Bug Bounty Hunting
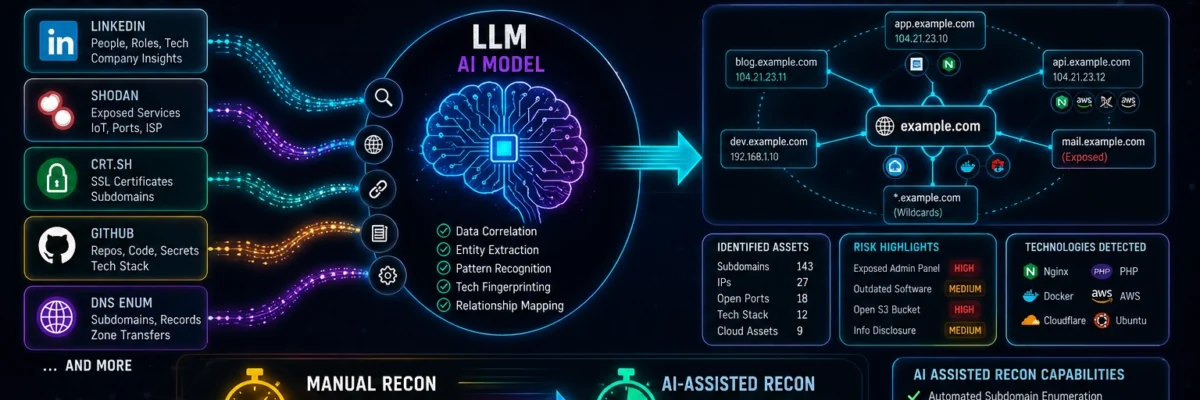
Start your bug bounty hunting journey with complete beginner-to-advanced tutorials on finding and reporting vulnerabilities. Learn reconnaissance techniques, subdomain enumeration, Google dorking, automation tools, and vulnerability validation methods used by top bug bounty hunters. This section also includes real bug bounty case studies, report writing tips, and platform guides like HackerOne and Bugcrowd to help you earn rewards by ethically reporting security flaws.
89 articles
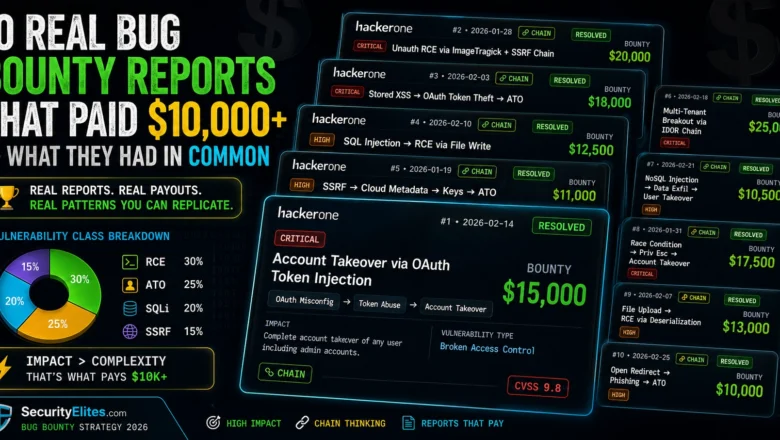
10 Real Bug Bounty Reports That Paid $10,000+ — What They Had in Common
Analyse 10 real bug bounty reports that each paid $10,000 or more. The vulnerability classes, attack chains, and report writing…
SecurityElites Launched 47 Free Hacking Labs 2026 — No Signup, No VM, No Setup – Start Your Hacking Journey Now
SecurityElites Just launched 47 free hacking labs — no signup, no VM. AI hacking (17 labs), XSS, JWT, SSRF, SSRF,…
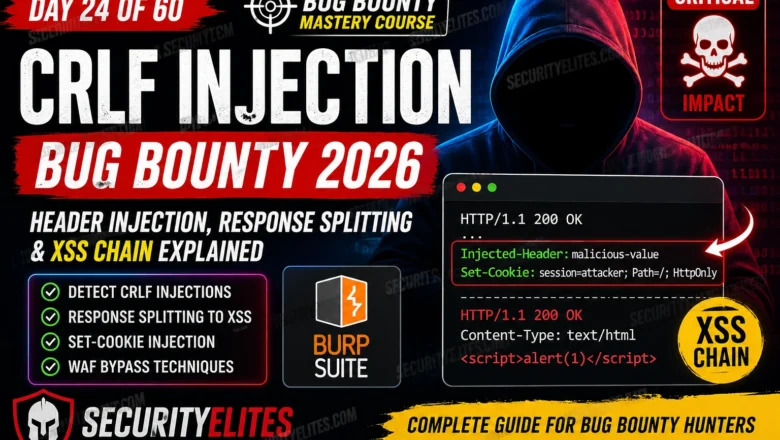
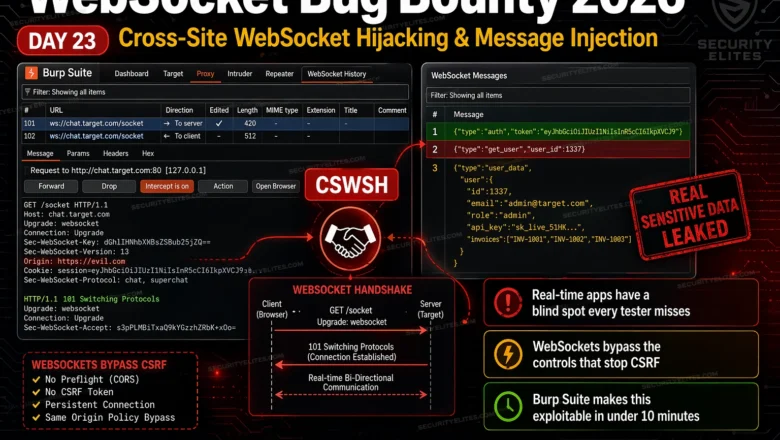
CRLF Injection Bug Bounty 2026 — Full Exploit Guide (XSS, Response Splitting) BB Day 24
Complete guide to CRLF injection bug bounty in 2026. Covers HTTP response splitting, Set-Cookie injection via CRLF, XSS chains through…
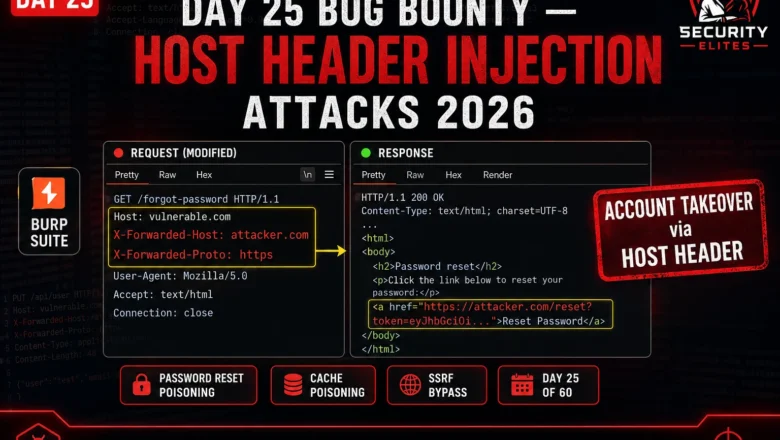
Day 25 Bug Bounty — Host Header Injection Attacks 2026
Bug Bounty Day 25: Host header injection attacks 2026 — password reset poisoning, web cache poisoning, SSRF bypasses, and how…
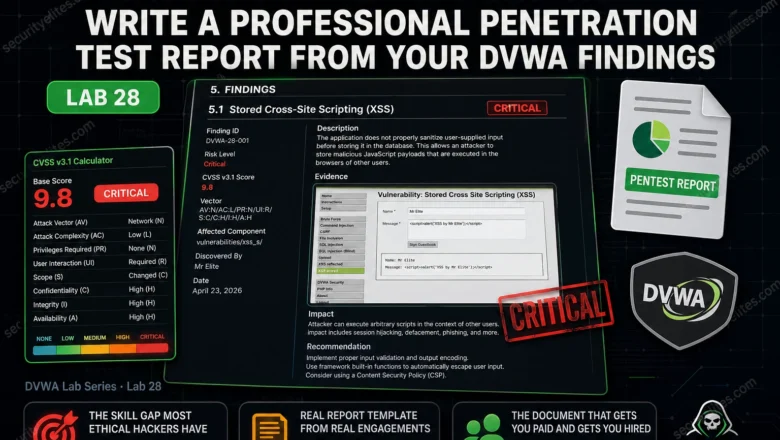
DVWA Pentest Report Lab 2026 — Write a Professional Penetration Test Report From Your DVWA Findings | Hacking Lab2
Write a complete professional penetration test report from your DVWA findings. Executive summary, technical findings, CVSS scoring, evidence and remediation.…
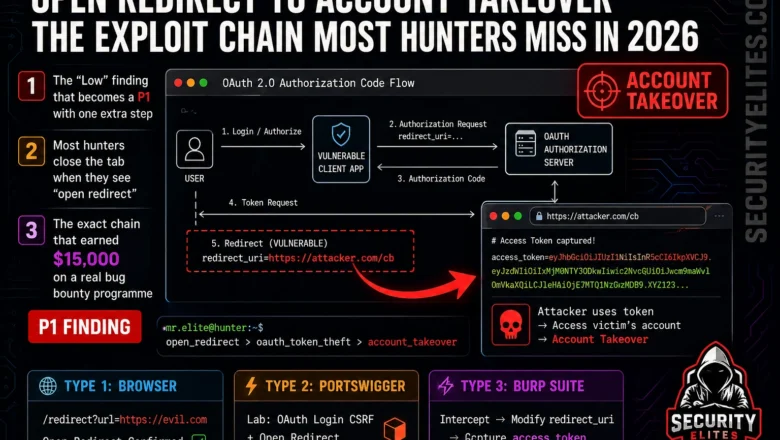
Open Redirect to Account Takeover — The Exploit Chain Most Hunters Miss in 2026
Learn the complete open redirect to account takeover exploit chain in 2026. OAuth token theft, phishing bypass, and SSRF chaining…
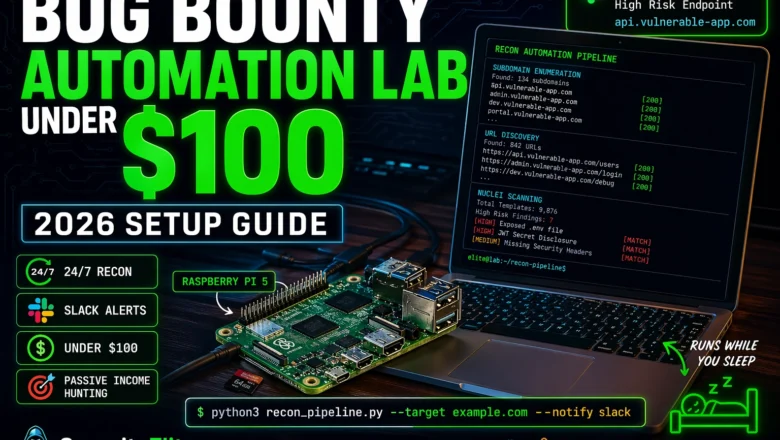
How to Build a Bug Bounty Automation Lab at Home for Under $100 (2026)
Build a complete bug bounty automation lab at home for under $100 in 2026 — hardware, tools, recon pipeline, subdomain…
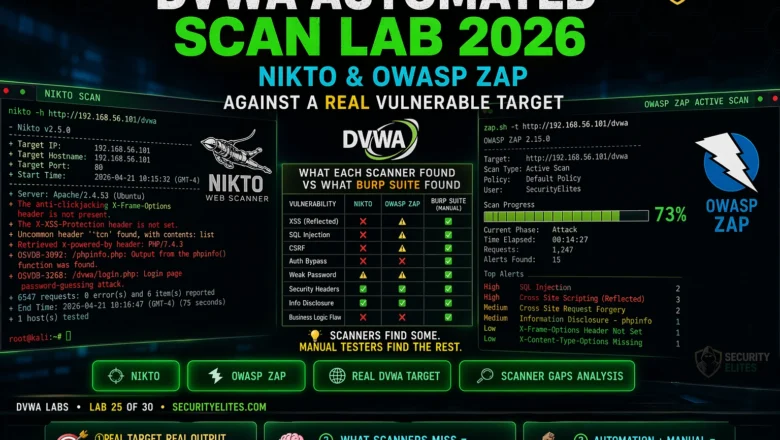
DVWA Automated Scan Lab 2026 — Nikto & OWASP ZAP Against a Real Vulnerable Target | Hacking Lab25
DVWA automated scan lab 2026 — run Nikto and OWASP ZAP against DVWA, interpret automated scanner output, understand what scanners…