FREE
Part of the DVWA Lab Series — 30 Labs
🎯 What You’ll Learn in Lab 15
⏱️ 45 min · 3 Burp Suite exercises
✅ Prerequisites
- DVWA running locally (Lab 1: Setup Guide)
- Lab 2: Brute Force with Hydra — understand the Low/Medium approach first
- Lab 14: Security Levels Explained — understand how the CSRF token works in source code
- Burp Suite Community or Professional with proxy configured
📋 DVWA Brute Force Advanced Lab 15 Contents — Anti-CSRF Brute Force Bypass
In Lab 14 you analysed the High security CSRF token source code — the md5(uniqid()) generation and per-request session validation. Lab 15 applies that understanding directly: you know where the token lives in the HTML and how it is validated, which is everything you need to configure the macro. The DVWA Lab Series is sequenced so each lab builds on the previous.
Why Standard Brute Force Fails at High Security
At Low and Medium security, the DVWA brute force form has no CSRF token. Tools like Hydra and Burp Intruder can send login attempts as-is — each request is independent. At High security, a hidden user_token field is added to the form. The server generates a unique token for each page load, stores it in the session, and validates that the submitted token matches when the form is submitted. A token that was valid for the last request is invalid for the current one.
⏱️ Time: 8 minutes · DVWA at High security · Burp Suite active
📸 Screenshot the Repeater showing the static token and identical response lengths in Intruder. Share in #dvwa-labs on Discord.
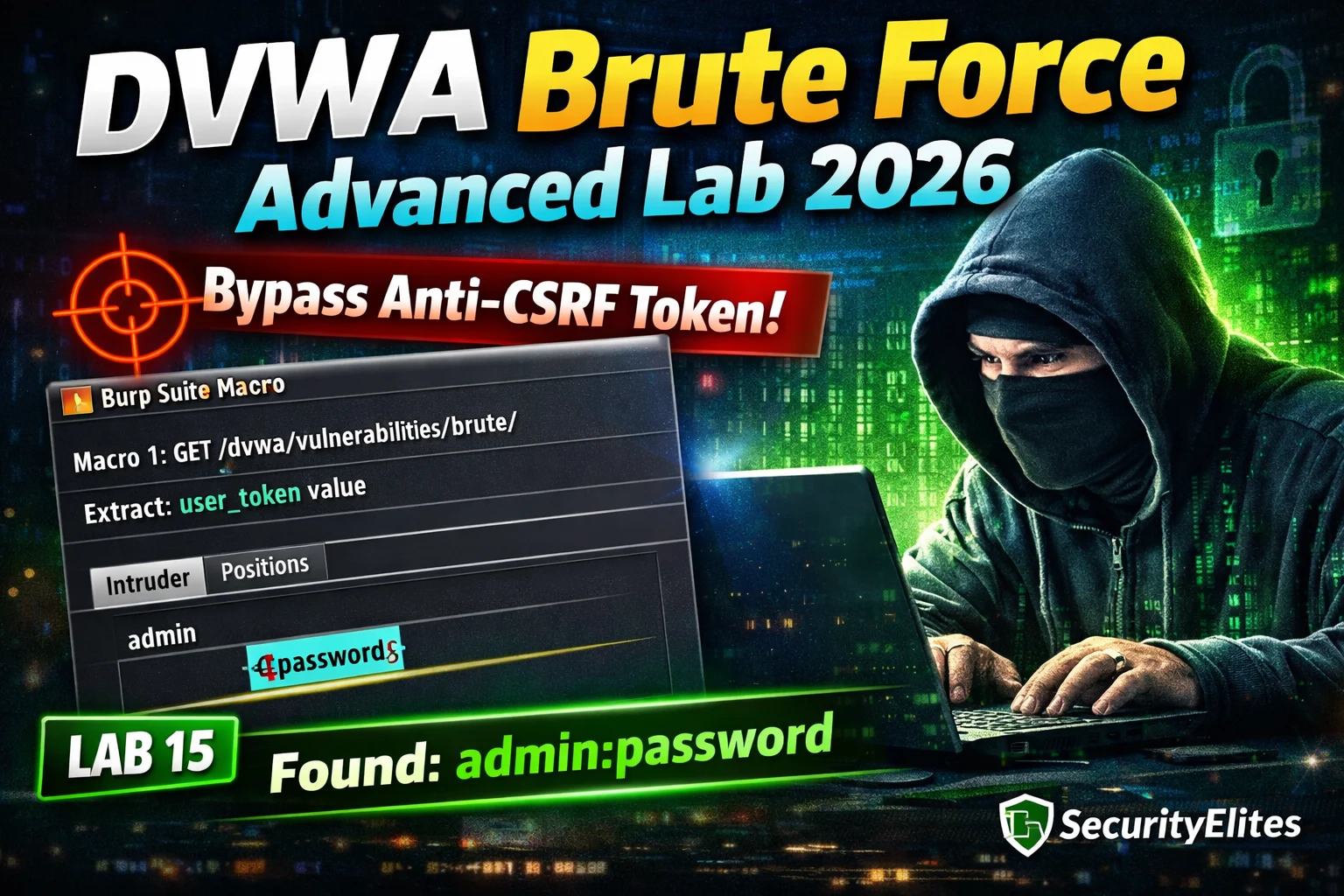
Configuring the Burp Macro — Token Extraction
A Burp macro is a recorded sequence of HTTP requests that Burp replays automatically. For this lab, the macro is a single GET request to the brute force page that extracts the user_token hidden field value from the HTML response. The Session Handling Rule then injects that fresh value into the POST body before each Intruder request fires.
⏱️ Time: 20 minutes · Burp Suite open · DVWA High security
📸 Screenshot the “Test macro” result showing user_token successfully extracted. Share in #dvwa-labs on Discord.
Session Handling Rule — Applying the Macro to Intruder
The Session Handling Rule is the bridge between the macro and Intruder. Without it, Burp knows how to extract the token but does not know when to do so or where to put it. The rule says: before every Intruder request to this URL, run the macro and replace the user_token parameter in the request with the freshly extracted value. The result is that every single Intruder payload gets sent with a valid, current token.
Running the Attack — Successful CSRF Bypass
⏱️ Time: 12 minutes · Macro configured from Exercise 2
📸 Screenshot Intruder results showing the different response length for admin:password. Share in #dvwa-labs on Discord. Tag #dvwabrute2026
🧠 QUICK CHECK — Lab 15
📋 Lab 15 Key Takeaways
🏆 Mark Lab 15 as Complete
Lab 15 is the most advanced Burp Suite technique in the DVWA series. Macros and session handling rules apply far beyond DVWA — any real application with CSRF-protected authentication forms can be tested using this exact approach. This is a professional-grade skill used in real penetration testing engagements.
❓ Frequently Asked Questions
What is anti-CSRF token brute force protection?
What is a Burp Suite Macro?
Why does standard Hydra fail against DVWA High security?
What is the token parameter name in DVWA High security?
Why must Intruder run at 1 thread with macros?
What comes after Lab 15?
Lab 14: DVWA Security Levels Explained
Lab 16: DVWA Command Injection Advanced
📚 Further Reading
- DVWA Security Levels Explained 2026 — Lab 14 reveals the exact PHP source for the CSRF token generation — understanding md5(uniqid()) and session validation is the prerequisite for configuring the Lab 15 macro extraction correctly.
- DVWA Brute Force Lab 2026 — Lab 2 covers Hydra and Burp Intruder against Low/Medium security — the baseline brute force skills that Lab 15 extends to defeat CSRF token protection at High security.
- DVWA Labs Hub — All 30 DVWA labs in sequence — Lab 15 is the halfway milestone at 50%, and the Burp macro skills learned here apply directly to upcoming web application testing labs.
- Burp Suite Macros — Official Documentation — PortSwigger’s official macro documentation covering all configuration options, response extraction methods, regex vs cursor selection, and session handling rule integration for complex authentication flows.
- PortSwigger — Password-Based Authentication Labs — PortSwigger Web Academy authentication labs that apply CSRF token bypass in real web application contexts — the natural next step after mastering the technique on DVWA.