FREE
Part of the DVWA Lab Series — 30 Labs
🎯 What You’ll Learn in Lab 14
⏱️ 40 min · 3 source code analysis exercises
✅ Prerequisites
- DVWA Labs 1–13 completed (or working knowledge of each vulnerability type)
- DVWA running locally with PHP source accessible via View Source
- Basic PHP reading ability (you do not need to write PHP — just read logic)
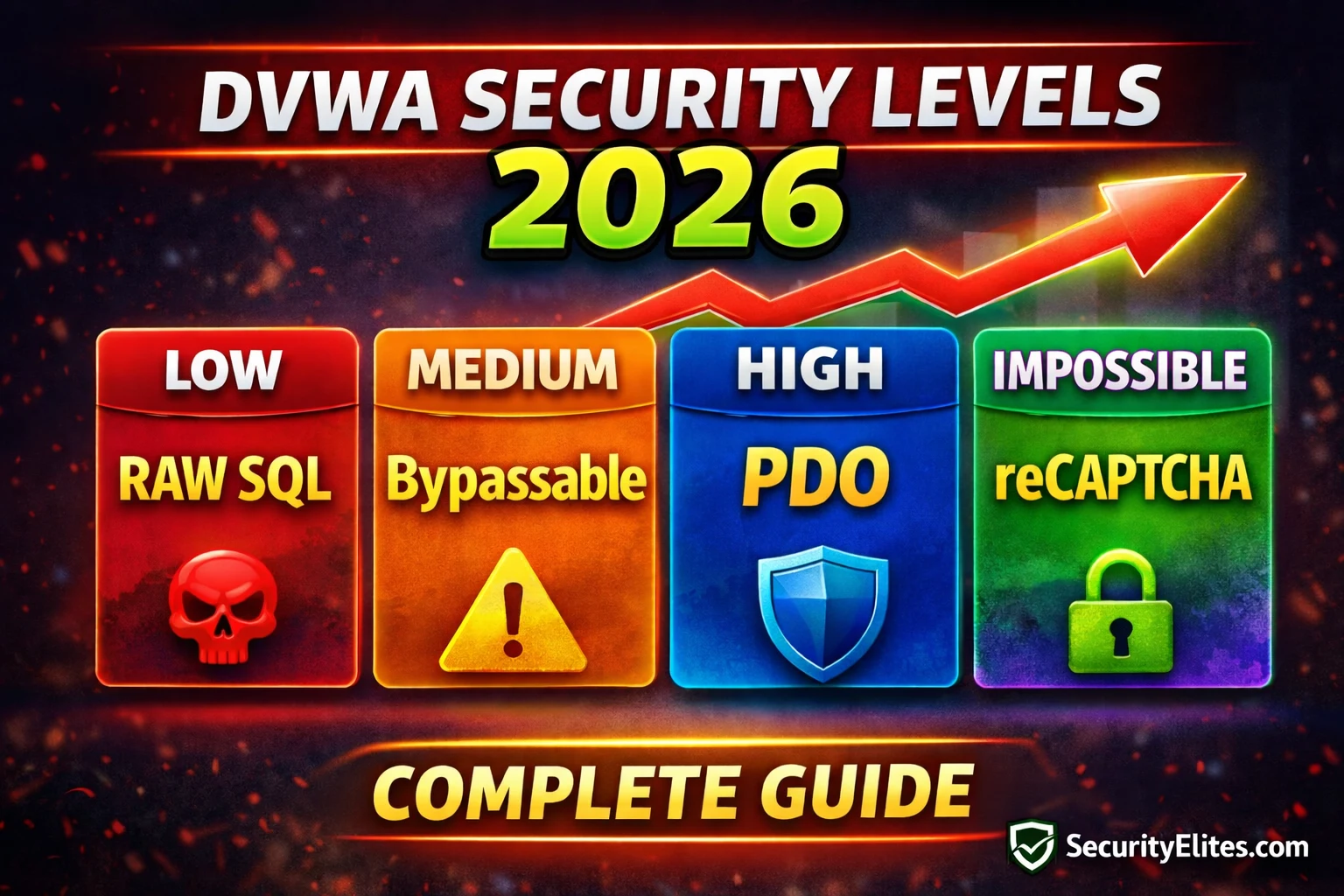
📋 Lab 14 Contents — DVWA Security Levels Explained
In Lab 13 you saw a logic flaw in CAPTCHA implementation. Lab 14 zooms out to view the entire DVWA security framework — understanding how defences are layered, why some fail, and what genuine security looks like in code. This knowledge is directly applicable to the remaining 16 DVWA labs and to writing remediation recommendations in real penetration test reports.
What Each Security Level Actually Changes
SQL Injection — Low vs Impossible Source Comparison
⏱️ Time: 15 minutes · DVWA running · navigate to SQL Injection module
📸 Screenshot all four source code snippets in DVWA and share in #dvwa-labs on Discord.
XSS — How Each Level Tries (and Sometimes Fails) to Filter Output
⏱️ Time: 12 minutes · DVWA XSS Reflected module · View Source
Hello ${name}“;
📸 Screenshot the Medium and Impossible source side by side and share in #dvwa-labs on Discord.
CSRF and Brute Force — Token and Lockout Implementation
⏱️ Time: 10 minutes · DVWA Brute Force module · View Source
📸 Screenshot the Impossible lockout source code and share in #dvwa-labs on Discord. Tag #dvwasecurity2026
Impossible Security Patterns — The Code Standards Worth Memorising
The DVWA Impossible security level consistently implements the same five patterns across all modules. Memorising these makes you faster at writing accurate recommendations in penetration test reports — you can name the exact function and pattern the developer should implement rather than writing generic “validate input” advice.
🧠 QUICK CHECK — Lab 14
📋 Lab 14 Reference — Impossible Security Quick Reference
🏆 Mark Lab 14 as Complete
You now understand what every DVWA security level actually changes in the source code, why Medium defences fail, and what Impossible-level implementation looks like for each vulnerability class. These five secure coding patterns belong in every penetration test finding recommendation you write.
❓ Frequently Asked Questions
What do the DVWA security levels change?
What is DVWA Impossible security and can it be bypassed?
How do I use DVWA View Source effectively?
Is mysql_real_escape_string a complete SQL injection fix?
What comes after DVWA Lab 14?
Lab 13: DVWA Insecure CAPTCHA 2026
Lab 15: DVWA Brute Force Advanced — Anti-CSRF Bypass
📚 Further Reading
- DVWA Insecure CAPTCHA Lab 2026 — Lab 13 demonstrated the logic flaw that the Impossible source code in this lab shows how to fix — server-side API verification replacing client-trusted step parameters.
- DVWA Labs Hub — All 30 DVWA labs in sequence — with the source code analysis skills from Lab 14, all subsequent labs include a deeper understanding of why each vulnerability exists and how it is fixed.
- SQL Injection Complete Guide — The complete SQL injection category covering manual techniques, automated tools, and the PDO prepared statement remediation demonstrated in Lab 14’s Impossible source.
- OWASP DVWA Project Page — The official DVWA project documentation including security level explanations, installation guides for Docker/XAMPP, and the complete list of vulnerability modules in the current release.
- OWASP SQL Injection Prevention Cheat Sheet — The definitive reference for PDO prepared statement implementation in multiple languages — the practical extension of the Impossible security pattern shown in Lab 14.