🎯 What You’ll Learn
⏱️ 40 min read · 3 exercises
📊 How do you currently use Nmap?
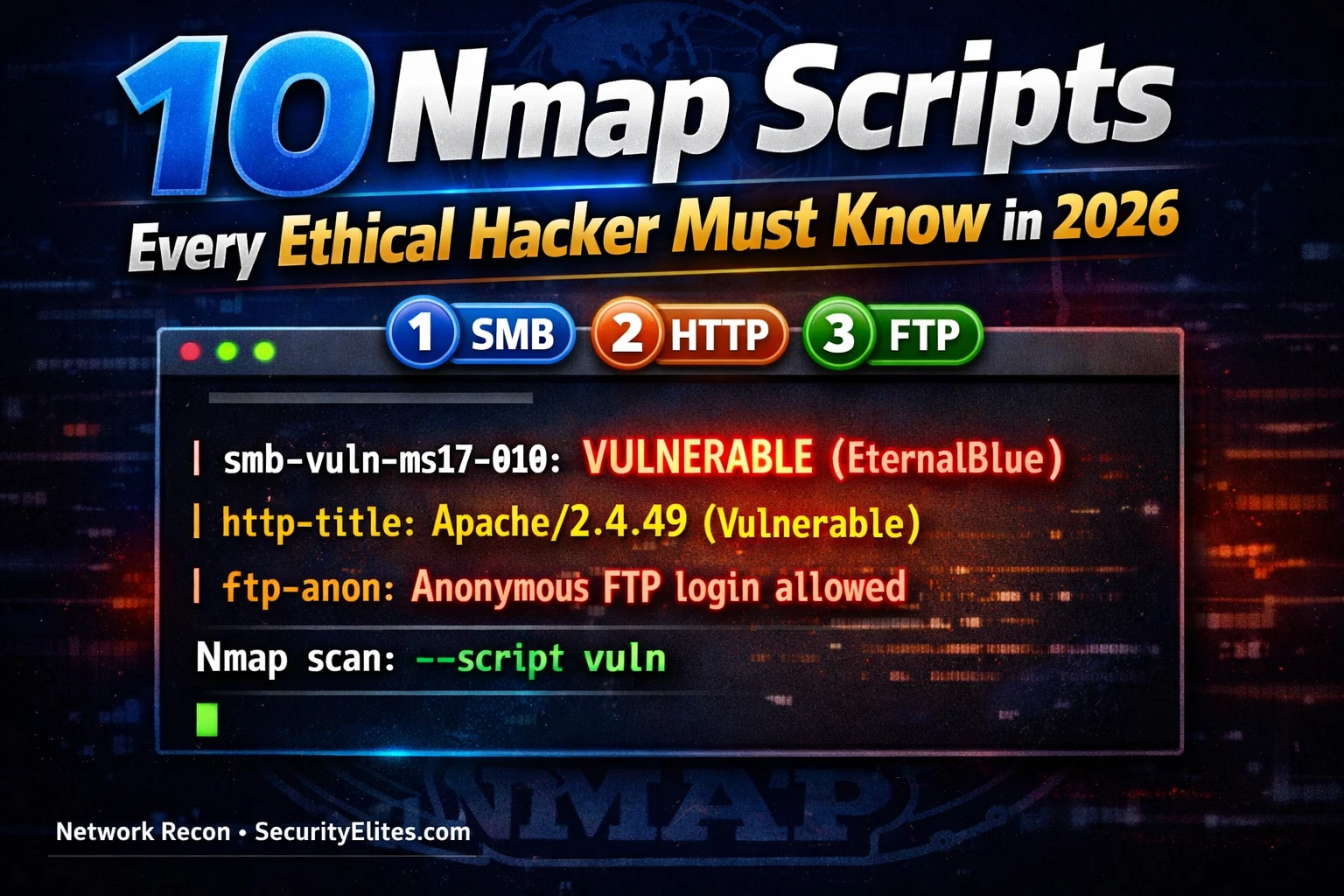
📋 The 10 Nmap scripts Ethical Hackers Must Know
- smb-vuln-ms17-010 — EternalBlue Detection
- smb-enum-users — SMB User Enumeration
- http-enum — Web Directory Discovery
- http-methods — Dangerous HTTP Method Detection
- ssl-heartbleed — Heartbleed Vulnerability
- ftp-anon — Anonymous FTP Login
- smtp-open-relay — Mail Relay Misconfiguration
- vulners — CVE Lookup per Service Version
- http-title — Web Server Title and Header Fingerprinting
- ssh-auth-methods — SSH Authentication Discovery
1. smb-vuln-ms17-010 — EternalBlue Detection
MS17-010 (EternalBlue) is the SMB vulnerability that powered WannaCry and NotPetya. Despite being patched in 2017, it remains present in unpatched systems encountered on internal network assessments. This script checks for the vulnerability without attempting exploitation — safe to run during a vulnerability assessment.
2. smb-enum-users — SMB User Enumeration
3. http-enum — Web Directory Discovery
4. http-methods — Dangerous HTTP Method Detection
5. ssl-heartbleed — Heartbleed Detection
6. ftp-anon — Anonymous FTP Login
⏱️ Time: 15 minutes · Kali terminal · Metasploitable running
📸 Screenshot your NSE scan output showing VULNERABLE findings and share in #nmap-scripts on Discord.
7. smtp-open-relay — Mail Relay Misconfiguration
8. vulners — CVE Lookup per Service Version
9. http-title — Web Server Title Fingerprinting
10. ssh-auth-methods — SSH Authentication Discovery
⏱️ Time: 8 minutes · No tools required
you would run. Time and stealth matter.
SCENARIO A: Quick triage of 50 Windows servers.
You have 30 minutes. Primary concern: unpatched SMB.
Write the single Nmap command.
SCENARIO B: Full web application pre-assessment.
30 web servers, multiple ports. Need: directories,
titles, methods, SSL status. No IDS concern.
Write the command.
SCENARIO C: Targeted single-host deep scan.
One Linux server, all services. Maximum finding density.
IDS present — need to keep noise moderate.
Write the command — and explain one flag you add for
stealth.
📸 Share your three NSE commands in #nmap-scripts on Discord.
⏱️ Time: 10 minutes · Browser · nmap.org
Step 2: Pick any 3 services you recently found open in a scan
(e.g. RDP, MySQL, MongoDB, Redis, Elasticsearch)
Step 3: For each service, find its NSE scripts in the NSEDoc
Step 4: Note: which category is each script? (safe/intrusive/vuln)
Step 5: Also run on Kali terminal:
ls /usr/share/nmap/scripts/ | grep -i [servicename]
Compare what’s installed vs what NSEDoc lists
Step 6: For one of your three services, run:
nmap –script-help [script-name]
Note what arguments are accepted
📸 Share your three service script discoveries in #nmap-scripts on Discord. Tag #nmapscripts2026
🧠 QUICK CHECK — NSE Scripts
📋 The 10 Scripts — Quick Reference
❓ Frequently Asked Questions
What is the Nmap Scripting Engine (NSE)?
What is the difference between -sC and –script=vuln?
How do I find Nmap scripts for a specific service?
Which scripts are most useful for penetration testing?
Are Nmap scripts safe for production servers?
Nmap Commands — Complete Reference 2026
180-Day Kali Linux Course
📚 Further Reading
- Nmap Commands Complete Reference 2026 — The complete Nmap command reference with every flag and scan type — the companion guide to NSE that covers port scanning, OS detection, and timing options alongside script usage.
- Enum4linux Tutorial 2026 — Day 15 covers dedicated SMB enumeration — use Enum4linux after smb-enum-users confirms user accounts exist for deeper RID cycling and share enumeration that Nmap scripts do not perform.
- 180-Day Kali Linux Mastery Course — The complete course hub — NSE scripts appear throughout the Kali course from Day 1 Nmap foundations through advanced service exploitation in Days 30+.
- Nmap NSEDoc — Official Script Database — The official NSE script documentation — every script with description, category, arguments, and example output. The definitive reference before running any NSE script on an authorised target.
- Vulscan — Enhanced NSE Vulnerability Scanner — A community NSE script that extends Nmap’s vulnerability detection by querying multiple CVE databases simultaneously — more comprehensive than vulners alone for version-based vulnerability lookup.