Cyber Security Tools
Discover the most powerful cyber security tools and ethical hacking tools used by penetration testers and security researchers. This category features detailed tutorials, installation guides, and usage walkthroughs for reconnaissance, exploitation, OSINT, wireless testing, and password cracking tools. Explore both free and premium security tools, compare their features, and learn how to use them effectively in real penetration testing scenarios.
81 articles
Kali Linux Day 11: Aircrack-ng Tutorial 2026 — Crack WiFi Passwords & Audit WPA2 Security
Aircrack-ng tutorial in Kali Linux 2026 — capture WPA2 handshakes, run dictionary attacks, audit wireless security. Day 11 complete guide…
Kali Linux Day 10 : Metasploit Tutorial Kali Linux 2026 — msfconsole, Modules & First Exploit Complete Guide
Master Metasploit in Kali Linux 2026 — msfconsole commands, exploit modules, payloads & your first real shell. Day 10 complete…
How Hackers Use theHarvester to Find Emails in Seconds (Most Don’t Know This)
Discover how hackers use theHarvester to harvest real employee emails from public sources in seconds — the OSINT technique most…
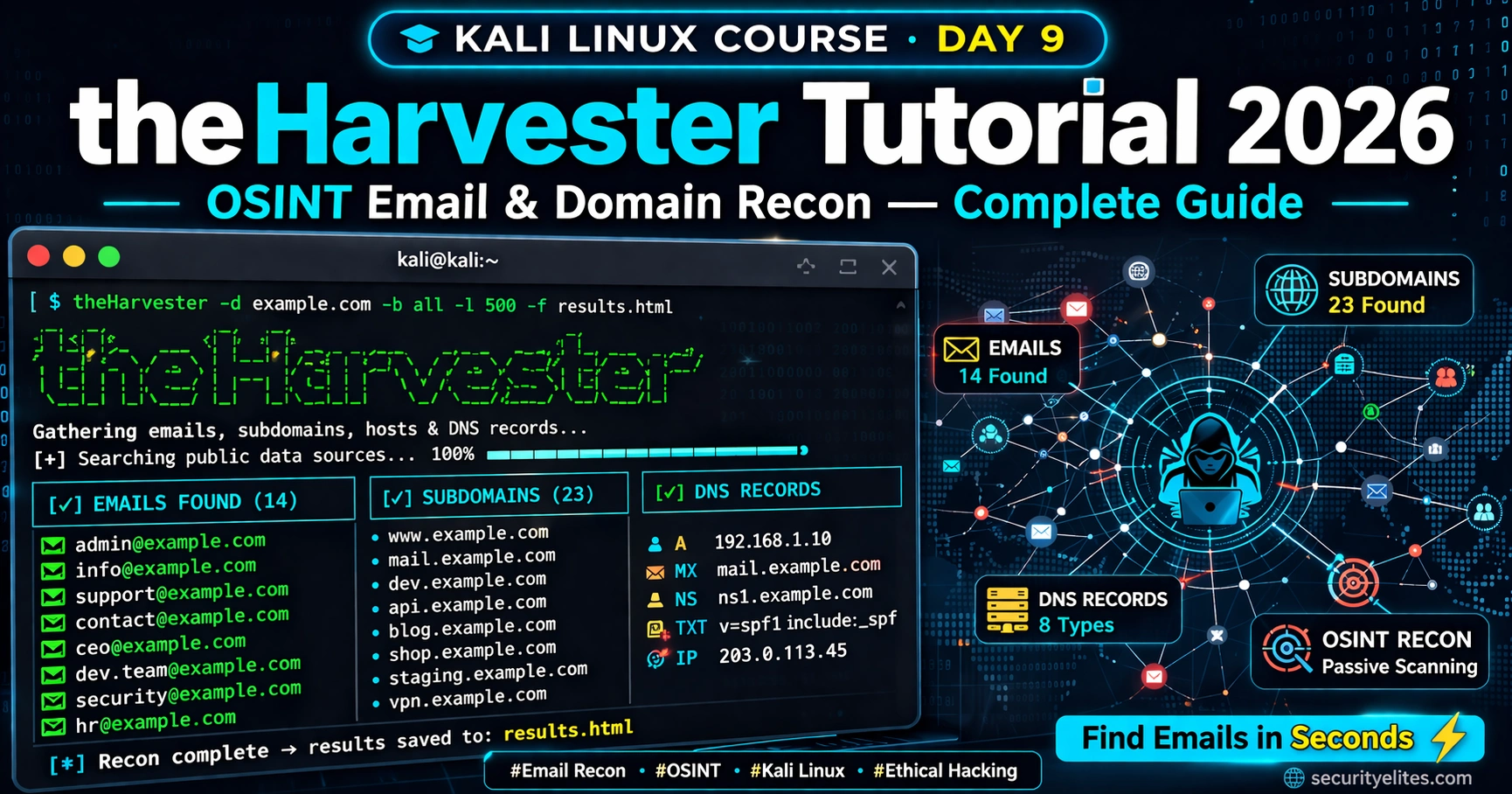
Kali Linux Day 9 : theHarvester Tutorial 2026 — OSINT Email & Domain Recon Complete Guide
Master theHarvester in Kali Linux 2026 — collect emails, subdomains & DNS records for OSINT recon. Complete Day 9 guide…
Cloud Security Hacking 2026 — How Attackers Exploit AWS, Azure & GCP (Ethical Hacker’s Guide)
Cloud security hacking is the highest-demand offensive skill of 2026. Learn IAM misconfiguration exploitation, S3 bucket attacks, SSRF to cloud…
Prompt Injection Attack & LLM Hacking 2026 — How Hackers Attack AI Systems (Complete Guide)
Prompt injection attack is OWASP’s #1 AI vulnerability. Learn how hackers exploit LLMs through direct injection, indirect attacks, data exfiltration,…
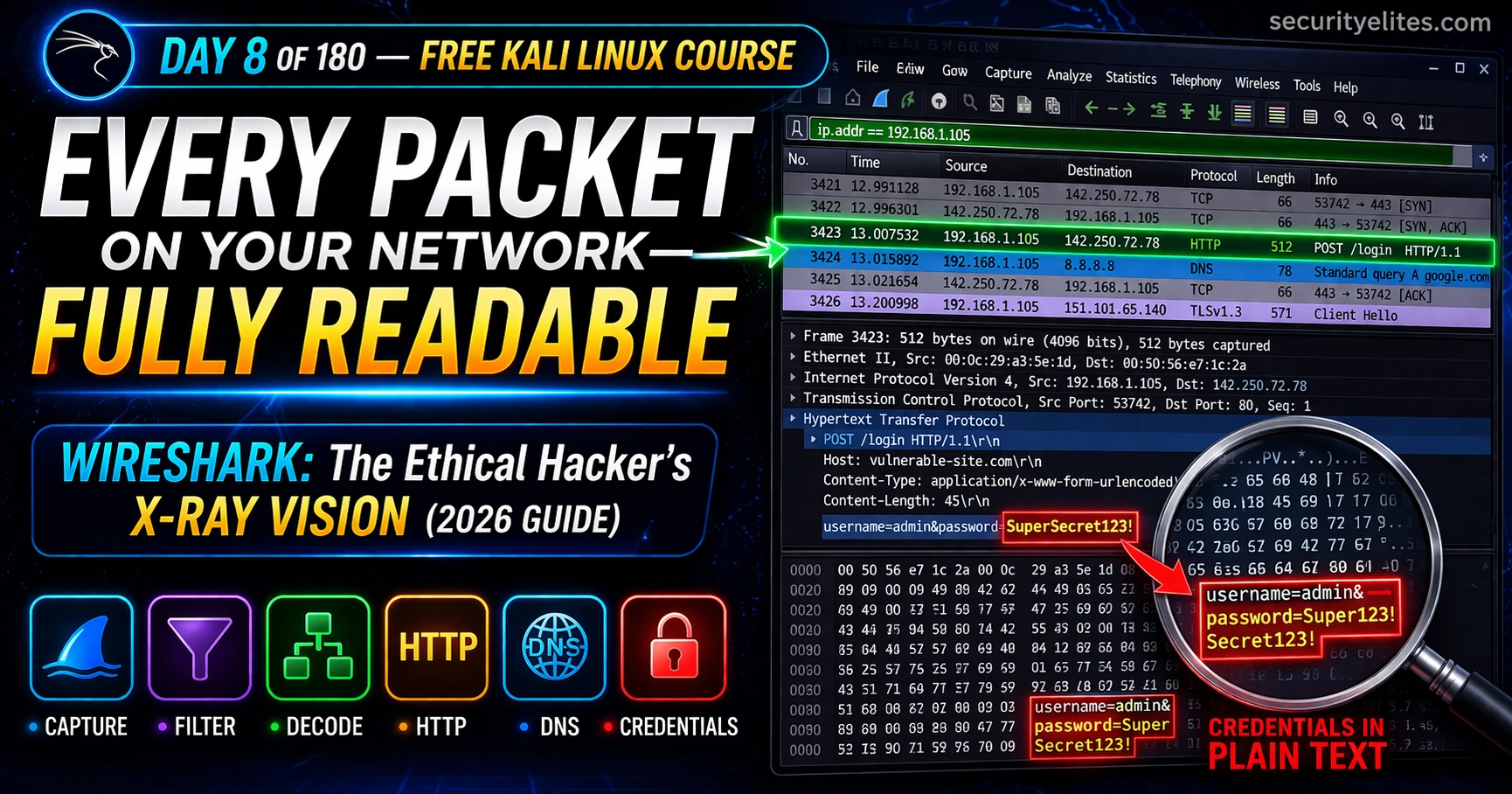
Kali Linux Day 8: Wireshark Tutorial 2026 — Capture & Analyse Real Network Traffic (Complete Guide)
Day 8 of 180. Wireshark Tutorial on Kali Linux from scratch — capture live network traffic, analyze PCAP files, apply…
Kali Linux Day 7: SQLmap Tutorial (2026) — Automate SQL Injection Like a Pro 🔥
Complete SQLmap tutorial for Kali Linux — detect SQL injection, enumerate databases, extract tables, dump credentials, use Burp request files,…
Kali Linux Day 6: Nikto Tutorial (Kali Linux 2026): Find CRITICAL Web Server Vulnerabilities in Minutes
Complete Nikto tutorial for Kali Linux: learn basic scans, HTTPS testing, output formats, tuning categories, evasion techniques, authentication, and a…