Part of the 180-Day Kali Linux Mastery Course
🎯 What You’ll Master in Day 17
⏱️ 45 min read · 3 hands-on exercises
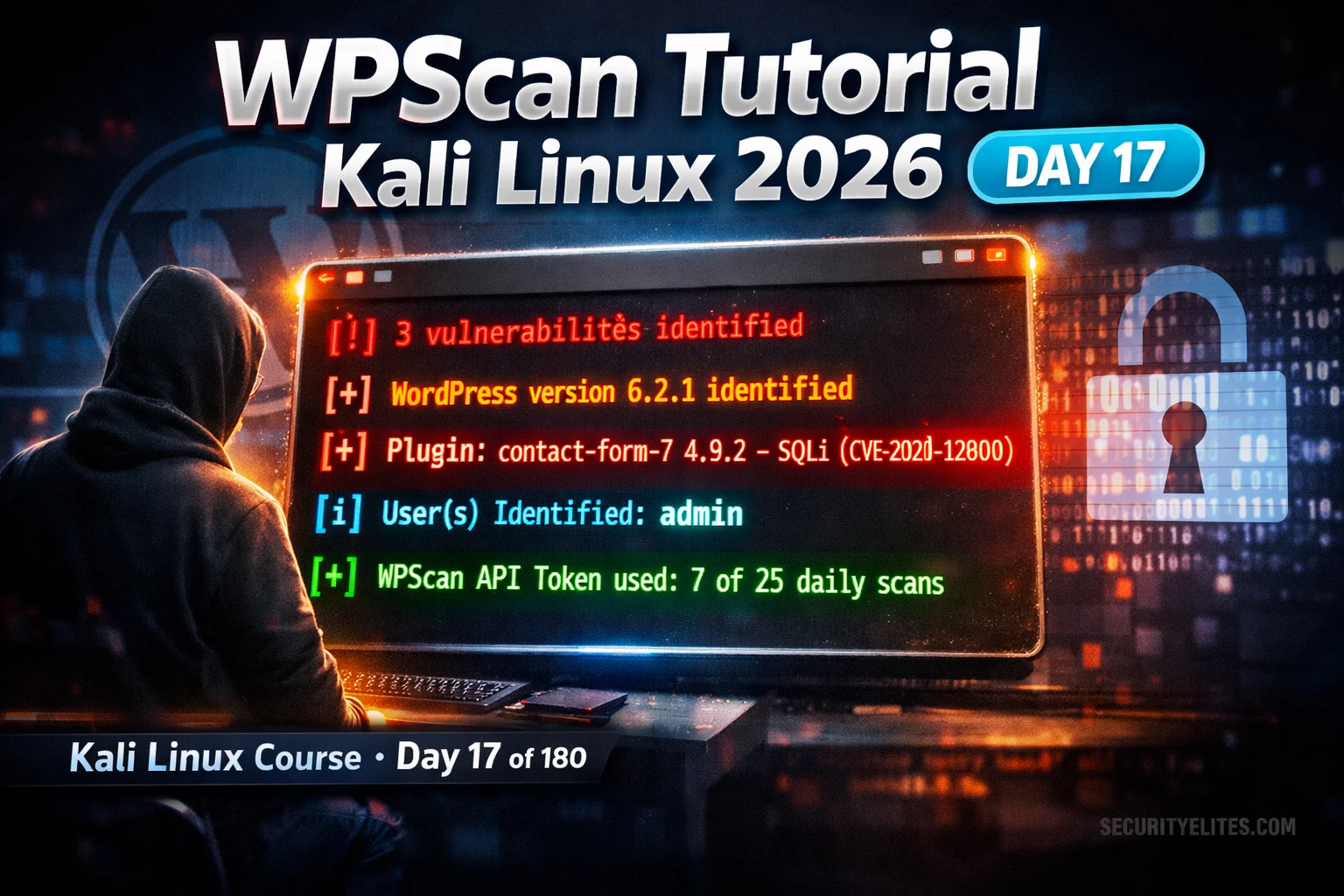
📋 WPScan Tutorial Kali Linux 2026
In Day 16 you used DirBuster to discover hidden directories on web servers. Day 17 takes web enumeration to the next level — WPScan is to WordPress what DirBuster is to generic web servers, but with built-in CVE intelligence. Together they form the complete web application reconnaissance toolkit in the 180-Day Kali Linux Mastery Course.
Setup — Installation, Update, and API Token
⏱️ Time: 8 minutes · No tools required
Think through the security implications:
1. PLUGIN LIFECYCLE PROBLEM:
A site installs a plugin in 2022, uses it for 6 months,
then deactivates it but never deletes it.
The plugin receives a critical security patch in 2024.
→ What is the security implication? Is the site vulnerable?
→ Would WPScan’s aggressive mode find this plugin?
2. THIRD-PARTY CODE TRUST:
A developer submits a plugin to the WordPress repository.
It has a backdoor. It gets 10,000 installs before discovery.
→ What trust model does WordPress use for plugins?
→ How does this compare to enterprise software procurement?
3. ENUMERATION STANDARDISATION:
WordPress installs all plugins under /wp-content/plugins/[name]/
with predictable file paths (readme.txt contains version number).
→ Why does this standardisation help attackers?
→ How would you defend against plugin version fingerprinting?
4. THE LONG TAIL:
Most WordPress vulnerabilities are in plugins with under
1,000 active installs — niche plugins that maintain small
sites without dedicated security teams.
→ Why does this create a disproportionate attack surface?
Write a 3-sentence assessment of why WordPress’s architecture
creates a persistent security challenge despite its popularity.
📸 Share your 3-sentence WordPress security architecture assessment in #day-17-wpscan on Discord.
Basic WordPress Scan — Version, Plugins, Themes
User Enumeration — Finding Valid Usernames
⏱️ Time: 20 minutes · Kali terminal · authorised practice target only
📸 Screenshot your WPScan results showing identified plugins/versions and share in #day-17-wpscan on Discord.
Aggressive Mode — Complete Plugin and Theme Discovery
The difference between passive and aggressive detection is the difference between finding what is advertised and finding everything that is installed. Passive detection reads plugin references from page source code. Aggressive detection systematically requests known plugin file paths — WPScan maintains a database of over 50,000 plugin directory names and checks each one for the presence of readme.txt (which contains the version number). This discovers inactive, hidden, and legacy plugins that would never appear in passive scanning.
⏱️ Time: 12 minutes · Kali terminal · own local WordPress only
📸 Screenshot the complete WPScan → credential attack chain on your local WordPress and share in #day-17-wpscan on Discord. Tag #wpscan2026
🧠 QUICK CHECK — Day 17
📋 Commands Used Today — Day 17 WPScan Reference
🏆 Mark Day 17 as Complete
WPScan is one of the most practically useful tools in your Kali arsenal because WordPress is everywhere. The combination of version fingerprinting, CVE mapping, user enumeration, and aggressive plugin discovery gives you a comprehensive WordPress attack surface in under 5 minutes. Day 18 covers Crunch — the password list generator that feeds the credential attacks Day 17 sets up.
❓ Frequently Asked Questions
What is WPScan and what does it find?
Does WPScan need an API token?
Is WPScan legal to use?
What is passive vs aggressive detection?
How does WPScan enumerate users?
What comes after Day 17?
Day 16: DirBuster Tutorial 2026
Day 18: Crunch Password Generator 2026
📚 Further Reading
- DirBuster Tutorial Kali Linux 2026 — Day 16 covers generic web directory discovery — the broader web enumeration technique that WPScan specialises for WordPress targets.
- Kali Linux Tools Hub — Complete Kali Linux tools reference — WPScan in context with the full web application assessment toolkit including Nikto, Gobuster, Burp Suite, and SQLmap.
- 180-Day Kali Linux Mastery Course — The complete course hub — Day 17 WPScan is part of the web application reconnaissance phase covering Days 14–22.
- WPScan GitHub Repository — Official WPScan source code and documentation — complete flag reference, custom detection rules, API documentation, and contribution guide for the WPVulnDB vulnerability database.
- WPScan Wordlists — Official WPScan wordlists for plugin and theme detection — understanding what the aggressive scan is checking helps interpret why it finds inactive plugins the passive mode misses.