Exploitation
Exploitation involves leveraging discovered vulnerabilities to gain unauthorized system access in controlled ethical hacking environments. This section includes hands-on tutorials using frameworks like Metasploit, manual exploit execution, payload delivery, and reverse shell creation. Learn how vulnerabilities are weaponized, how exploits are tested, and how organizations can defend against real-world cyber attacks.
43 articles
How Hackers Exploit Bluetooth Devices in 2026 — Bluejacking, Bluesnarfing & BIAS Attacks
How hackers exploit Bluetooth in 2026 — bluejacking, bluesnarfing, BIAS authentication bypass, BLE attacks, and how to protect your devices.…
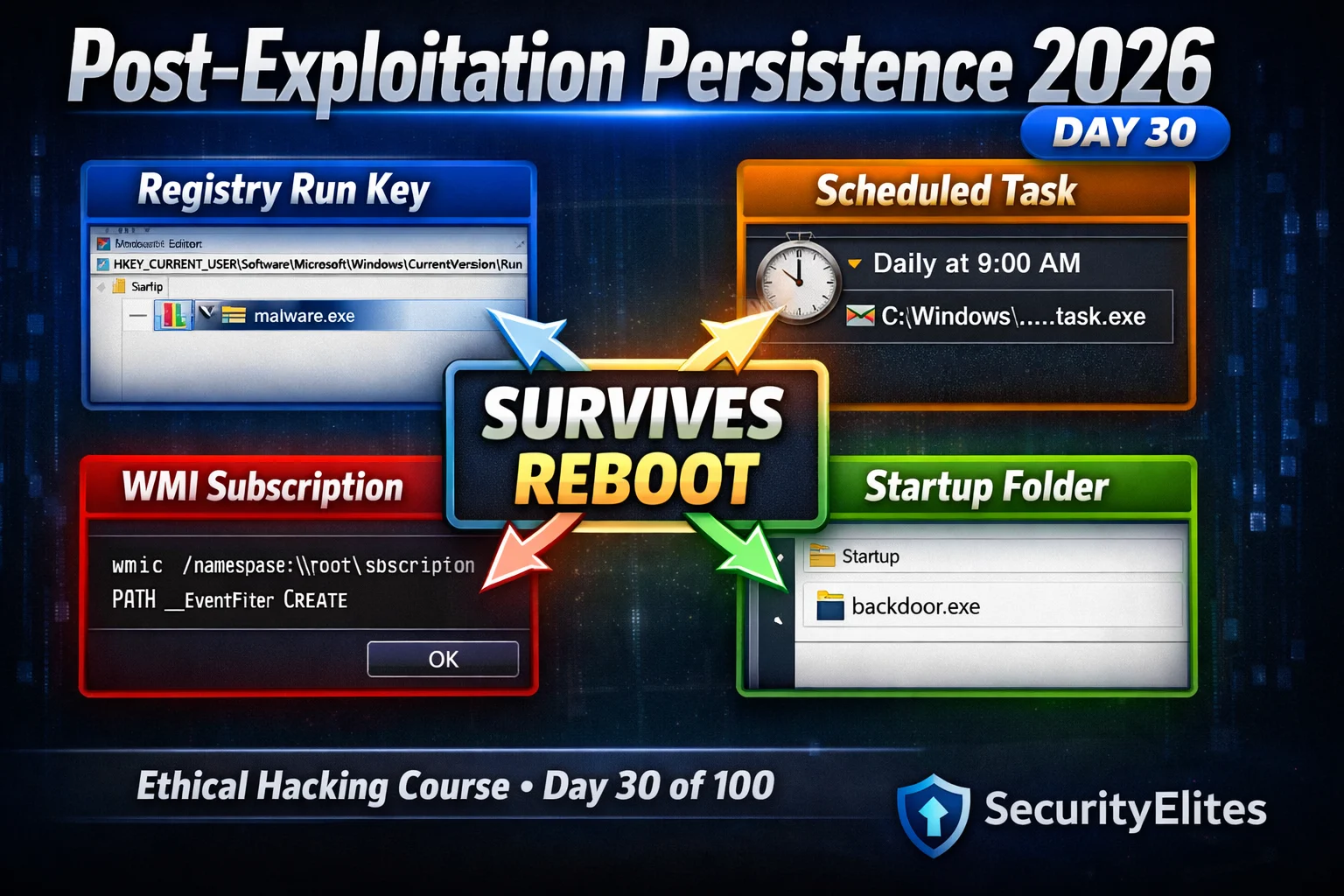
Post Exploitation Persistence 2026 — Registry, Startup Folders & WMI Subscriptions | Hacking Course Day30
Post exploitation persistence 2026 — maintain access to compromised Windows systems using registry run keys, startup folders, scheduled tasks and…
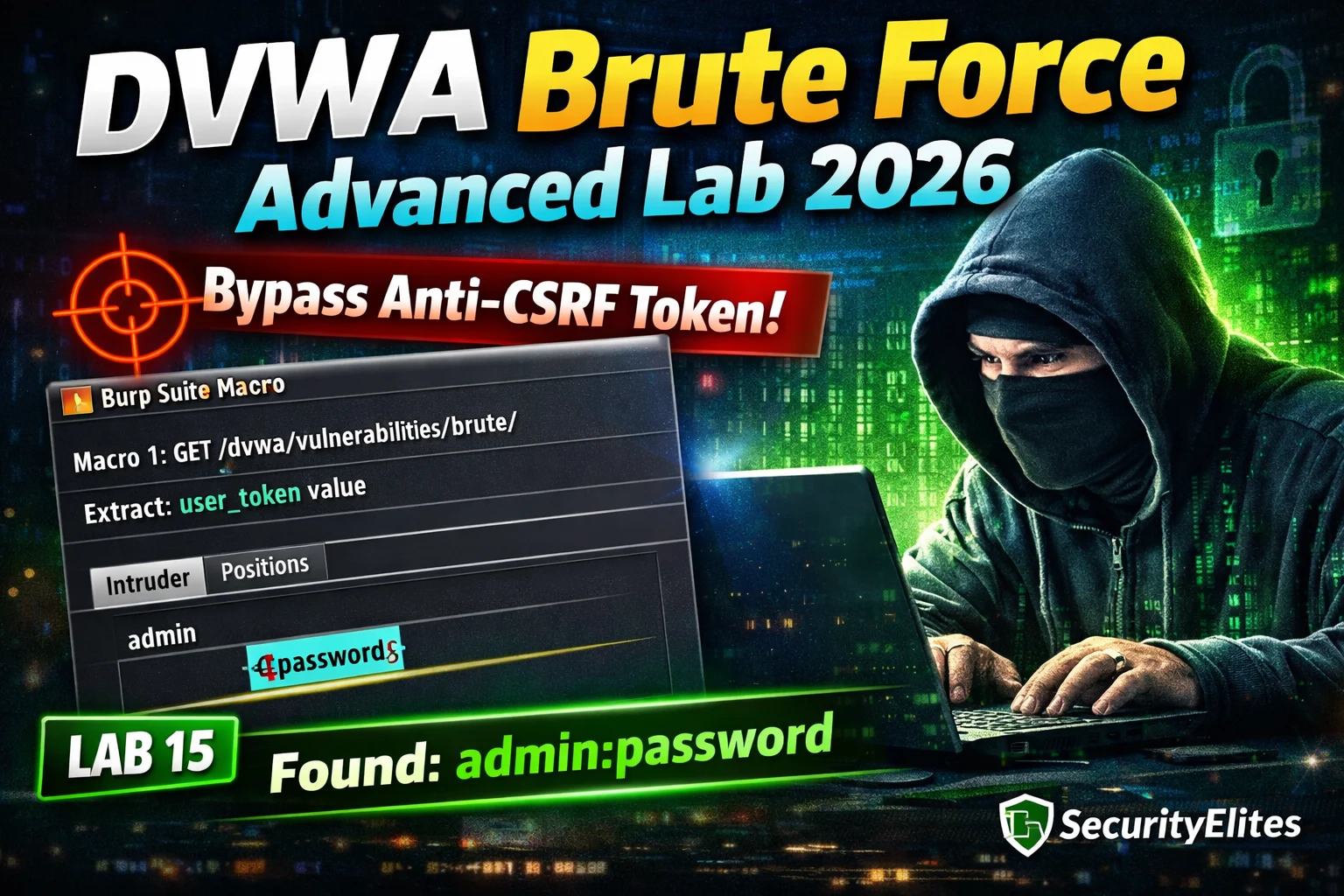
DVWA Brute Force Advanced Lab 2026 — Anti-CSRF Token Bypass Complete Walkthrough | Hacking Lab15
DVWA brute force advanced lab 2026 — bypass anti-CSRF token protection at High security using Burp Suite macros to extract…
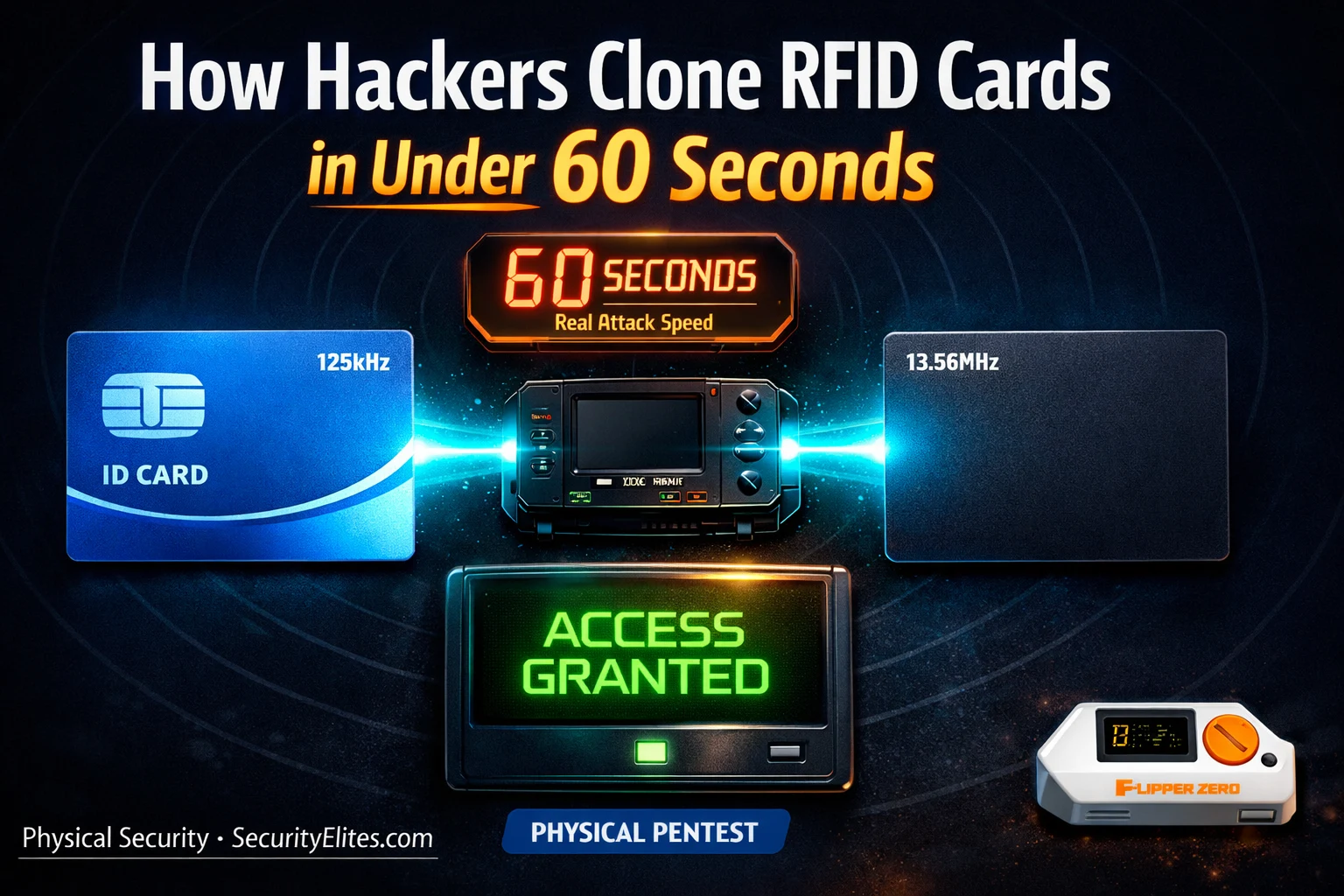
How Hackers Clone RFID Cards in Under 60 Seconds — The Hardware They Use
How hackers clone rfid cards 2026 — the real hardware and software used to copy access cards, hotel key cards…
Day 25: Kerberoasting 2026 — Attack & Defend Service Account Passwords in Active Directory
Master Kerberoasting in 2026 — request Kerberos service tickets, extract TGS hashes, crack offline with Hashcat, and detect attacks as…
Kali Linux Day 10 : Metasploit Tutorial Kali Linux 2026 — msfconsole, Modules & First Exploit Complete Guide
Master Metasploit in Kali Linux 2026 — msfconsole commands, exploit modules, payloads & your first real shell. Day 10 complete…
North Korea Just Poisoned the Axios npm Package — Here’s Exactly How a Supply Chain Attack Works (2026)
Google attributed the Axios npm supply chain attack to North Korean group UNC1069. Millions of developers affected. Here's exactly how…
Browser-Based Attacks 2026 — AITM Phishing, ClickFix and Session Hijacking Are Driving the Biggest Breaches Right Now (Complete Guide)
AITM phishing, ClickFix malware and session hijacking are behind today's biggest corporate breaches. Here's exactly how browser-based attacks works and…
Cisco CVE-2026-20093 — CVSS 9.8 Authentication Bypass Explained: How Hackers Get Admin Access Without a Password (2026)
Cisco patched Cisco CVE-2026-20093 authentication bypass, a CVSS 9.8 critical flaw letting unauthenticated attackers bypass authentication and gain admin access.…