FREE
Part of the DVWA Lab Series — 30 Labs
🎯 What You’ll Learn in Lab 13
⏱️ 35 min · 3 Burp Suite exercises
✅ Prerequisites
- DVWA running locally (Lab 1: DVWA Setup Guide)
- Burp Suite configured as proxy (Day 12: Burp Suite Kali Linux)
- Basic understanding of HTTP POST parameters
📋 Lab 13 Contents — DVWA Insecure CAPTCHA Lab
In Lab 12 you automated database extraction with SQLmap. Lab 13 demonstrates a completely different vulnerability class — business logic flaws. Where SQL injection is a technical vulnerability in data handling, insecure CAPTCHA is a design flaw in security control implementation. Both appear in the DVWA Lab Series and in real bug bounty programmes.
The Insecure CAPTCHA Vulnerability Explained
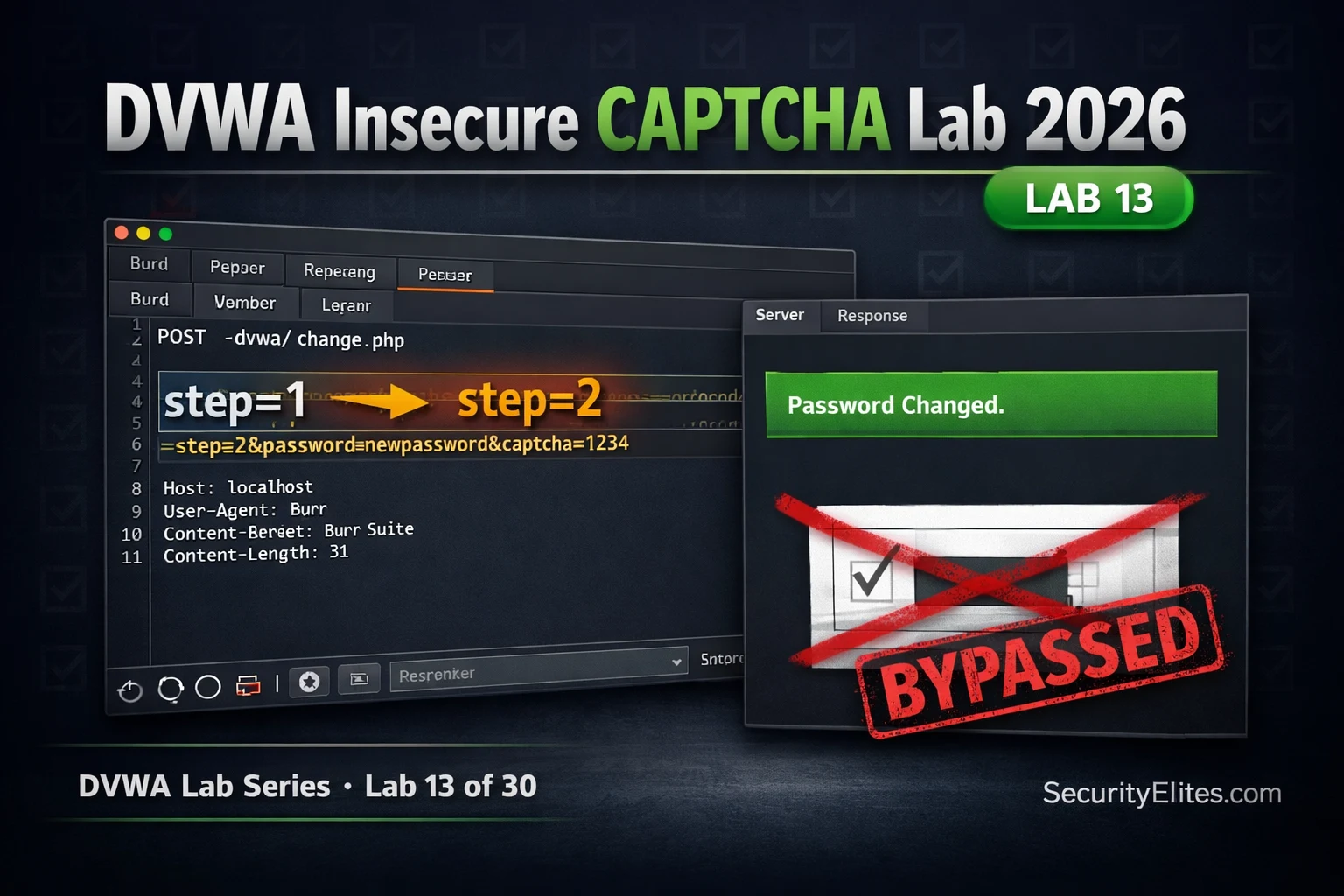
The DVWA Insecure CAPTCHA module simulates a password change form protected by a CAPTCHA. The intended flow is: (1) user fills in new password → (2) user completes CAPTCHA → (3) CAPTCHA is verified → (4) password changes. The insecure implementation tracks which step the user is on using a parameter in the HTTP request. Step 1 is the CAPTCHA form; step 2 is the processing step. If the server trusts the step value without independently verifying that the CAPTCHA was actually completed, an attacker submits step=2 directly and bypasses the entire control.
⏱️ Time: 15 minutes · DVWA running · Burp Suite proxy active
📸 Screenshot Burp Repeater showing step=2 and the “Password Changed.” response. Share in #dvwa-labs on Discord.
Medium Security — passed_captcha Parameter Injection
Medium security changes the mechanism but not the fundamental flaw. Instead of a step number, the application uses a passed_captcha boolean parameter. If this parameter is present and true in the POST request, the server skips CAPTCHA verification. The attacker simply adds passed_captcha=true to the POST body — the server trusts it without any verification.
⏱️ Time: 10 minutes · DVWA at Medium security
📸 Screenshot the View Source showing the passed_captcha PHP check. Share in #dvwa-labs on Discord.
High Security — Server-Side Verification (The Correct Approach)
⏱️ Time: 10 minutes · DVWA View Source comparison
📸 Screenshot both source code sections side-by-side and share in #dvwa-labs on Discord. Tag #captchabypass2026
Real-World CAPTCHA Bypass Patterns in Bug Bounty
CAPTCHA bypass vulnerabilities appear regularly in bug bounty programmes in several patterns beyond the DVWA step-parameter example. The most common are: CAPTCHA only on the web form but not on the underlying API endpoint (submit the API POST directly, bypassing the form and its CAPTCHA entirely); CAPTCHA response tokens that are not invalidated server-side after use (replay the same g-recaptcha-response token multiple times); CAPTCHA only on GET requests, not on POST to the same endpoint; and CAPTCHA verification that is asynchronous with a race condition window where the action completes before verification responds.
🧠 QUICK CHECK — Lab 13
📋 Lab 13 Key Findings Reference
🏆 Mark Lab 13 as Complete
Lab 13 demonstrated the insecure CAPTCHA logic flaw — a business logic vulnerability that bypasses access controls through parameter manipulation rather than code injection. This is a distinct and equally important vulnerability class from the SQL injection and XSS attacks in earlier labs.
❓ Frequently Asked Questions
What is the DVWA Insecure CAPTCHA vulnerability?
Why is the step parameter approach insecure?
What is the secure CAPTCHA implementation?
Is Insecure CAPTCHA a real bug bounty vulnerability?
What comes after DVWA Lab 13?
Lab 12: DVWA SQLmap Lab 2026
Lab 14: DVWA Security Levels Explained
📚 Further Reading
- DVWA SQLmap Lab 2026 — Lab 12 automated database extraction with SQLmap — the technical counterpart to Lab 13’s logic flaw approach.
- Web Application Security Hub — The complete web application security category covering logic flaws, injection attacks, XSS, CSRF, and authentication vulnerabilities.
- DVWA Labs Hub — All 30 DVWA labs in sequence — the complete walkthrough series from setup through advanced exploitation techniques.
- Burp Suite Kali Linux 2026 — Day 12 covers Burp Suite setup and HTTPS interception — the proxy technique used in this lab to intercept and modify the step parameter.
- DVWA GitHub Repository — Damn Vulnerable Web Application (DVWA) GitHub Repository.