Exploitation
Exploitation involves leveraging discovered vulnerabilities to gain unauthorized system access in controlled ethical hacking environments. This section includes hands-on tutorials using frameworks like Metasploit, manual exploit execution, payload delivery, and reverse shell creation. Learn how vulnerabilities are weaponized, how exploits are tested, and how organizations can defend against real-world cyber attacks.
43 articles
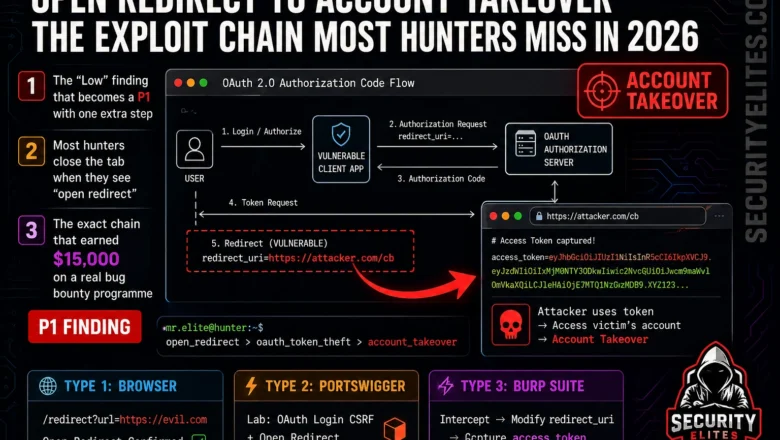
Open Redirect to Account Takeover — The Exploit Chain Most Hunters Miss in 2026
Learn the complete open redirect to account takeover exploit chain in 2026. OAuth token theft, phishing bypass, and SSRF chaining…
AI Hallucination Attacks 2026: Real Exploits, Slopsquatting & CVE Abuse
Learn how AI hallucination attacks work in 2026, including slopsquatting, fake CVEs, and adversarial prompts. Real attack techniques explained.
Social Engineering Scripts for Pentesters 2026 — Phishing, Vishing & Pretexting Playbooks
Real social engineering scripts for pentesters in 2026. Phishing lures, vishing call scripts, pretexting playbooks and SET automation used on…
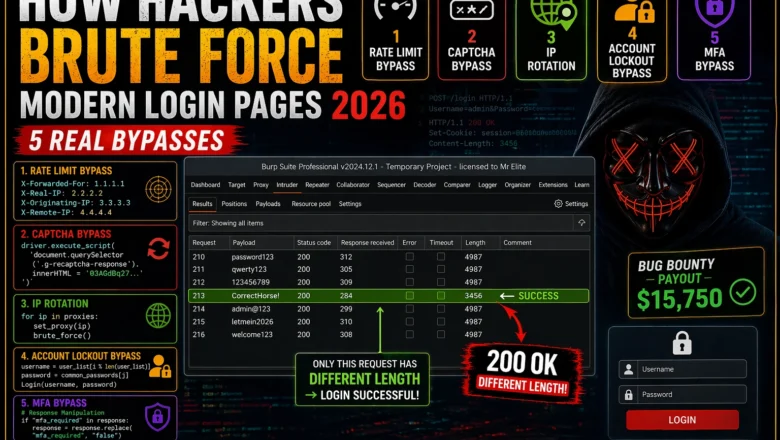
How Hackers Brute Force Modern Login Pages — 5 Real Bypasses (2026)
How hackers brute force modern login pages in 2026 — bypass rate limiting, CAPTCHA, account lockout, MFA, and IP rotation…
How Ethical Hackers Break Into Smart Locks — Real Techniques Explained (2026)
How hackers break smart locks in 2026 — BLE replay attacks, Flipper Zero cloning, firmware extraction, rolling code bypass and…
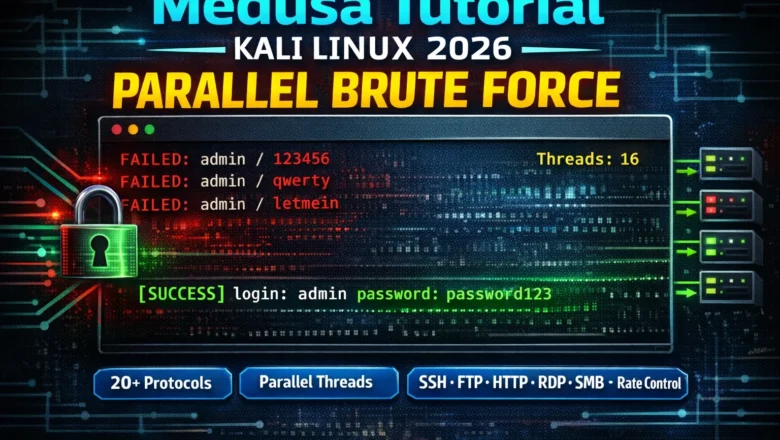
Medusa Tutorial Kali Linux 2026 — Parallel Brute Force for SSH, FTP, HTTP & 20+ Protocols | Tools Day20
Medusa tutorial Kali Linux 2026 — master parallel login brute force across SSH, FTP, HTTP, RDP, SMB and 20+ protocols.…
Windows Privilege Escalation 2026 — WinPEAS, AlwaysInstallElevated, Token Impersonation | Hacking Course Day 32
Windows privilege escalation 2026 — WinPEAS enumeration, AlwaysInstallElevated MSI exploit, unquoted service paths, weak service permissions, token impersonation with GodPotato.…
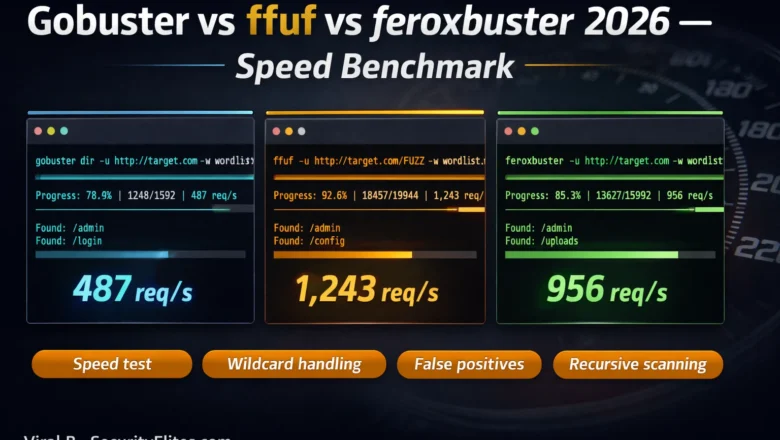
Gobuster vs ffuf vs feroxbuster — Speed & Accuracy Benchmark 2026
Gobuster vs ffuf vs feroxbuster 2026 — side-by-side speed and accuracy benchmark. Which directory fuzzer wins on speed, false positives,…
Meterpreter Commands Cheat Sheet 2026 — 50+ Commands With Real Examples
Complete Meterpreter commands cheat sheet 2026. Every essential Meterpreter command with real examples — system recon, file operations, privilege escalation,…