Cyber Security Tools
Discover the most powerful cyber security tools and ethical hacking tools used by penetration testers and security researchers. This category features detailed tutorials, installation guides, and usage walkthroughs for reconnaissance, exploitation, OSINT, wireless testing, and password cracking tools. Explore both free and premium security tools, compare their features, and learn how to use them effectively in real penetration testing scenarios.
81 articles
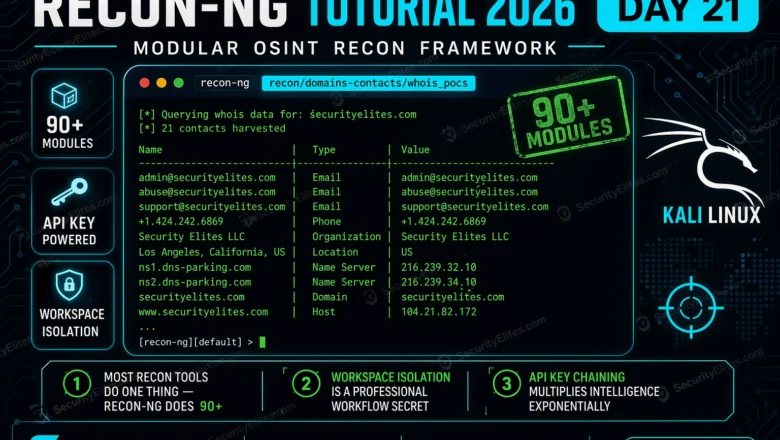
Recon-ng Tutorial 2026 — Modular OSINT Framework for Professional Reconnaissance | Tools Day21
Recon-ng tutorial 2026 — install, configure workspaces, run modules, harvest emails domains and contacts using the most powerful modular OSINT…
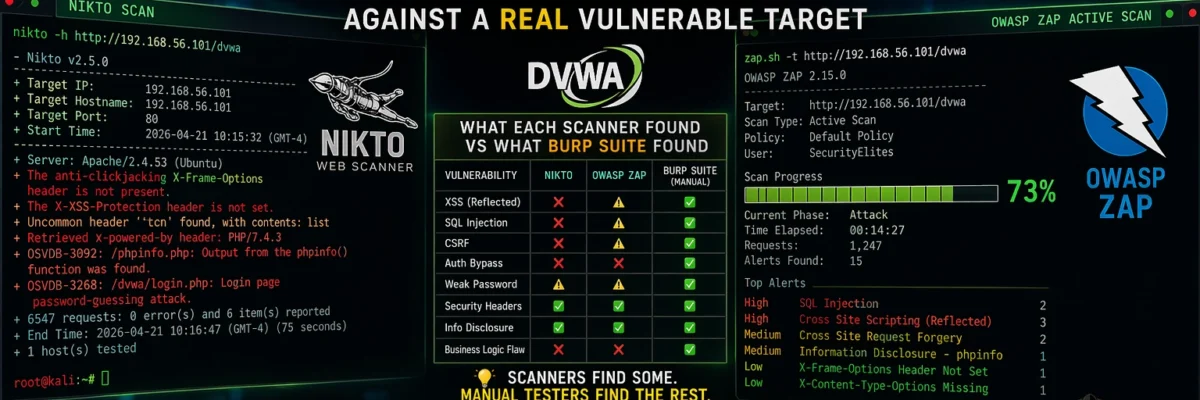
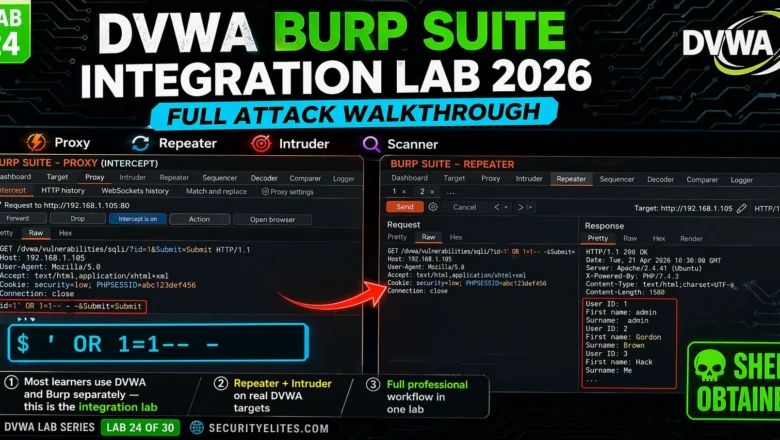
DVWA Burp Suite Integration Lab 2026 — Full Attack Walkthrough Using Burp Suite | Hacking Lab24
DVWA Burp Suite integration lab 2026 — configure Burp proxy, use Repeater, Intruder and Scanner to exploit every DVWA vulnerability…
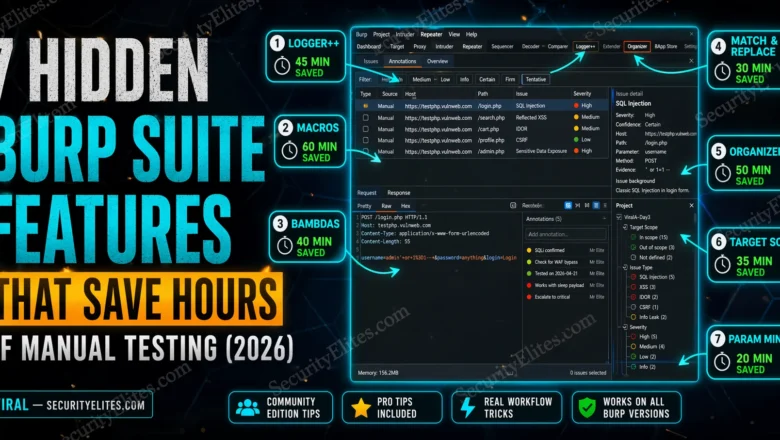
7 Hidden Burp Suite Features That Save Hours of Manual Testing (2026)
7 Burp Suite hidden features most ethical hackers miss in 2026 — macros, Logger++, Match & Replace, Bambdas, target scope…
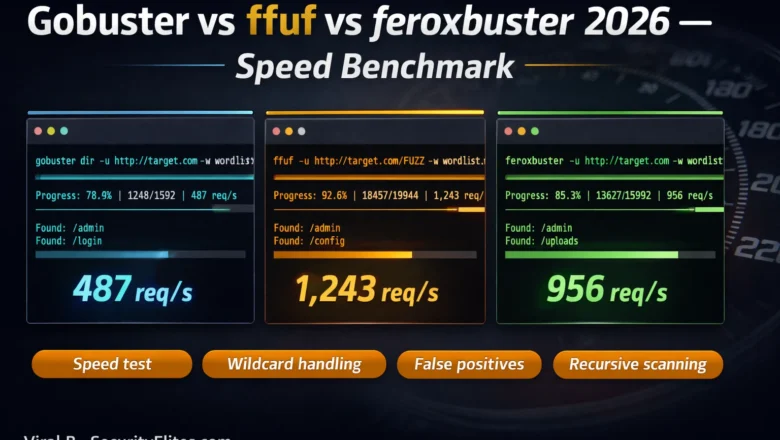
Gobuster vs ffuf vs feroxbuster — Speed & Accuracy Benchmark 2026
Gobuster vs ffuf vs feroxbuster 2026 — side-by-side speed and accuracy benchmark. Which directory fuzzer wins on speed, false positives,…
Meterpreter Commands Cheat Sheet 2026 — 50+ Commands With Real Examples
Complete Meterpreter commands cheat sheet 2026. Every essential Meterpreter command with real examples — system recon, file operations, privilege escalation,…
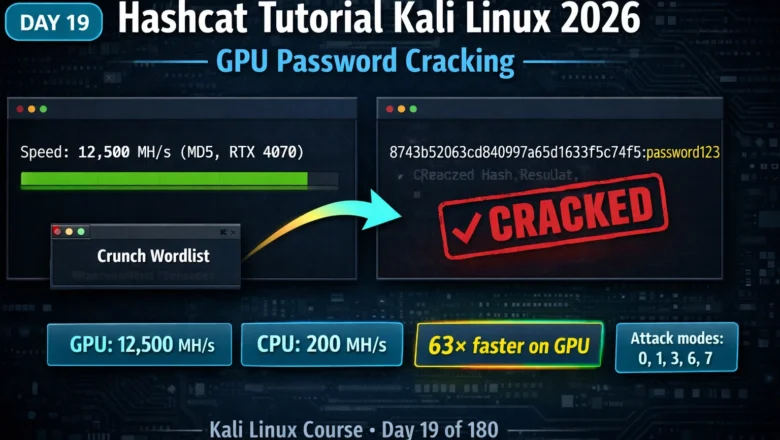
Kali Linux Day19: Hashcat Tutorial Kali Linux 2026 — GPU Password Cracking, Attack Modes & Benchmarking
Hashcat tutorial Kali Linux 2026 — master GPU password cracking with dictionary, mask, rule-based and combinator attack modes. Crack MD5,…
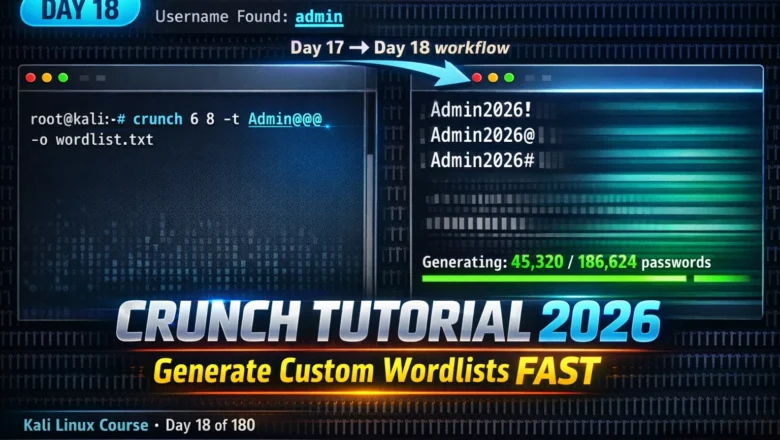
Kali Linux Day18: Crunch Tutorial Kali Linux 2026 — Generate Custom Wordlists for Targeted Password Attacks
Crunch tutorial kali linux 2026 — generate custom password wordlists using patterns, character sets and rules. Day 18 complete guide…
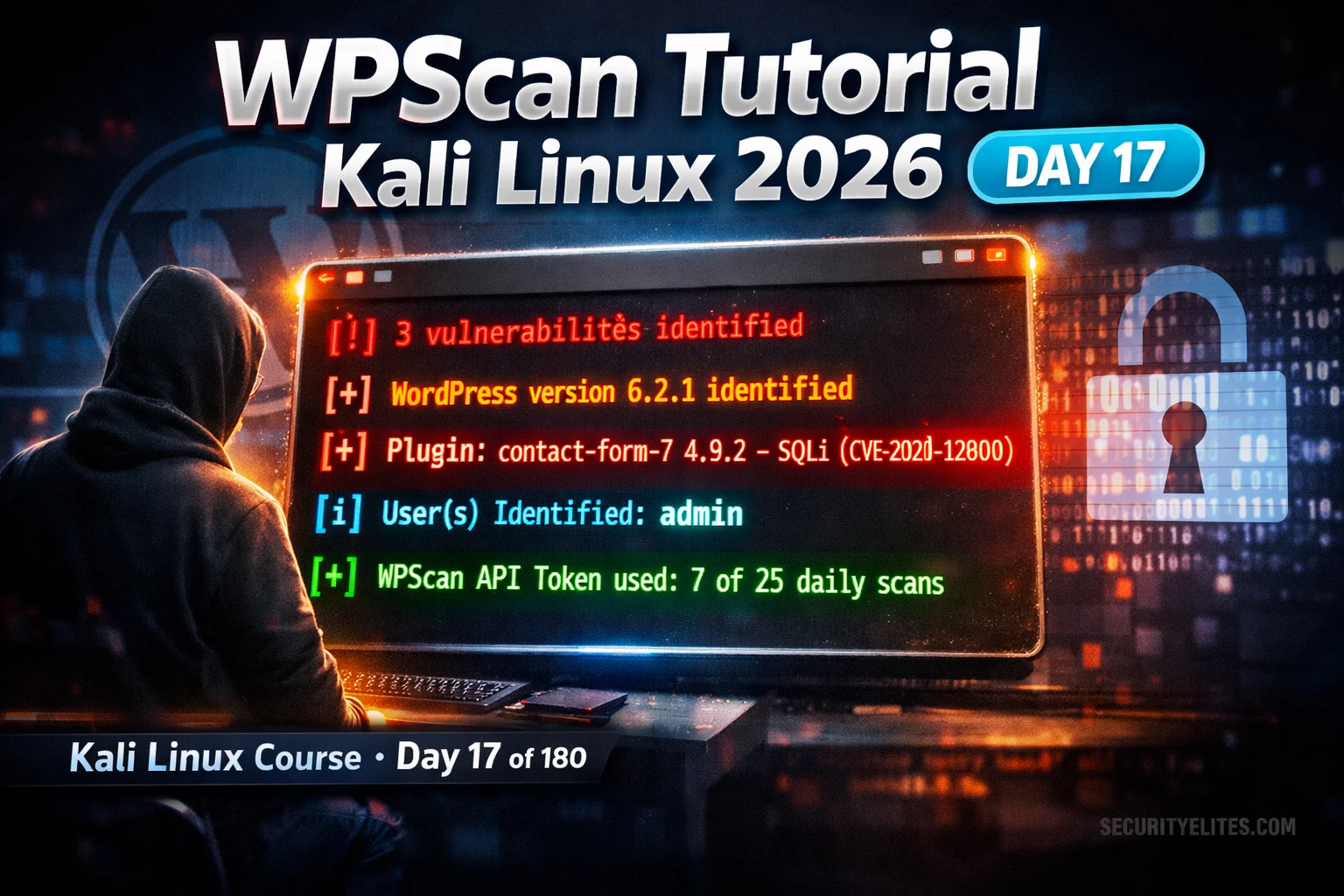
WPScan Tutorial Kali Linux 2026 — Scan WordPress Sites, Find Vulnerabilities & Enumerate Users | Tools Day17
WPScan tutorial kali linux 2026 — scan WordPress sites for vulnerable plugins, themes and users. Day 17 complete guide with…
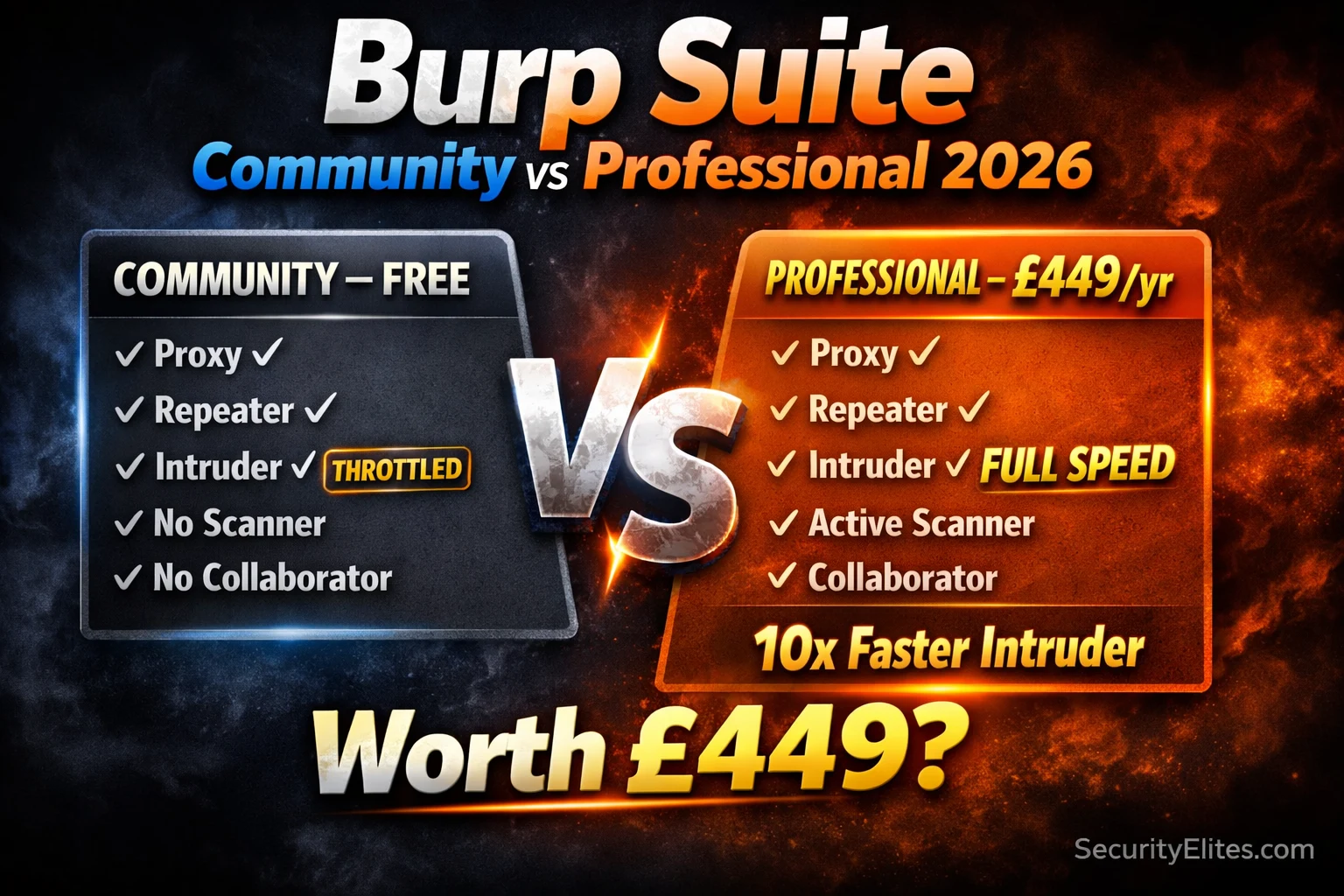
Burp Suite Community vs Professional 2026 — Is the Upgrade Worth £449?
Burp suite community vs professional 2026 — honest comparison of every feature difference. Is the £449/year upgrade worth it for…