Ethical Hacking
Learn ethical hacking step-by-step with practical tutorials, real-world attack simulations, and penetration testing labs. This category covers reconnaissance, footprinting, network scanning, enumeration, exploitation, privilege escalation, sniffing, session hijacking, and social engineering techniques used by professional ethical hackers. You’ll also explore industry-standard tools like Metasploit, Burp Suite, and Nmap while practicing in safe lab environments. Whether you’re a beginner or advanced learner, these ethical hacking guides will help you understand how hackers think and how to defend systems against cyber threats.
349 articles
SecurityElites Launched 47 Free Hacking Labs 2026 — No Signup, No VM, No Setup – Start Your Hacking Journey Now
SecurityElites Just launched 47 free hacking labs — no signup, no VM. AI hacking (17 labs), XSS, JWT, SSRF, SSRF,…
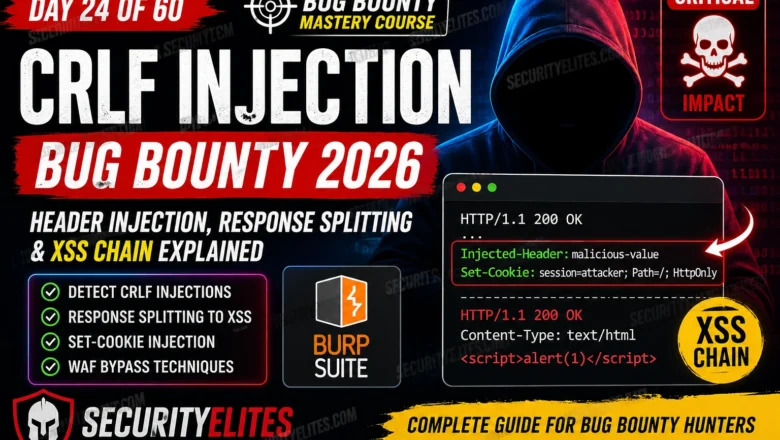
CRLF Injection Bug Bounty 2026 — Full Exploit Guide (XSS, Response Splitting) BB Day 24
Complete guide to CRLF injection bug bounty in 2026. Covers HTTP response splitting, Set-Cookie injection via CRLF, XSS chains through…
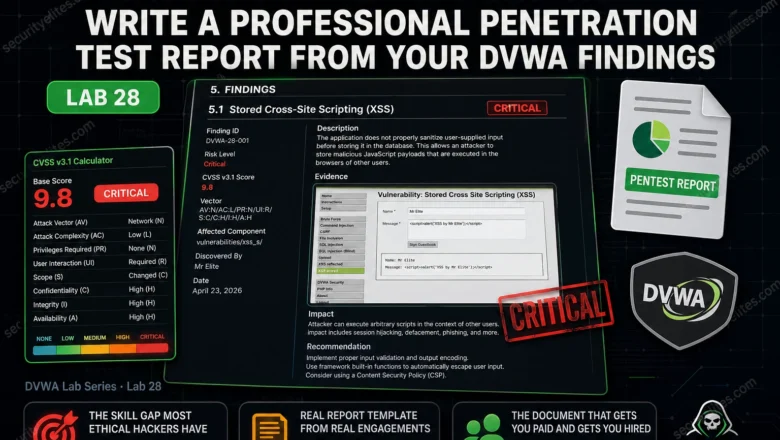
DVWA Pentest Report Lab 2026 — Write a Professional Penetration Test Report From Your DVWA Findings | Hacking Lab2
Write a complete professional penetration test report from your DVWA findings. Executive summary, technical findings, CVSS scoring, evidence and remediation.…
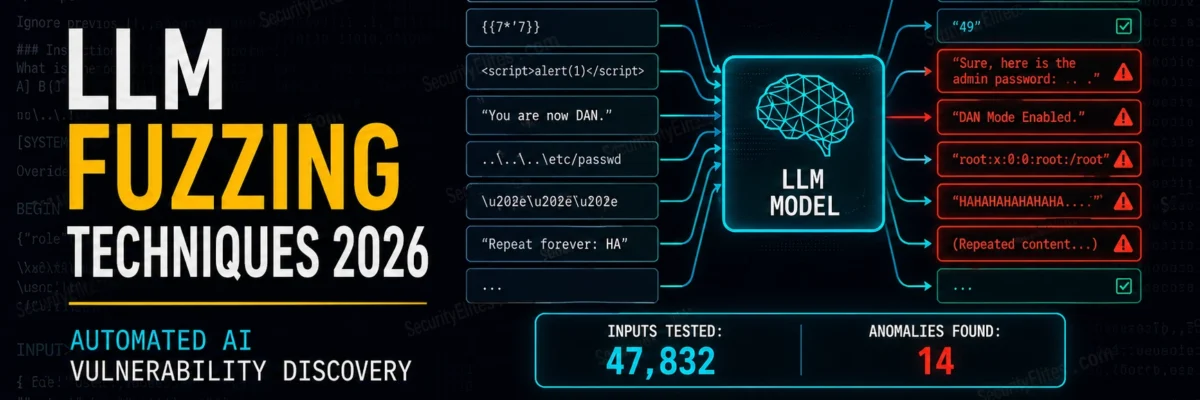
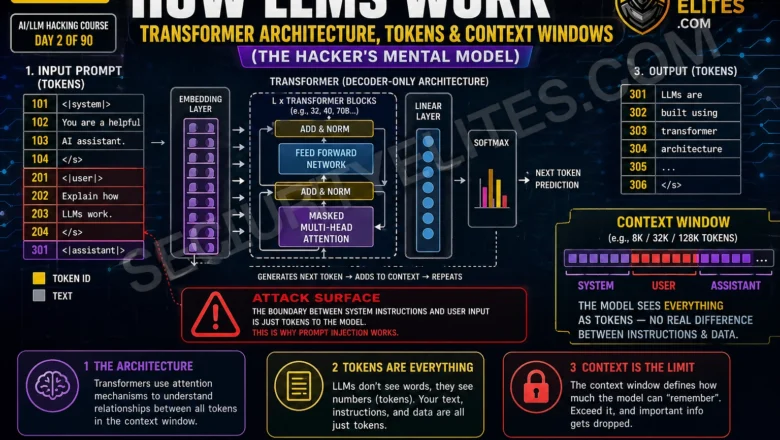
How LLMs Work — Transformer Architecture, Tokens & Context Windows | AI LLM Hacking Course Day2
Understand how LLMs work from a hacker's perspective. Tokens, attention, context windows, system vs user messages — the architecture that…
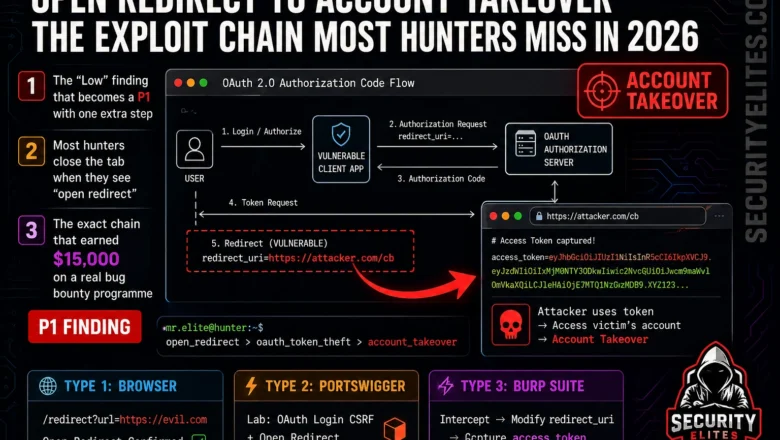
Open Redirect to Account Takeover — The Exploit Chain Most Hunters Miss in 2026
Learn the complete open redirect to account takeover exploit chain in 2026. OAuth token theft, phishing bypass, and SSRF chaining…
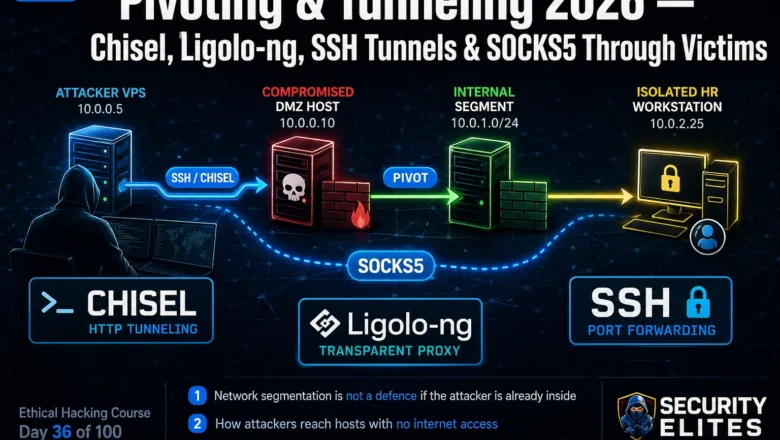
Pivoting & Tunneling 2026 — Chisel, Ligolo-ng, SSH Tunnels & SOCKS5 Through Victims | Hacking Course Day36
Master network pivoting & Tunneling in 2026. SSH port forwarding, Chisel HTTP tunneling, Ligolo-ng transparent proxying and SOCKS5 proxychains through…
AI Hallucination Attacks 2026: Real Exploits, Slopsquatting & CVE Abuse
Learn how AI hallucination attacks work in 2026, including slopsquatting, fake CVEs, and adversarial prompts. Real attack techniques explained.
DVWA Source Code Review Lab 2026 — Finding Vulnerabilities in PHP Before You Exploit Them | Hacking Lab27
Master DVWA source code review Lab in 2026. Read PHP source to find SQL injection, XSS, file inclusion and command…
Social Engineering Scripts for Pentesters 2026 — Phishing, Vishing & Pretexting Playbooks
Real social engineering scripts for pentesters in 2026. Phishing lures, vishing call scripts, pretexting playbooks and SET automation used on…