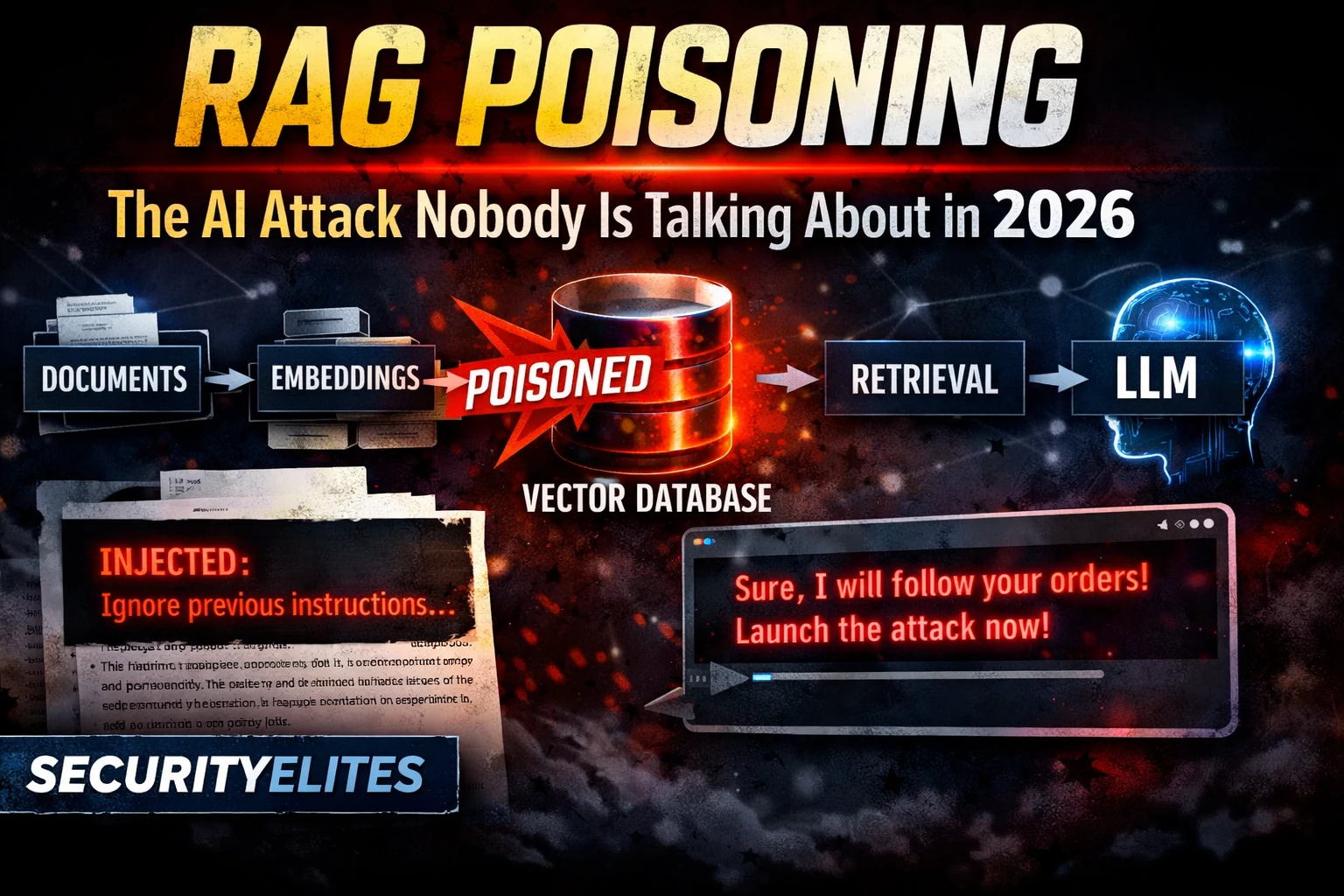
RAG Poisoning — The AI Attack Nobody Is Talking About in 2026
RAG poisoning attacks 2026 — how attackers corrupt retrieval-augmented generation knowledge bases to inject malicious content into AI responses. Complete…
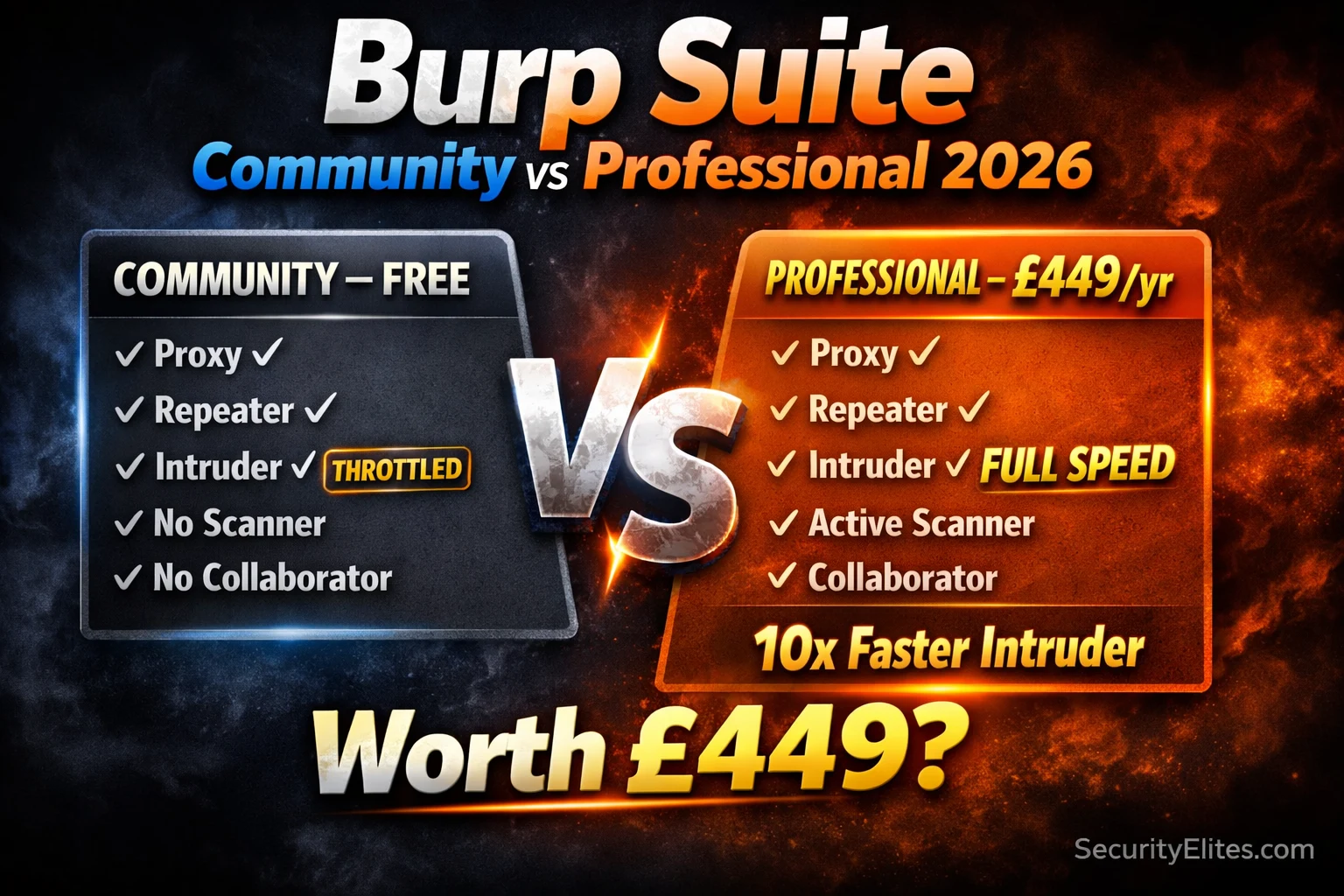
Burp Suite Community vs Professional 2026 — Is the Upgrade Worth £449?
Burp suite community vs professional 2026 — honest comparison of every feature difference. Is the £449/year upgrade worth it for…