Part of the 100-Day Ethical Hacking Course
🎯 What You’ll Master in Day 31
⏱️ 50 min read · 3 exercises
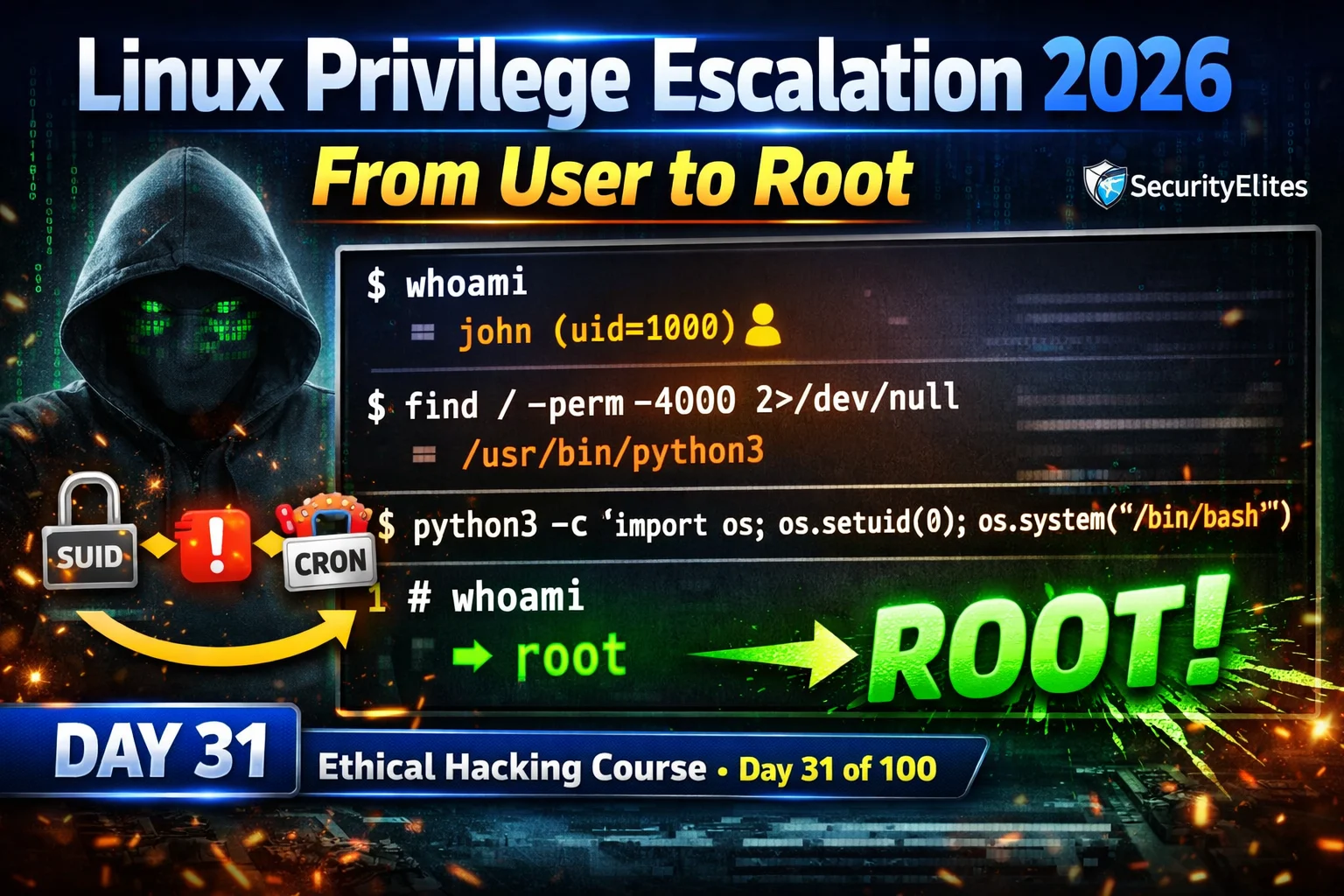
📋 Linux Privilege Escalation 2026
In Day 30 you established persistence mechanisms on Windows. Day 31 returns to a critical earlier phase: escalating from initial access to full system compromise on Linux. You cannot establish persistent access with real impact until you have root-level privileges — persistence and escalation always work together in the 100-Day Ethical Hacking Course.
Enumeration First — LinPEAS and Manual Checks
⏱️ Time: 8 minutes · No tools required
these findings (colour-coded: RED=critical, YELLOW=interesting):
[RED] SUID files found:
/usr/bin/python3.9 (owned by root)
/usr/bin/find
/usr/bin/nmap (version 5.21)
[RED] Sudo rules (sudo -l output):
(root) NOPASSWD: /usr/bin/vim /var/www/html/config.php
[YELLOW] Cron jobs (running as root):
*/5 * * * * /opt/backup/run_backup.sh
File permissions: -rwxrwxrwx (world-writable!)
[YELLOW] PATH-dependent script (owned by root, runs at login):
/usr/local/bin/system-check
Content: “ping -c 1 localhost” (uses relative path for ping)
/usr/local/bin is in your PATH and is world-writable
For each finding:
1. Which escalation technique applies?
2. What is the exact command or payload?
3. How quickly would this give you root?
4. Which finding would you exploit FIRST? Why?
📸 Share your prioritised exploitation plan in #day-31-privesc on Discord.
SUID Binary Exploitation
Sudo Misconfiguration Exploitation
Cron Job Abuse
⏱️ Time: 25 minutes · Free TryHackMe account
Step 2: Search: “Linux Privilege Escalation” room
Open: “Linux PrivEsc” or “Linux Privilege Escalation”
Step 3: Deploy machine and connect via VPN or AttackBox
Step 4: The room covers each vector — complete:
a) SUID/SGID escalation task
→ find the SUID binary, check GTFOBins, get root
b) Sudo escalation task
→ sudo -l, exploit the listed command, get root
c) Cron job task
→ find the writable cron script, replace with payload
Step 5: For each successful escalation, note:
– The exact binary/rule/script that was vulnerable
– The exploit command used
– The MITRE ATT&CK technique ID
(T1548.001 = SUID, T1053.003 = Cron, T1548.003 = Sudo)
Step 6: Screenshot each “root shell obtained” moment
with whoami output visible
📸 Share root shell screenshots from all three escalation techniques in #day-31-privesc on Discord.
PATH Hijacking
⏱️ Time: 15 minutes · Kali · Metasploitable or TryHackMe
📸 Screenshot the full chain from initial shell to root whoami in #day-31-privesc on Discord. Tag #linuxprivesc2026
🧠 QUICK CHECK — Day 31
📋 Linux Privilege Escalation Quick Reference — Day 31
🏆 Mark Day 31 as Complete
Linux privilege escalation completes the post-exploitation picture on Linux targets. SUID, sudo, cron, and PATH hijacking cover the vast majority of real-world escalation vectors. Day 32 applies the equivalent techniques to Windows — unquoted service paths, weak service permissions, and token impersonation.
❓ Frequently Asked Questions
What is Linux privilege escalation?
What is a SUID binary and how is it exploited?
What is GTFOBins?
What is LinPEAS?
What comes after Day 31?
Day 30: Post-Exploitation Persistence 2026
Day 32: Windows Privilege Escalation 2026
📚 Further Reading
- Post-Exploitation Persistence 2026 — Day 30 covers Windows persistence — complements Day 31 by covering the post-escalation phase: once you have root, persistence ensures you keep it.
- Privilege Escalation Hub — Complete SecurityElites privilege escalation category covering Linux SUID/sudo/cron, Windows service exploits, and cross-platform escalation techniques.
- 100-Day Ethical Hacking Course — The complete course hub — Day 31 privilege escalation is the start of the post-exploitation specialisation phase covering Days 31-45.
- GTFOBins — The essential privilege escalation reference — every Unix binary that can be exploited for SUID abuse, sudo escalation, file read/write, and shell spawning with exact command examples.
- LinPEAS — PEASS-ng GitHub — The LinPEAS automated privilege escalation enumeration script — download link, full documentation, and the complete list of checks the script performs with explanations of each finding category.