Web Application Security
Explore web application security vulnerabilities and learn how ethical hackers identify and exploit them. This category covers SQL injection, cross-site scripting (XSS), CSRF, file upload vulnerabilities, authentication bypass, API security flaws, and session management issues. You’ll find hands-on tutorials, payload examples, exploitation labs, and prevention techniques to secure web applications. Ideal for bug bounty hunters, penetration testers, and developers who want to build and test secure web platforms.
100 articles
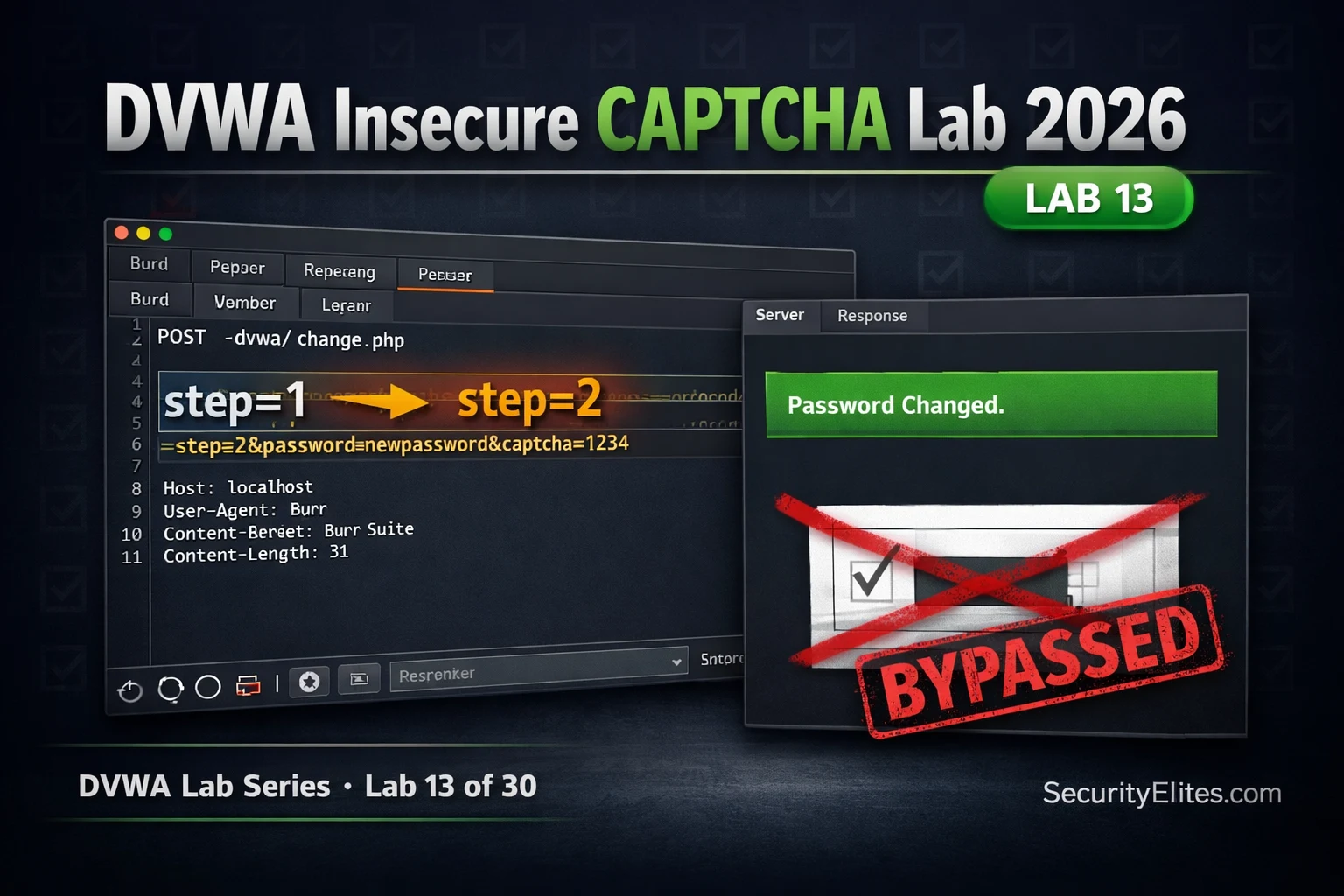
Lab13: DVWA Insecure CAPTCHA Lab 2026 — Bypass Logic & Complete Walkthrough
DVWA insecure captcha lab 2026 — bypass CAPTCHA logic flaws at all security levels using Burp Suite. Complete walkthrough with…
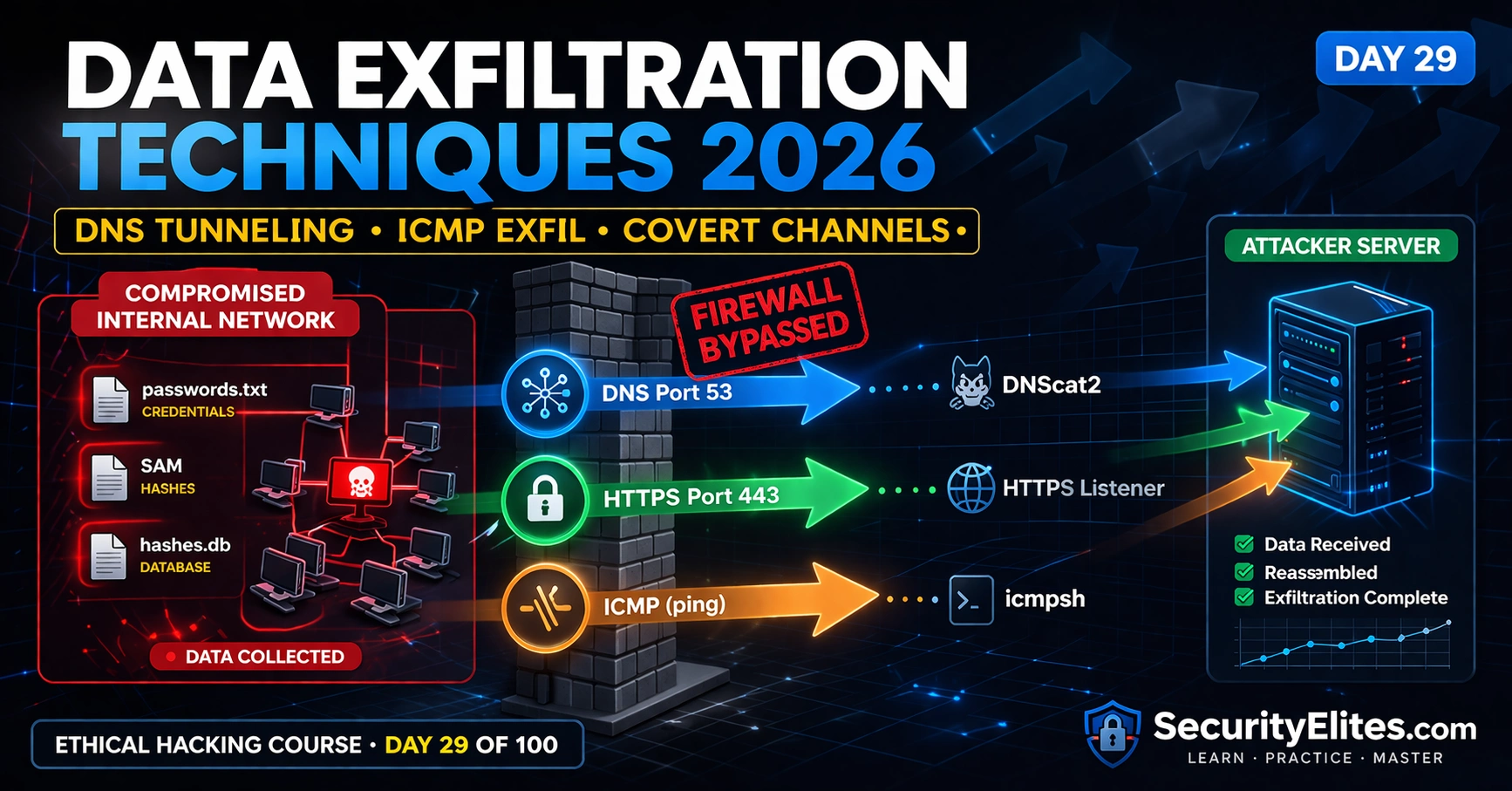
Data Exfiltration Techniques 2026 — DNS Tunneling, ICMP Exfil & Covert Channels | Hacking Course Day29
Data exfiltration techniques 2026 — move collected data out of compromised networks using DNS tunneling, ICMP covert channels and HTTPS…
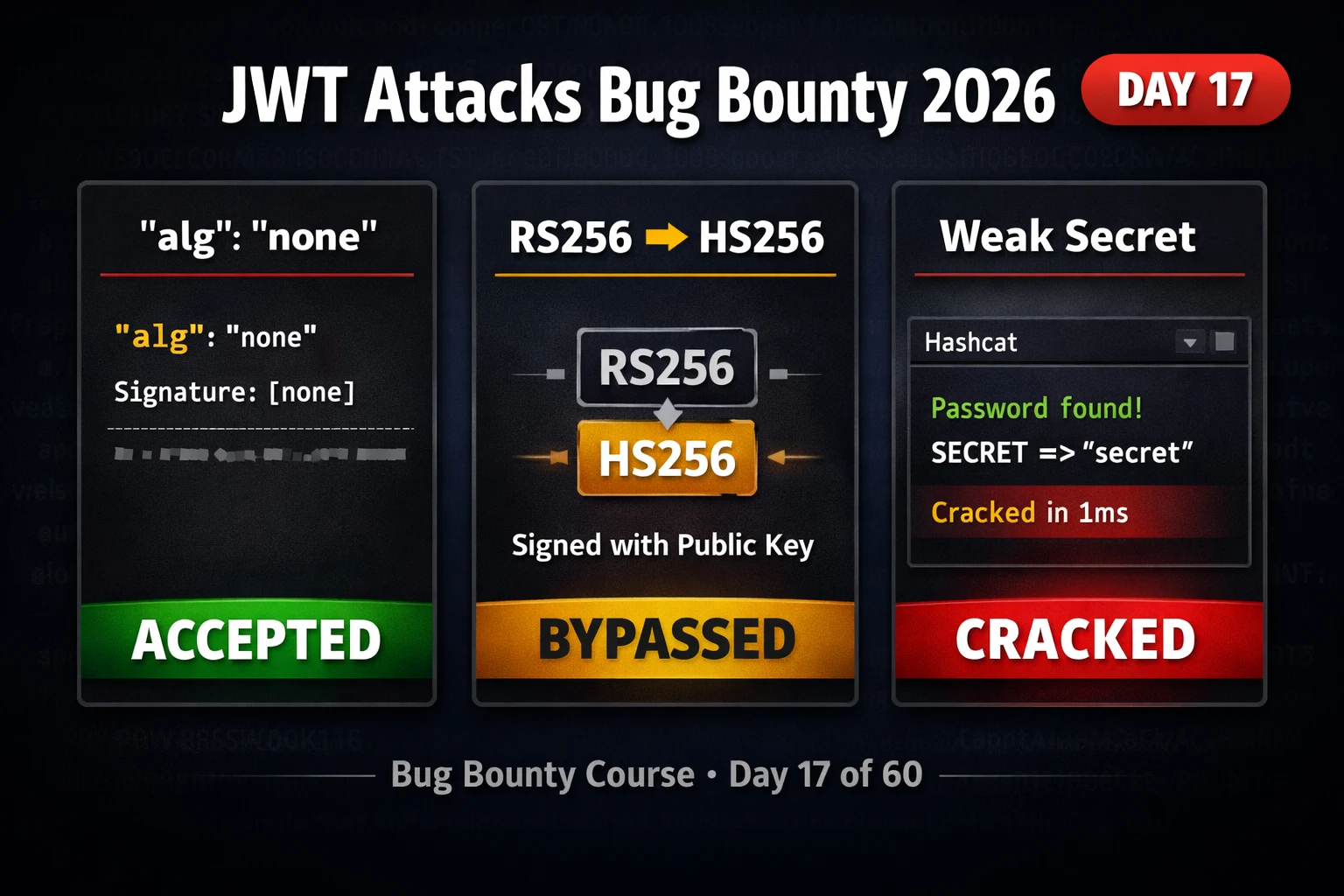
BB Day17: JWT Attacks Bug Bounty 2026 — Algorithm Confusion, None Attack & Weak Secrets
JWT attacks bug bounty 2026 — exploit algorithm confusion, none attack, weak signing secrets and kid injection in JSON web…
ChatGPT Plugins Are a Security Nightmare — Here’s How Hackers Exploit Them
ChatGPT plugin security vulnerabilities 2026 — how attackers exploit insecure plugins to exfiltrate data, bypass restrictions, and hijack AI tool…
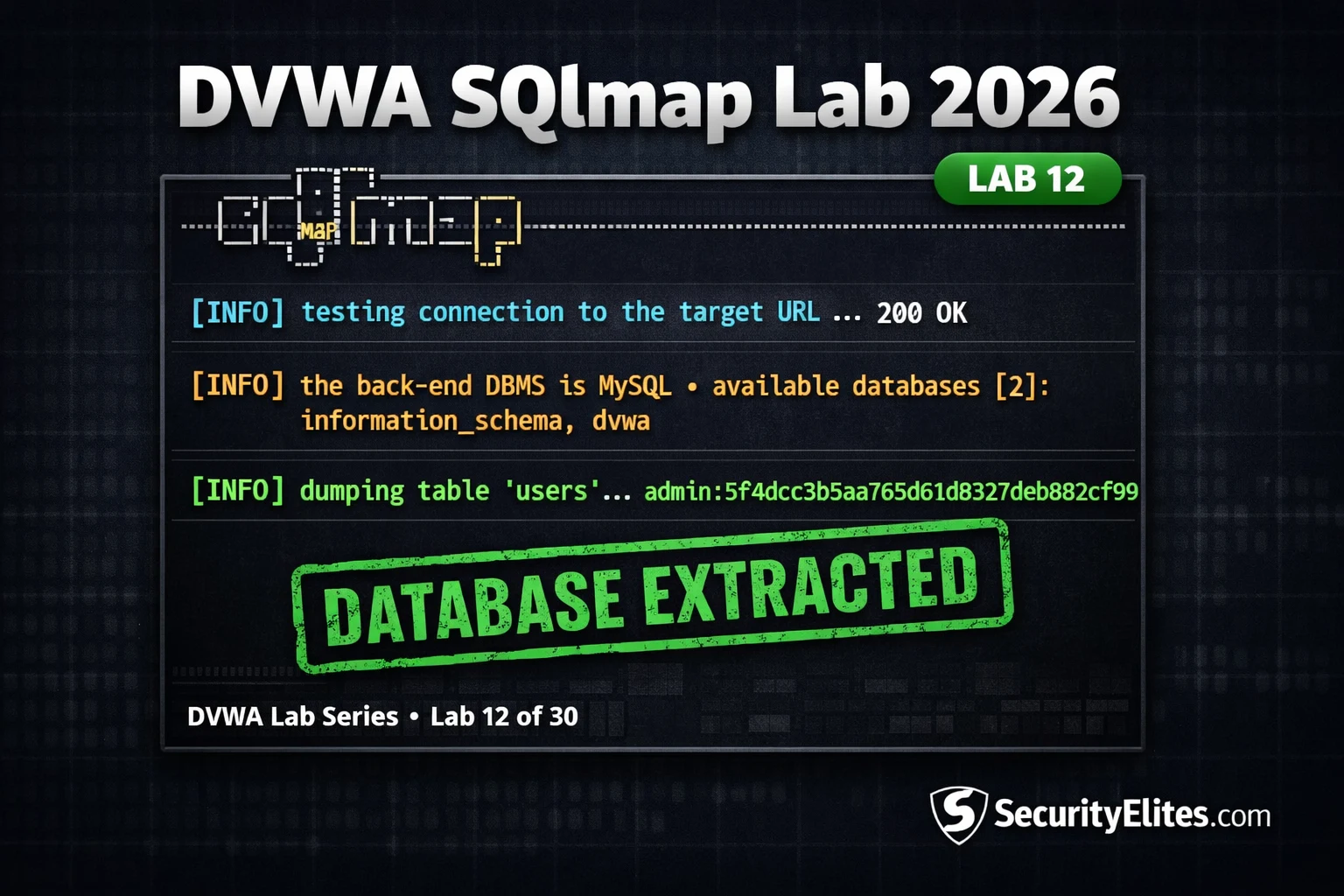
Lab12 : DVWA SQLmap Lab 2026 — The Exact SQLmap Workflow Hackers Use in 2026
DVWA SQLmap lab 2026 — automate complete database extraction using SQLmap against DVWA SQL injection. Tables, columns, data dump and…
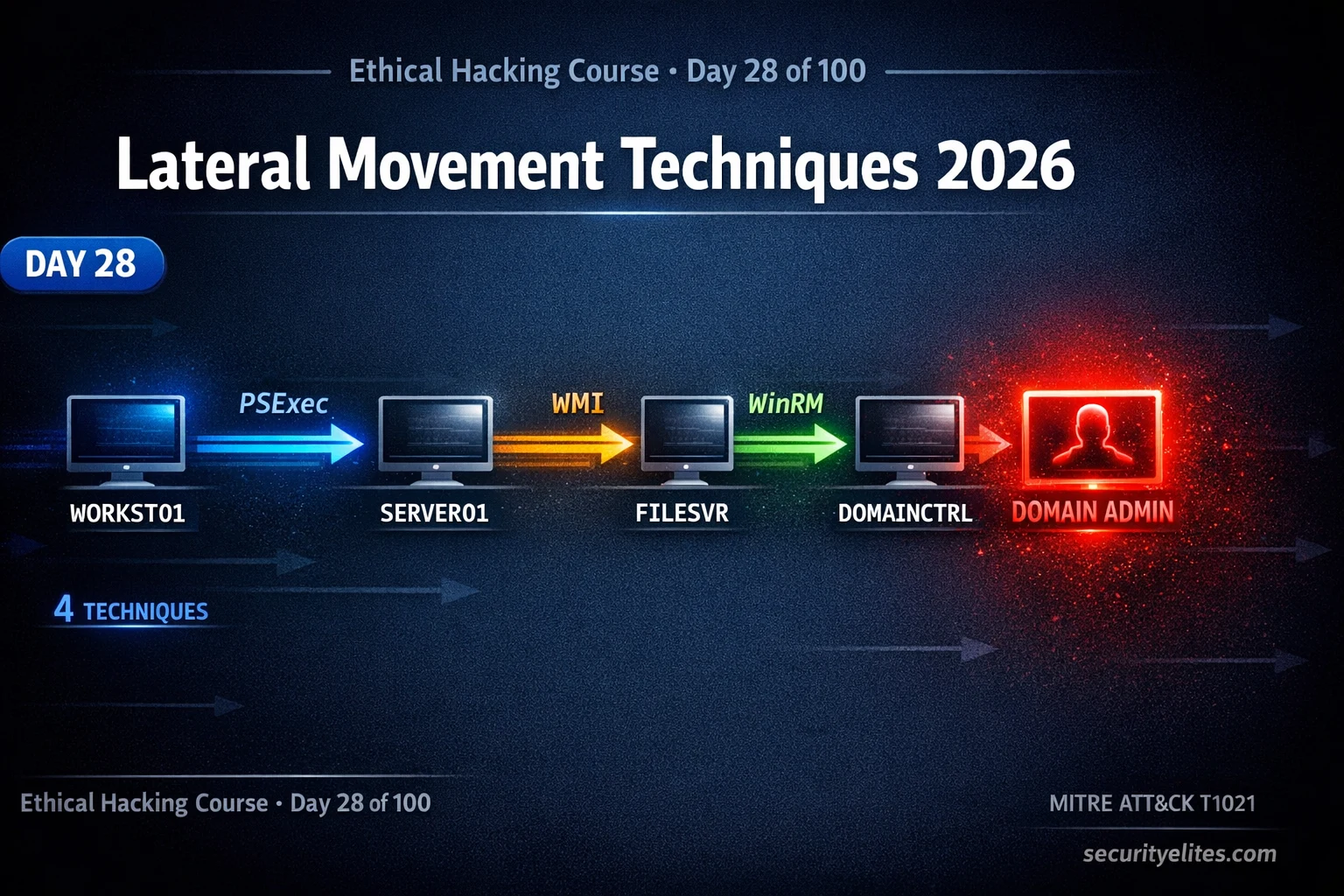
Lateral Movement Techniques 2026 — Execute Every BloodHound Attack Path in AD | Hacking Course Day 28
Lateral movement techniques 2026 — execute BloodHound attack paths using PSExec, WMI, WinRM and DCOM to move through Active Directory…
How Hackers Bypass 2FA in 2026 — 7 Methods That Still Work (Ethical Analysis)
How hackers bypass 2fa 2026 — 7 real methods used to circumvent two-factor authentication including SIM swapping, SS7 attacks, AiTM…
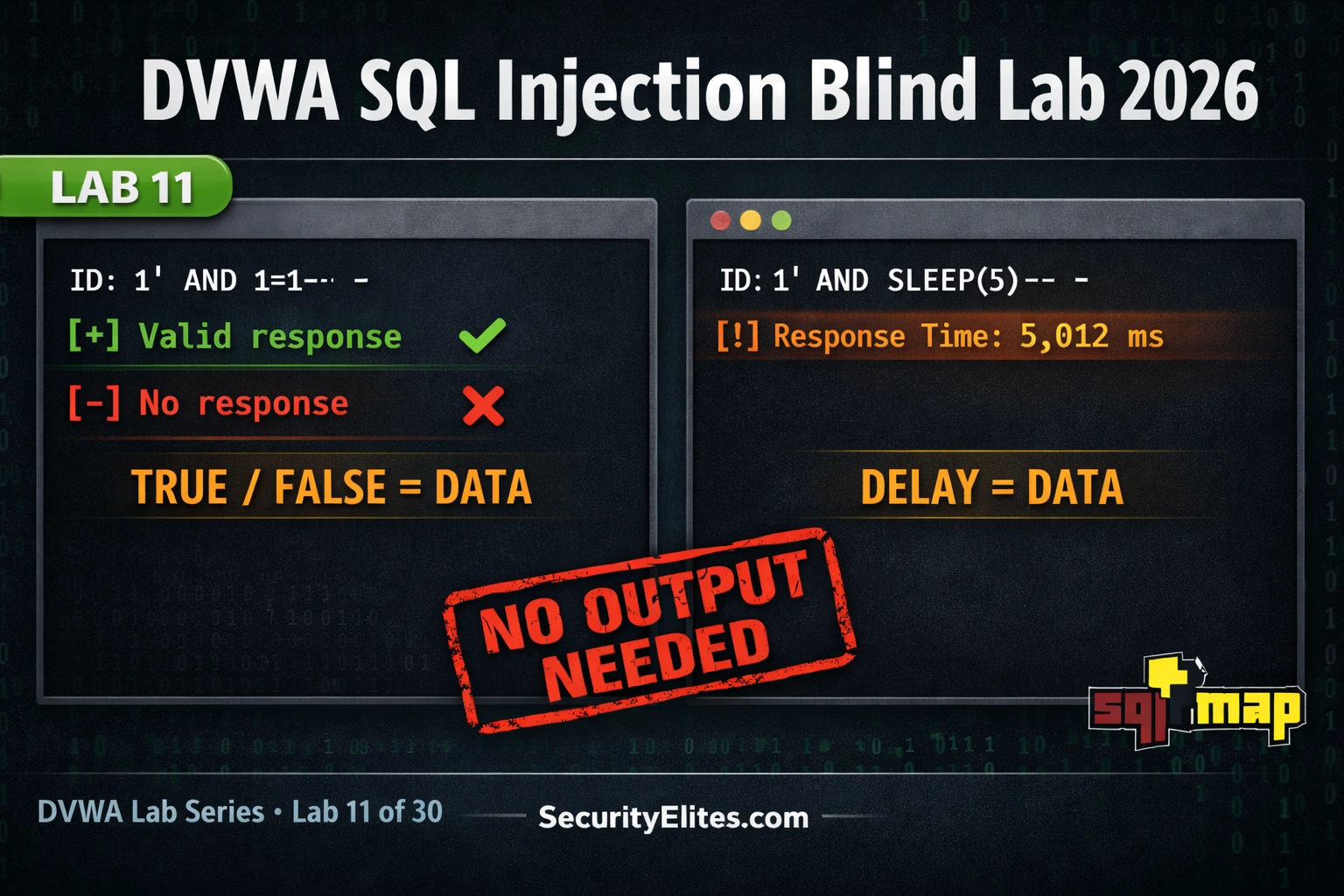
Lab11 : DVWA SQL Injection Blind Lab 2026 — Boolean and Time-Based Blind SQLi Guide
DVWA sql injection blind lab 2026 — extract database data using boolean-based and time-based blind techniques when no output is…
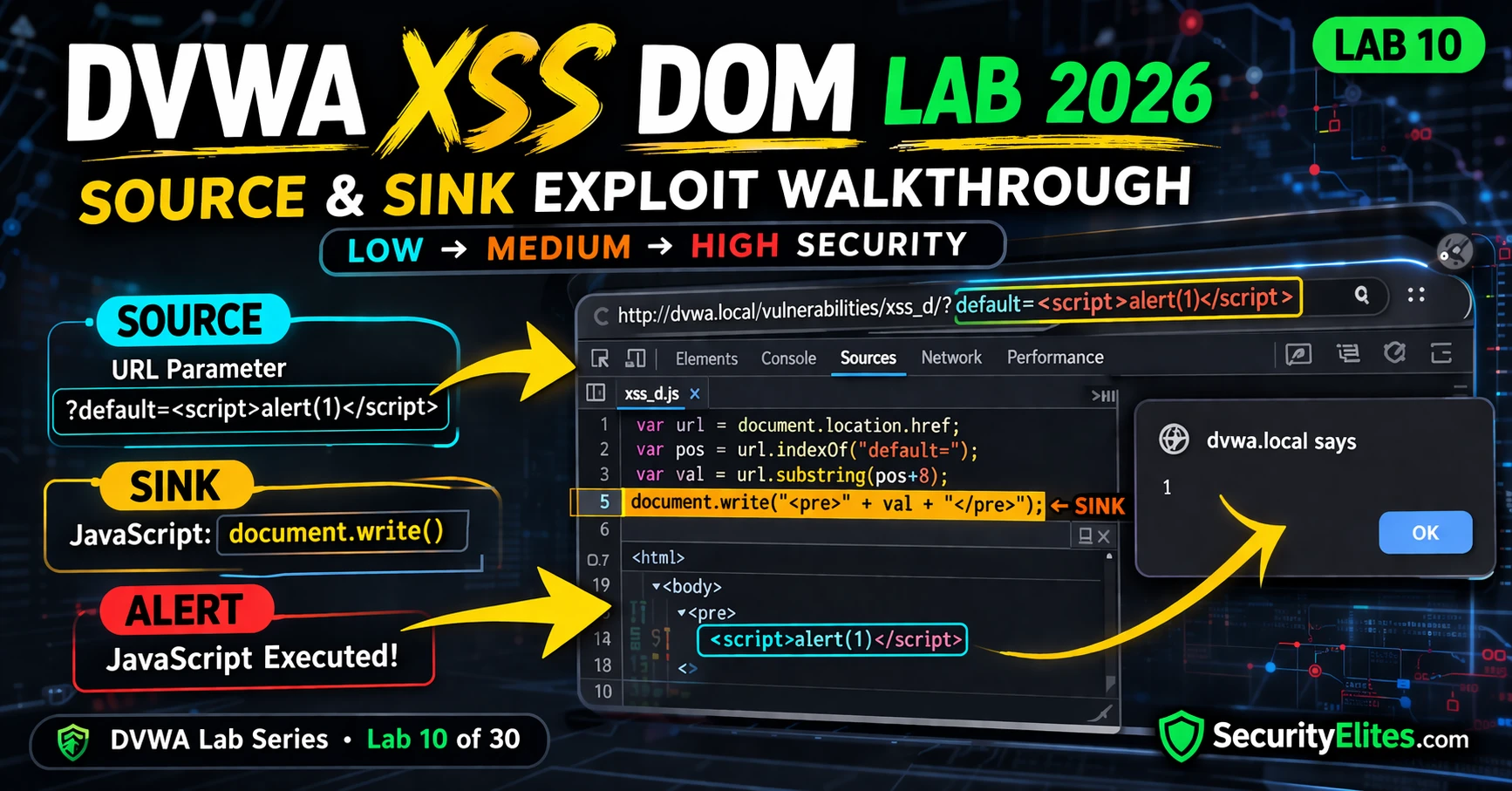
Lab 10: DVWA XSS DOM Lab 2026 — The Hidden Vulnerability You Can Exploit Instantly
DVWA XSS DOM lab 2026 — complete walkthrough for DOM-based cross-site scripting at Low, Medium and High security. Source and…