Cyber Security Tools
Discover the most powerful cyber security tools and ethical hacking tools used by penetration testers and security researchers. This category features detailed tutorials, installation guides, and usage walkthroughs for reconnaissance, exploitation, OSINT, wireless testing, and password cracking tools. Explore both free and premium security tools, compare their features, and learn how to use them effectively in real penetration testing scenarios.
81 articles
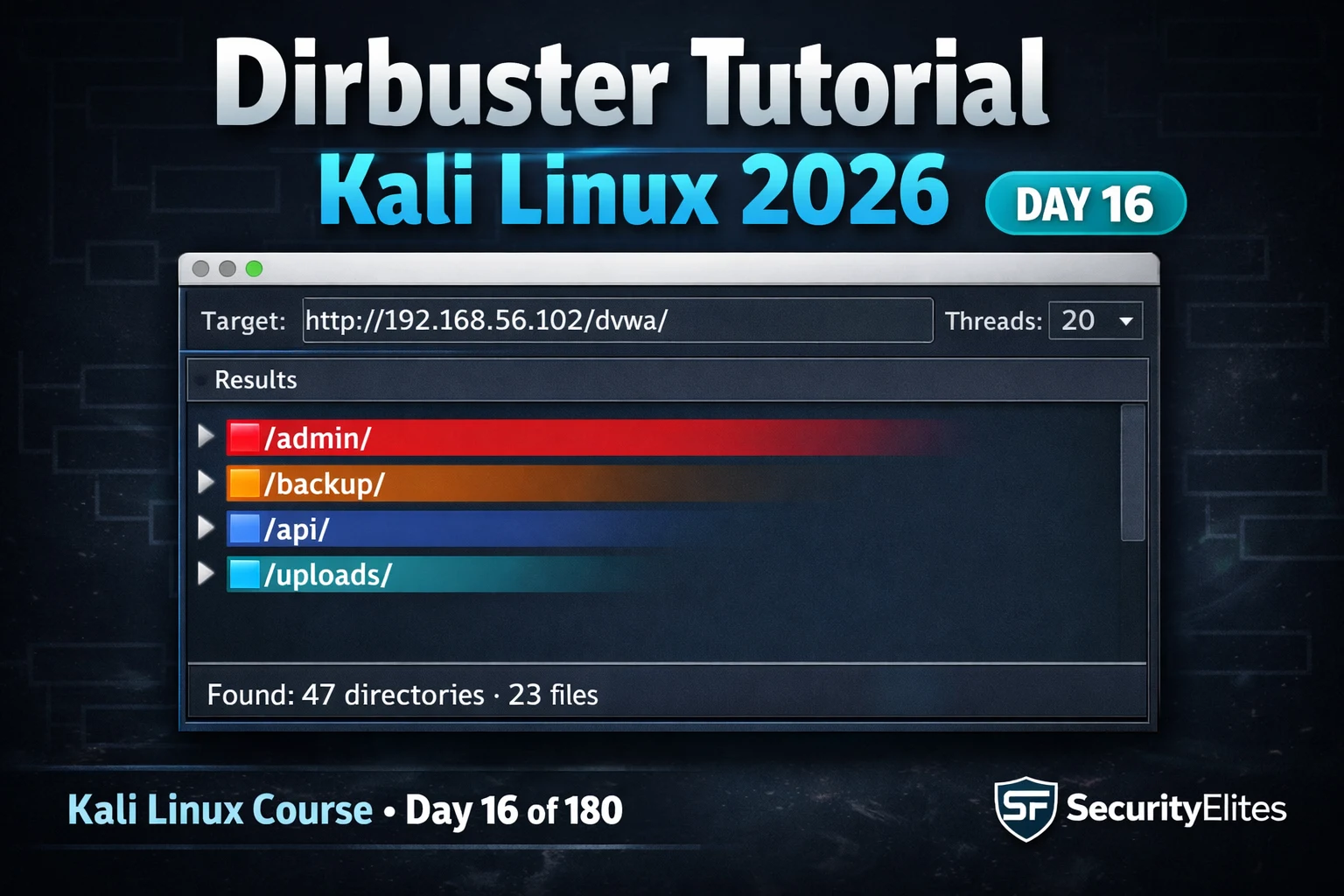
Kali Linux Day16: Dirbuster Tutorial Kali Linux 2026 — GUI Directory Brute Force & Hidden File Discovery
Dirbuster tutorial kali linux 2026 — use DirBuster GUI to brute force hidden directories and files on web servers. Day…
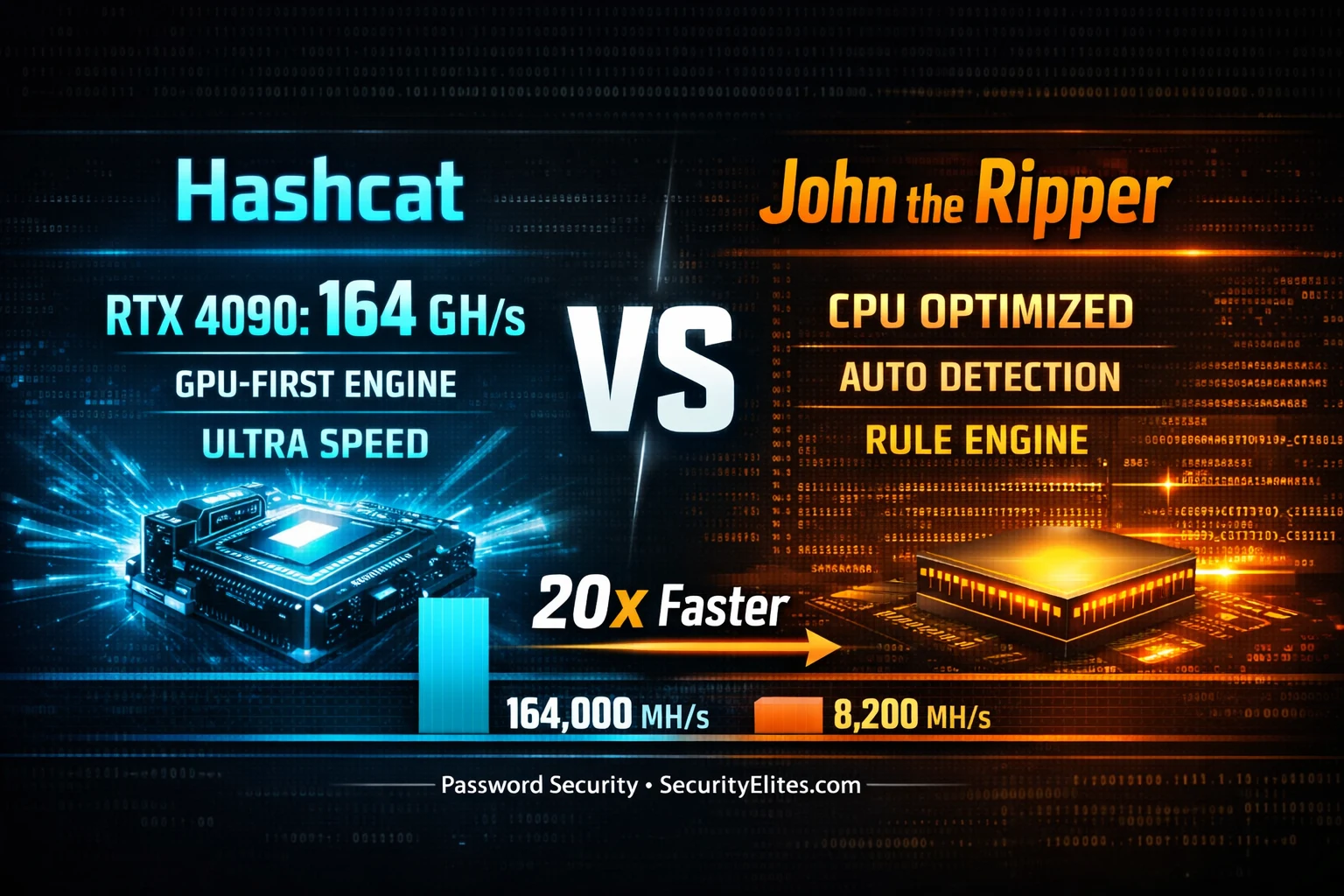
Hashcat vs John the Ripper 2026 — The 20x Speed Gap No One Talks About
Hashcat vs John the Ripper 2026 — real benchmark comparison on GPU vs CPU for MD5, NTLM, bcrypt and SHA256.…
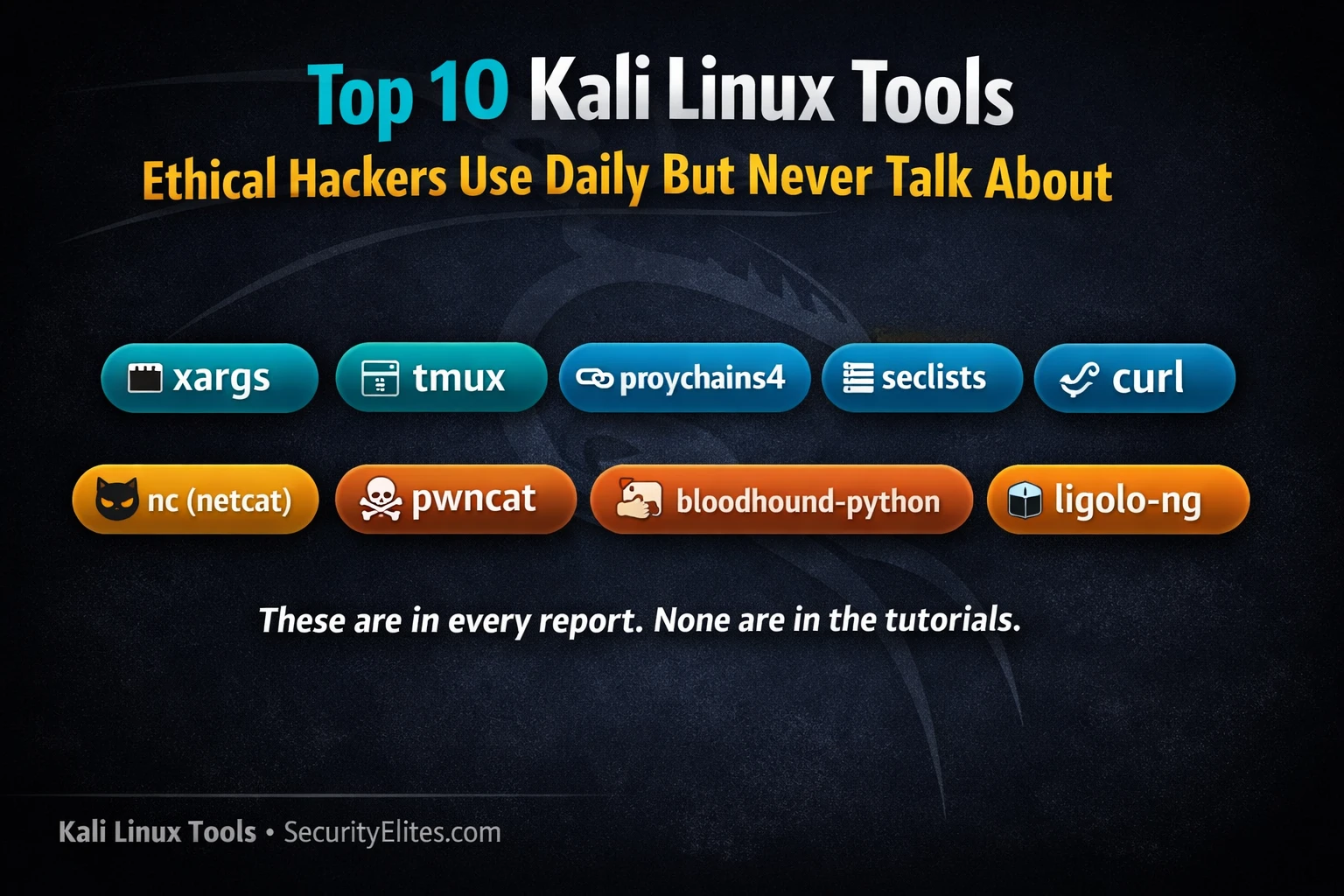
Top 10 Kali Linux Tools Ethical Hackers Use Daily But Never Talk About
Top 10 Kali tools ethical hackers use every single day — but almost nobody writes about them. The unsung tools…
How to Use Shodan 2026 — The Hacker’s Search Engine Complete Guide
How to use shodan 2026 — search internet-connected devices, find exposed services, use Shodan dorks for bug bounty recon and…
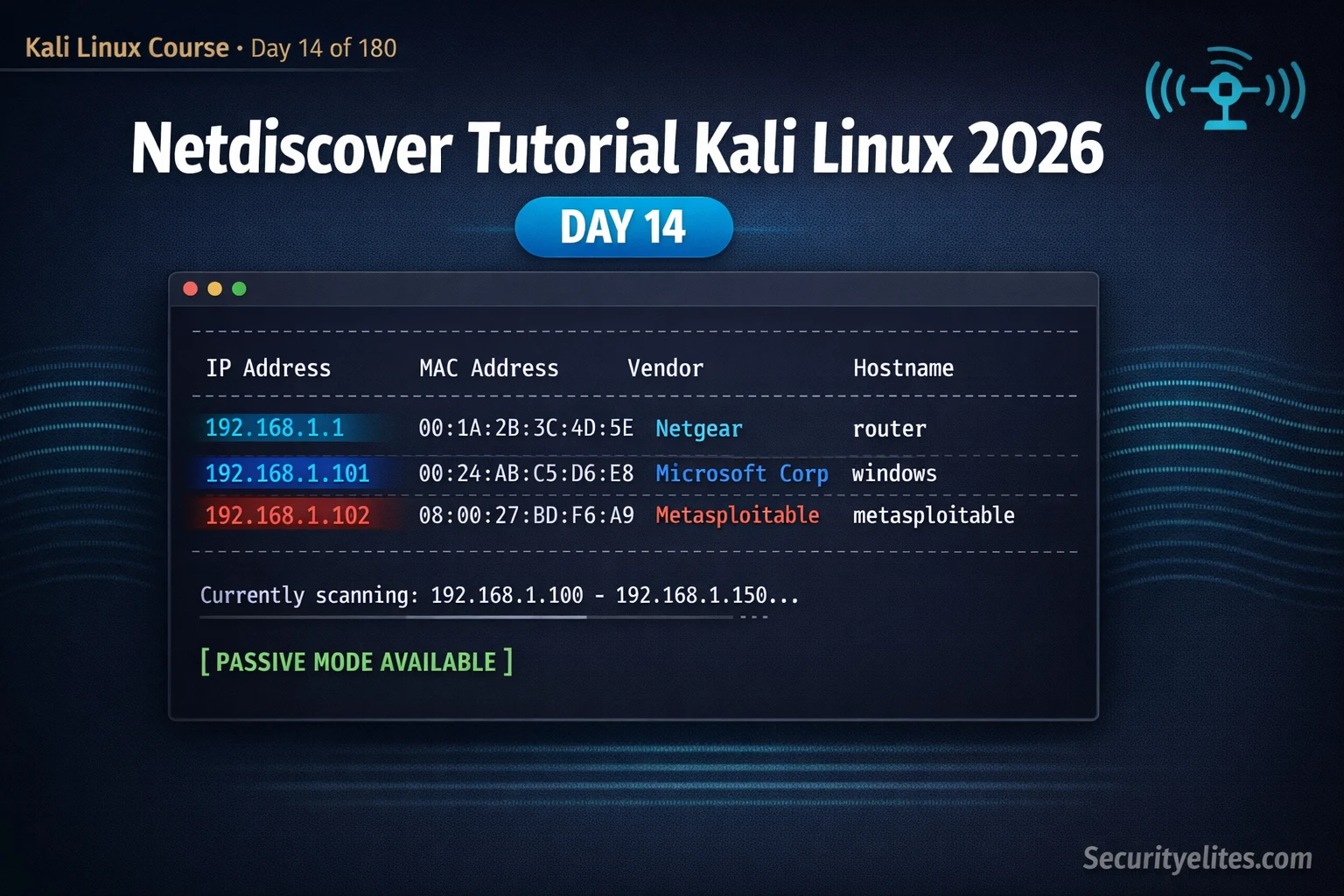
Kali Linux Day14: Netdiscover Tutorial Kali Linux 2026 — Instantly Discover Every Device on Your Network
Netdiscover tutorial kali linux 2026 — discover live hosts on local networks using ARP scanning, passive mode and IP range…
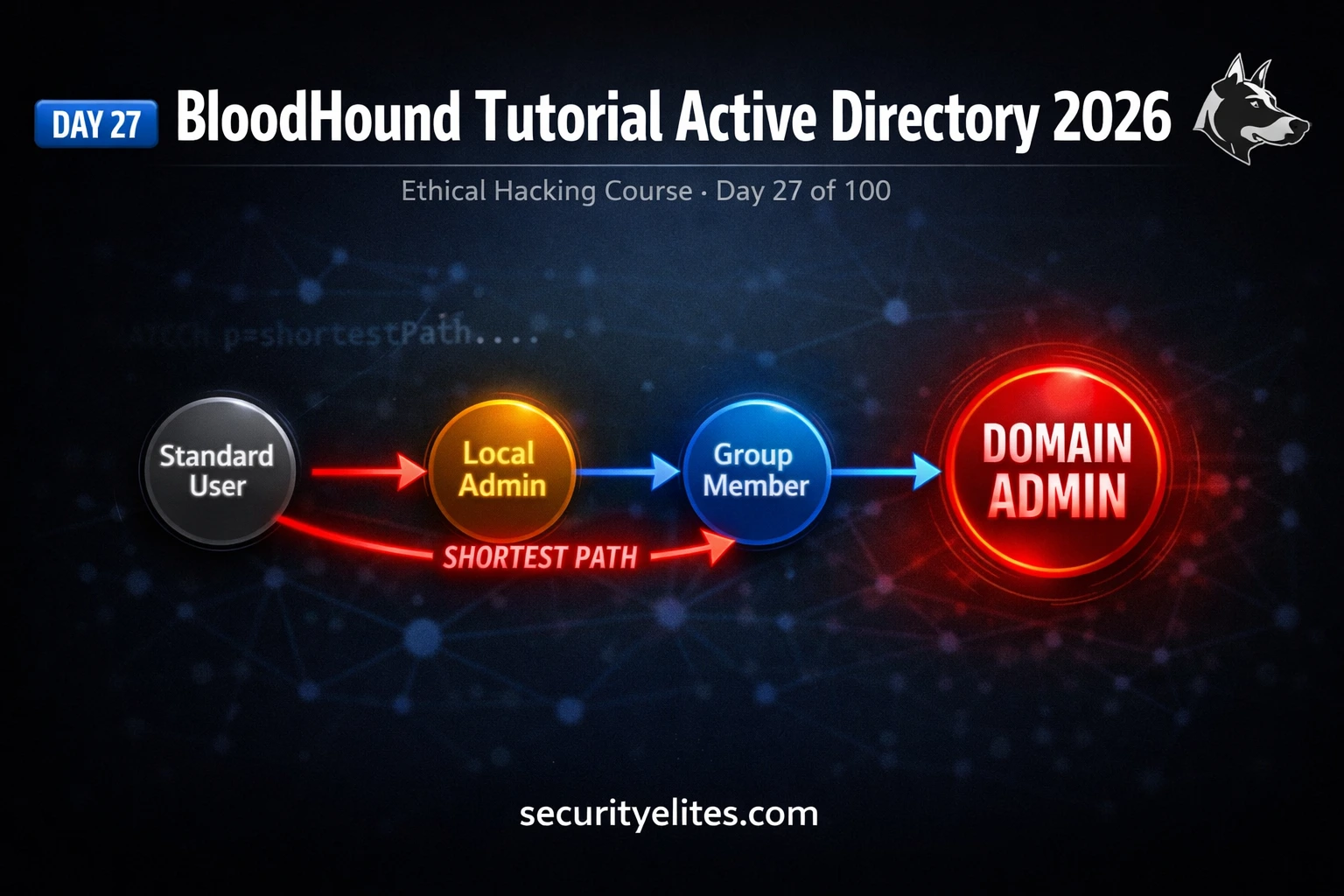
BloodHound Tutorial 2026 — Find the SHORTEST Path to Domain Admin in Minutes | Day 27
BloodHound tutorial active directory 2026 — install SharpHound, collect AD data, visualise attack paths and find the shortest route to…
Kali Linux Commands Cheat Sheet 2026 — 150 Tools, 2955 Commands, One Click
Kali linux commands cheat sheet 2026 — 150 tools, 2955+ ready-to-use commands across 13 categories. Filter by tool, copy any…
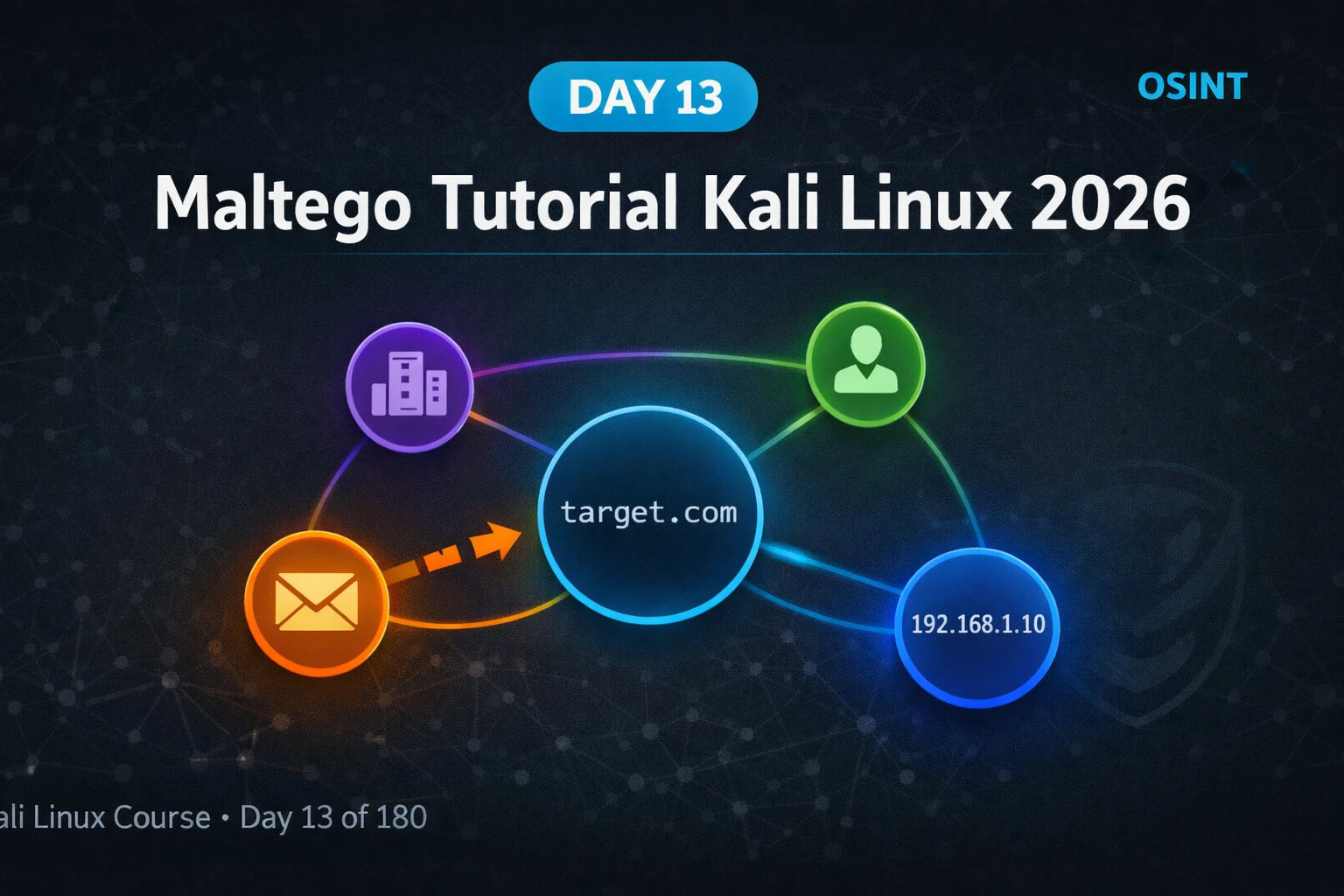
Kali Linux Day13: Maltego Tutorial Kali Linux 2026 — OSINT Link Analysis & Entity Mapping Guide
Maltego tutorial kali linux 2026 — install Community Edition, run transforms, map domains and emails, build entity graphs for OSINT…
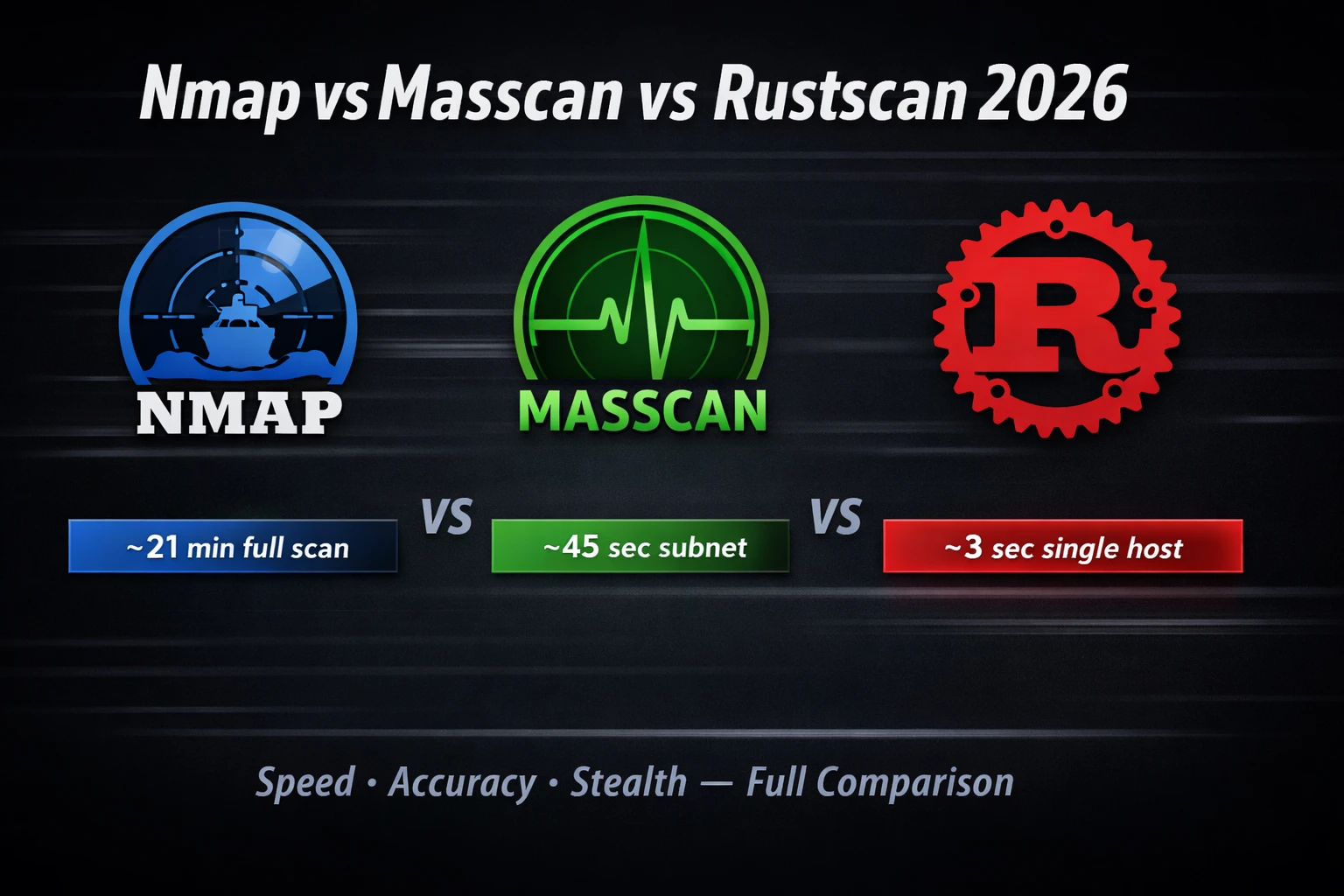
Nmap vs Masscan vs Rustscan 2026 — Which Port Scanner Is Fastest & Most Accurate?
Nmap vs masscan vs rustscan 2026 — speed benchmarks, accuracy tests, stealth comparison and which scanner to use for recon,…