Ethical Hacking
Learn ethical hacking step-by-step with practical tutorials, real-world attack simulations, and penetration testing labs. This category covers reconnaissance, footprinting, network scanning, enumeration, exploitation, privilege escalation, sniffing, session hijacking, and social engineering techniques used by professional ethical hackers. You’ll also explore industry-standard tools like Metasploit, Burp Suite, and Nmap while practicing in safe lab environments. Whether you’re a beginner or advanced learner, these ethical hacking guides will help you understand how hackers think and how to defend systems against cyber threats.
349 articles
Post-Quantum Cryptography — What Security Teams Must Do Before It’s Too Late
Post-quantum cryptography. Why harvest-now-decrypt-later attacks are already happening, what NIST PQC standards mean for your organisation, and the migration timeline.
How to Extract a System Prompt Using Advanced Techniques in 2026 | Day 18
Master How to extract a system system prompt using Advanced Techniques in 2026. 15 ranked techniques, model resistance profiling, Burp…
How to Use Burp Suite for LLM Security Testing | Day17
Use Burp Suite for LLM security testing in 2026. Intercept AI API traffic, manipulate prompts in the proxy, build custom…
AI Security Posture Management – The Security Tool Every Organisation Needs
What is AI-SPM? AI Security Posture Management explained — what it monitors, how it differs from CSPM, the top tools…
How to Build an Automated Prompt Injection Testing Pipeline | Day 16
Build automated prompt injection testing pipelines in 2026. Payload libraries, multi-model scanning, rate-aware fuzzing and evidence collection — Day 16…
Metasploitable vsftpd Backdoor Lab — CVE-2011-2523 Exploit Guide
Exploit vsftpd 2.3.4 backdoor on Metasploitable 2026. CVE-2011-2523 manual exploitation, Metasploit module, root shell verification and remediation. Lab 5 guide.
Linux Sudo Privilege Escalation Methods — 7 Techniques + GTFOBins Guide
Linux sudo privilege escalation methods 2026. NOPASSWD abuse, sudo -l enumeration, GTFOBins, LD_PRELOAD, env_keep exploits, wildcards and sudo version CVEs.
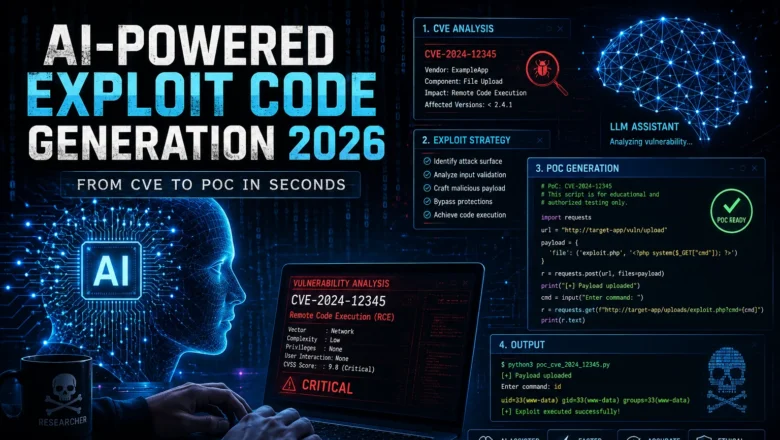
AI-Powered Exploit Code Generation — From CVE to PoC in Seconds
AI-powered exploit code generation. How LLMs assist security researchers creating proof-of-concept code, from CVE analysis to PoC drafting, limitations, and…
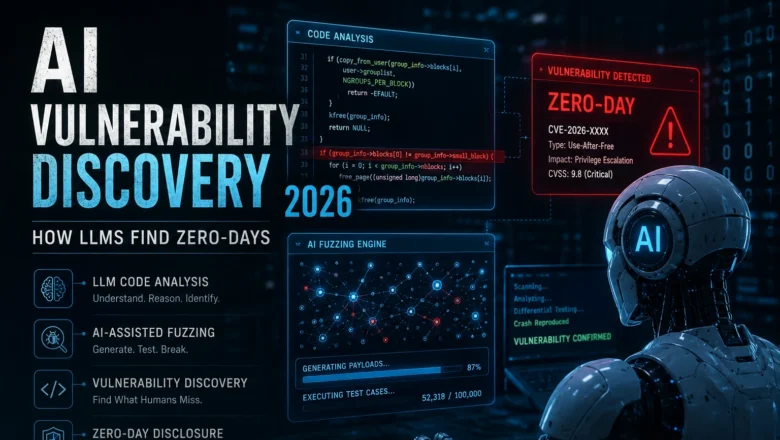
How AI and LLMs are discovering zero-days faster than human researchers in 2026
AI vulnerability discovery 2026. How LLMs and automated tools find zero-days faster than human researchers, AI-assisted fuzzing, code analysis pipelines,…