That’s because modern login pages don’t have one protection — they have layers. Rate limiting. Account lockout. CAPTCHA. MFA. IP reputation checks. The hunters consistently finding authentication bypass findings on major bug bounty programmes aren’t brute-forcing in the traditional sense. They’re testing whether each protection layer actually works, and finding the specific implementation flaws where one layer fails without breaking the others.
I’ve found rate limiting bypasses on FTSE 100 company login pages by adding a single header. I’ve found CAPTCHA token reuse on a financial services platform that meant the CAPTCHA provided exactly zero protection. I’ve found MFA OTP brute force on a healthcare portal with no rate limiting on the OTP entry form. These aren’t exotic attacks — they’re systematic testing of controls that developers implemented incorrectly. Here are the five that pay most consistently.
🎯 What You’ll Know After This
⏱️ 25 min read · applicable to your next bug bounty session
📋 How Hackers Brute Force Modern Login Pages – Contents
Bypass 1 — Rate Limit via IP Header Injection
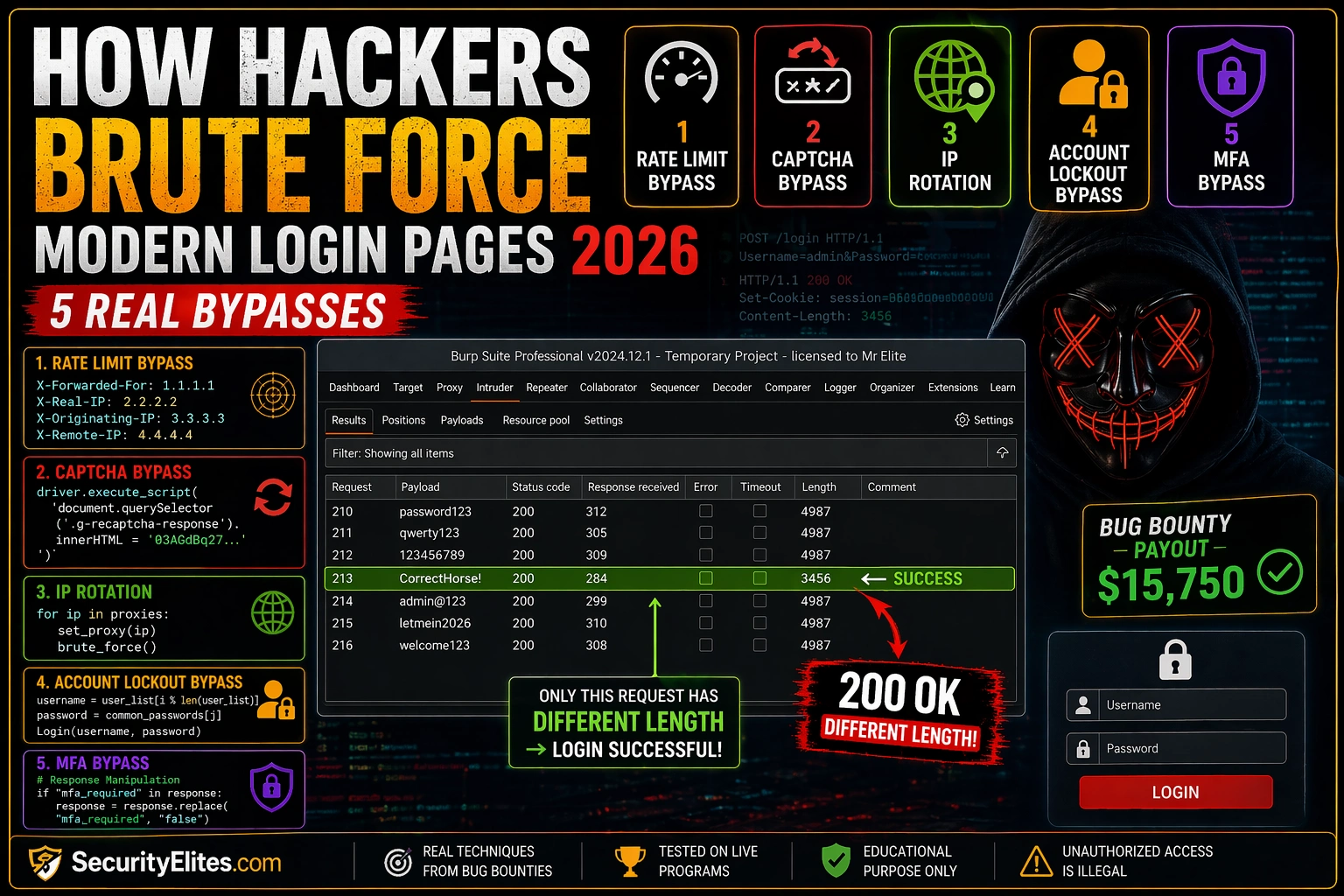
Rate limiting should track failed attempts by account, not by IP. But a lot of implementations track by source IP — because it’s simpler to implement. That implementation choice creates the bypass: if the application respects the X-Forwarded-For header as the source IP, rotating that header value resets your attempt counter.
The test takes two minutes. Add an X-Forwarded-For header with a fake IP to your login request. Confirm the application accepts it (no error). Then change the IP value and retry a failed attempt — does the failed attempt counter reset? If yes, the rate limiting is bypassable by anyone who can send custom headers. In Burp Intruder, use a Pitchfork attack type with one payload on the password field and one on the X-Forwarded-For value.
Bypass 2 — CAPTCHA Token Reuse
Most developers implement CAPTCHA by integrating Google reCAPTCHA or hCaptcha and checking that the response token is valid. What many don’t implement: checking that the token hasn’t been used before. A valid solved token should be single-use. If the server accepts the same token on multiple requests, CAPTCHA provides no protection against automated testing — you solve it once manually and replay that token indefinitely.
The test is trivial. Solve the CAPTCHA once normally, capture the g-recaptcha-response parameter in Burp, and replay the login request with that same value multiple times. If subsequent requests succeed despite the token being “used,” token reuse is confirmed.
Bypass 3 — Username Enumeration via Timing
Before brute-forcing anything, you want to know which usernames exist. The most reliable enumeration technique that survives normalised error messages is timing analysis. When you submit a valid username with a wrong password, the application does a database lookup, finds the account, then checks the password — that takes measurable time. When you submit an invalid username, the application either skips the password check or returns immediately — slightly faster.
The timing difference is often only 50-200ms, but it’s consistent. Run Burp Intruder with a username wordlist, constant wrong password, and sort results by response time. Valid usernames cluster at one timing band, invalid ones at another. On large user populations this gives you a confirmed valid username list before you attempt a single password.
Bypass 4 — Account Lockout Logic Flaws
Account lockout is often implemented with subtle logic errors. The most common: lockout per IP, not per account — already covered in Bypass 1. The second most common: the lockout counter doesn’t reset correctly. Test whether a correct password attempt resets the lockout counter, or whether it persists regardless of correct attempts in between. A counter that resets on any successful interaction (not just the same account) creates a bypass: alternate between correct and wrong passwords with the counter never reaching the threshold.
The most complete chain I’ve documented on a real engagement: timing analysis confirmed 340 valid usernames from a company’s login page. X-Forwarded-For rotation bypassed the 10-attempt rate limit. CAPTCHA token reuse eliminated the CAPTCHA layer entirely. Credential stuffing from a 2022 breach database against the valid username list returned 11 working account credentials. Six of those accounts had no MFA because they were contractor accounts the IT team had deprioritised in the MFA rollout. That’s a complete path from zero knowledge to eleven authenticated sessions — every step enabled by a different bypass finding, each one Medium-rated individually, collectively Critical. The report structure that got it triaged as Critical immediately: a numbered attack chain table showing exactly which bypass enabled which step, with the full impact at the bottom. Individual findings submitted separately would have been five Medium payouts. Submitted as a chain with documented impact: one Critical.
Password spraying is the anti-lockout technique. One password per account. Lockout triggers after N failed attempts per account. With one attempt per account, no individual account ever reaches N. Against an organisation with 500 employees, testing password “Summer2026!” against all 500 accounts triggers zero lockouts while finding anyone using that exact password.
Bypass 5 — MFA OTP Rate Limiting Absence
Here’s the MFA implementation flaw I find most consistently: rate limiting exists on the username/password form, but not on the OTP entry form. The developer secured the first step thoroughly and forgot the second step is also a brute-force surface. A 6-digit TOTP has 1,000,000 possible values. With no rate limiting on OTP entry, you can brute force it in under two minutes with automated requests.
The test: get past the first authentication step with valid credentials (your own test account), arrive at the OTP entry form, and send that form submission to Burp Intruder. Load a 6-digit number sequence as the payload. Start the attack and watch the response lengths. Any response with a different length from the “wrong OTP” baseline indicates a valid OTP or a different error — investigate it.
⏱️ 15 minutes · Browser only
The best way to understand what’s actually finding real payouts is reading the reports. Real bug bounty reports show exactly what the researcher tested, what they found, and what the impact was rated. Start here before testing anything yourself.
Go to: hackerone.com/hacktivity
Filter: Vulnerability type = “Improper Authentication”
Read 3 disclosed reports involving rate limiting or account lockout
Step 2: Search for CAPTCHA bypass reports
hackerone.com/hacktivity → search “CAPTCHA bypass”
What bypass technique was used in each report?
What was the CVSS score assigned?
Step 3: Search for MFA bypass reports
hackerone.com/hacktivity → search “MFA bypass” or “OTP bypass”
How many involve rate limiting on the OTP form specifically?
What’s the most common impact description?
Step 4: Find a credential stuffing or password spraying report
Search: “password spraying” OR “credential stuffing” site:hackerone.com
What organisational conditions made the attack successful?
Was account lockout present? If so, how was it bypassed?
Step 5: Calculate average payout
From your 5 reports: what was the median bounty amount?
What was the severity distribution (Low/Med/High/Critical)?
Which bypass type paid most consistently?
📸 Screenshot a disclosed rate limiting bypass report from HackerOne. Share in #bug-bounty
| # | Password | X-Forwarded-For | Status | Length |
| 1 | password123 | 10.0.0.1 | 200 | 842 |
| 2 | Summer2026! | 10.0.0.2 | 200 | 842 |
| 3 | Welcome@1 | 10.0.0.3 | 200 | 3847 |
| 4 | qwerty123 | 10.0.0.4 | 200 | 842 |
⏱️ 15 minutes · No tools needed
Before you run any of these tests on a real target, you need a systematic checklist that covers every protection layer without missing anything. Build it here, from scratch, using what you’ve just learned.
with exactly 10 items covering all 5 bypass types.
For each item, specify:
– What you’re testing (1 sentence)
– How you test it (specific technique or Burp tool)
– What outcome confirms vulnerability
Start with these categories and add 2 items per category:
1. Rate Limiting (2 tests)
2. CAPTCHA (2 tests)
3. Username Enumeration (2 tests)
4. Account Lockout (2 tests)
5. MFA (2 tests)
BONUS: For each vulnerability type, identify:
– Minimum Burp Suite tool needed to test it
– Approximate time to test (in minutes)
– Realistic CVSS range for a confirmed finding
CONSTRAINT: None of your tests should affect other users
in a production system. All tests use your own test accounts.
How does this constraint change any of your 10 test designs?
📸 Post your 10-item checklist in #bug-bounty. Get feedback on anything you missed.
Chaining: Enumeration + Bypass = Account Takeover
Individual authentication bypass findings rate Medium in most programmes. Chain them together and you’re at Critical. Here’s the chain I’ve demonstrated on real engagements: timing enumeration gives you a list of valid usernames → rate limit bypass via X-Forwarded-For gives you unlimited attempts → credential stuffing with breach data against those valid usernames → account takeover.
None of those individual findings is Critical in isolation. Together, the attack path goes from “I know nothing about the application” to “I have account access” without triggering a single protection. That’s the bug bounty report structure that generates Critical payouts: not one finding, but a documented chain with each step and the cumulative impact.
| Username | Status | Response Time | Length | Valid? |
| notauser | 200 | 48ms | 842 | No |
| alice | 200 | 312ms | 842 | Yes ← |
| fakeuser | 200 | 51ms | 842 | No |
| bob.smith | 200 | 298ms | 842 | Yes ← |
⏱️ 15 minutes · HackerOne or Bugcrowd account
Your next step after reading this article is finding a real target where authentication bypass testing is explicitly in scope. Here’s how to find the right programme.
hackerone.com/programs → filter by “authentication” in scope
Or search: programme policies mentioning “rate limiting”, “brute force”
Step 2: Read the programme policy carefully
Is brute force testing explicitly allowed or excluded?
What test account process does the programme require?
Is there a staging environment for testing?
Step 3: Find 3 programmes that explicitly allow authentication testing
Document: programme name, scope, test account method, bounty range
Step 4: For each programme, check disclosed reports
Has anyone already reported rate limiting bypass on this programme?
What was the outcome? Was it accepted or marked as informational?
Step 5: Choose one programme and complete the test account setup
Register a legitimate test account following the programme’s process
Note: some programmes require notifying them before authentication testing
Confirm the test account email is yours and the account is yours to test with
📸 Screenshot the programme policy section confirming authentication testing is in scope. Share in #bug-bounty
✅ 5 Authentication Bypass Techniques — Ready to Apply
Rate limit via IP header, CAPTCHA token reuse, timing enumeration, lockout logic flaws, MFA OTP rate limiting — five systematic tests, each applicable in under five minutes, each finding payouts consistently on major programmes. The next authentication form you encounter gets all five.
🧠 Quick Check
❓ Brute Force & Auth Bypass FAQ
How do hackers bypass rate limiting on login pages?
What is credential stuffing and how is it different from brute force?
Can CAPTCHAs be bypassed in bug bounty testing?
Is testing login page brute force protections legal for bug bounty?
What is password spraying?
What CVSS score does a rate limiting bypass get?
Gobuster vs ffuf vs Feroxbuster 2026
Social Engineering Scripts Pentesters Use
📚 Further Reading
- Day 22 — GraphQL Bug Bounty — GraphQL APIs frequently have weaker authentication controls than REST endpoints — the same systematic testing approach from this article applies directly to GraphQL login and auth mutations.
- Day 16 — Rate Limiting Bug Bounty — The dedicated rate limiting course module with additional bypass techniques covering non-login endpoints like password reset, OTP generation, and email verification flows.
- How Hackers Bypass 2FA in 2026 — Full coverage of MFA bypass beyond OTP brute force — SIM swapping, SS7 attacks, real-time phishing proxies, and session token theft after MFA completion.
- PortSwigger — Authentication Vulnerabilities Labs — Free lab environment covering every authentication bypass technique covered above with guided exercises and working solutions.
- HackerOne Hacktivity — Disclosed Reports — Search “rate limiting” or “CAPTCHA bypass” to read real disclosed reports — the fastest way to understand what these findings look like in practice and how triagers rate them.