Part of the 100-Day Ethical Hacking Course
🎯 What You’ll Master in Day 30
⏱️ 50 min read · 3 exercises
📋 What You’ll Master — Post-Exploitation Persistence 2026
In Day 29 you exfiltrated data through DNS tunneling and HTTPS channels. Day 30 completes the post-exploitation phase — after collecting and exfiltrating data, persistence ensures the attacker can return. The kill chain is now fully demonstrated: initial access → lateral movement → data collection → exfiltration → persistence. This is the complete story a penetration test tells in the 100-Day Ethical Hacking Course.
Why Persistence Matters in a Penetration Test
A finding of “we achieved Domain Admin” is a point-in-time demonstration. A finding of “we achieved Domain Admin and installed persistence mechanisms that would have maintained access indefinitely without re-exploitation” is a fundamentally different risk statement. The first shows the initial access path was open. The second shows the organisation would have been compromised for weeks or months while the vulnerability was being discovered and patched. Persistence demonstrations directly inform the timeline risk section of executive-level penetration test reports.
⏱️ Time: 8 minutes · No tools required
explain your reasoning. Consider: privilege level, detection
risk, and long-term reliability.
SCENARIO A:
You have compromised a standard user workstation via phishing.
No admin privileges. EDR installed (CrowdStrike).
The user logs in daily at 09:00.
→ Which persistence mechanism? Admin required? Detection risk?
SCENARIO B:
You have compromised a Domain Controller with SYSTEM privileges.
The SOC monitors new registry Run keys via Windows Event Logs.
The target environment has no WMI repository monitoring.
→ Which persistence mechanism? Why WMI over registry?
SCENARIO C:
You need persistence that survives a user account password reset.
The compromised system has no admin access.
The organisation uses MDE (Microsoft Defender for Endpoint).
→ Which mechanism is LEAST likely to survive a password reset?
→ Which mechanism survives regardless of the user account state?
For each: Technique name, MITRE ATT&CK ID, admin required Y/N,
survives reboot Y/N, survives password reset Y/N.
📸 Share your three persistence strategy answers with MITRE IDs in #day-30-persistence on Discord.
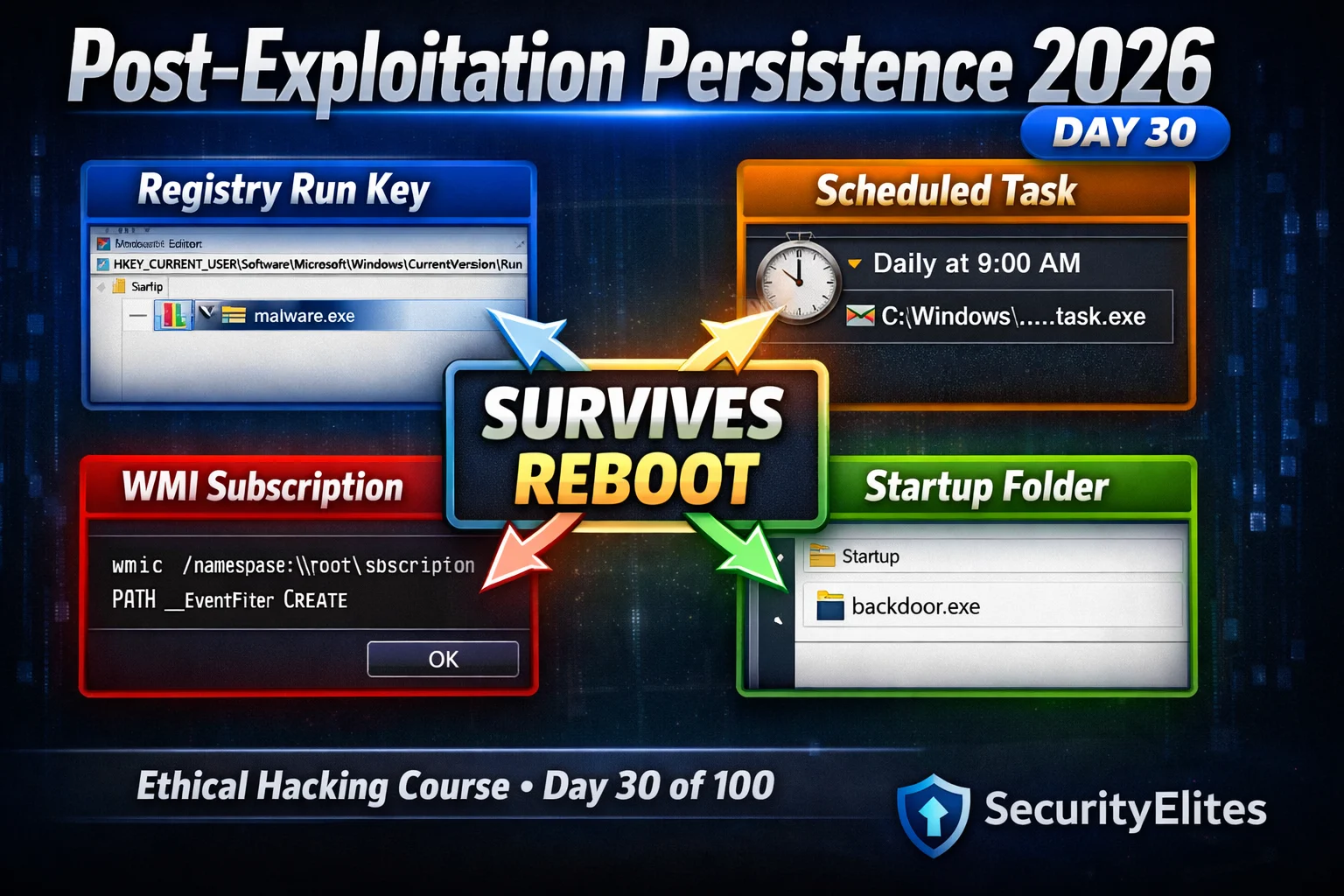
Registry Run Keys — T1547.001
Scheduled Tasks — T1053.005
WMI Event Subscriptions — T1546.003
WMI permanent event subscriptions are the most sophisticated Windows persistence technique available without kernel-level access. They use the Windows Management Instrumentation repository — a separate database completely distinct from the registry — to store three linked objects: an EventFilter (the trigger), an EventConsumer (the action), and a binding linking them. The payload executes entirely through the WMI subsystem, generating no new processes from suspicious parent processes, no registry Run key changes, and no scheduled task entries.
⏱️ Time: 25 minutes · Free TryHackMe account
Step 2: Search for “Windows Persistence” room
Open: “Windows Persistence” or “Windows Local Persistence”
room (these change names periodically — search the term)
Step 3: Deploy the machine and connect via VPN or AttackBox
Step 4: The room covers registry persistence — complete:
a) The registry Run key task (HKCU variant)
b) Verify the key persists by checking the registry
c) Note the Windows Event Log ID generated (if shown)
Step 5: Complete the startup folder task:
a) Place a payload in the per-user startup folder
b) Verify execution on next login
Step 6: If scheduled tasks are covered:
a) Create a task with a logon trigger
b) Verify it appears in Task Scheduler GUI
Step 7: For each mechanism, record:
– Exact command used
– Registry path OR file path
– MITRE ATT&CK technique ID
– Windows Event ID generated (if visible)
– How would a blue team analyst detect this?
📸 Screenshot completed persistence mechanisms and the detection Event IDs in #day-30-persistence on Discord.
Startup Folders and Services
⏱️ Time: 12 minutes · Kali + Windows lab target (Metasploit/Evil-WinRM shell)
📸 Screenshot Get-WMIObject output confirming the subscription exists and share in #day-30-persistence on Discord. Tag #persistence2026
Detection Artefacts — What Each Technique Leaves Behind
T1547.001
T1053.005
T1546.003
T1543.003
🧠 QUICK CHECK — Day 30
📋 Day 30 Persistence Reference Card
🏆 Mark Day 30 as Complete
You now have four Windows persistence techniques mapped to their MITRE ATT&CK IDs, understand which require admin, know the detection Event IDs for each, and can write professional blue team recommendations for all of them. Day 30 completes the post-exploitation arc: lateral movement (Day 28) → data exfiltration (Day 29) → persistence (Day 30).
❓ Frequently Asked Questions
What is post-exploitation persistence in penetration testing?
What is the most common Windows persistence technique?
What is WMI subscription persistence and why is it harder to detect?
Which persistence techniques work without administrator privileges?
What comes after persistence in the course?
Day 29: Data Exfiltration 2026
Day 31: Linux Privilege Escalation 2026
📚 Further Reading
- Data Exfiltration Techniques 2026 — Day 29 covers DNS tunneling, ICMP exfil, and living-off-the-land exfiltration — the phase immediately before persistence in the complete post-exploitation lifecycle.
- Lateral Movement Techniques 2026 — Day 28 covers PsExec, WMI, and DCOM lateral movement — the techniques that position you on the high-value hosts where persistence has maximum strategic value.
- 100-Day Ethical Hacking Course — The complete course hub — Day 30 persistence sits at the milestone of the post-exploitation phase, completing the attack chain from initial access through data theft to maintained access.
- MITRE ATT&CK — Persistence Tactic — The official MITRE ATT&CK Persistence tactic page listing all 19 technique groups including T1547 (Boot/Logon Autostart), T1053 (Scheduled Tasks), and T1546 (Event-Triggered Execution) with real-world procedure examples.
- PayloadsAllTheThings — Windows Persistence — Community-maintained comprehensive Windows persistence techniques reference — registry keys, startup locations, COM hijacking, DLL side-loading, and 30+ additional methods beyond the four covered today.