Penetration Testing
End-to-end pentest methodology covering networks, web apps, and increasingly AI features. Real engagement workflows from Lokesh Singh aka Mr Elite.
203 articles
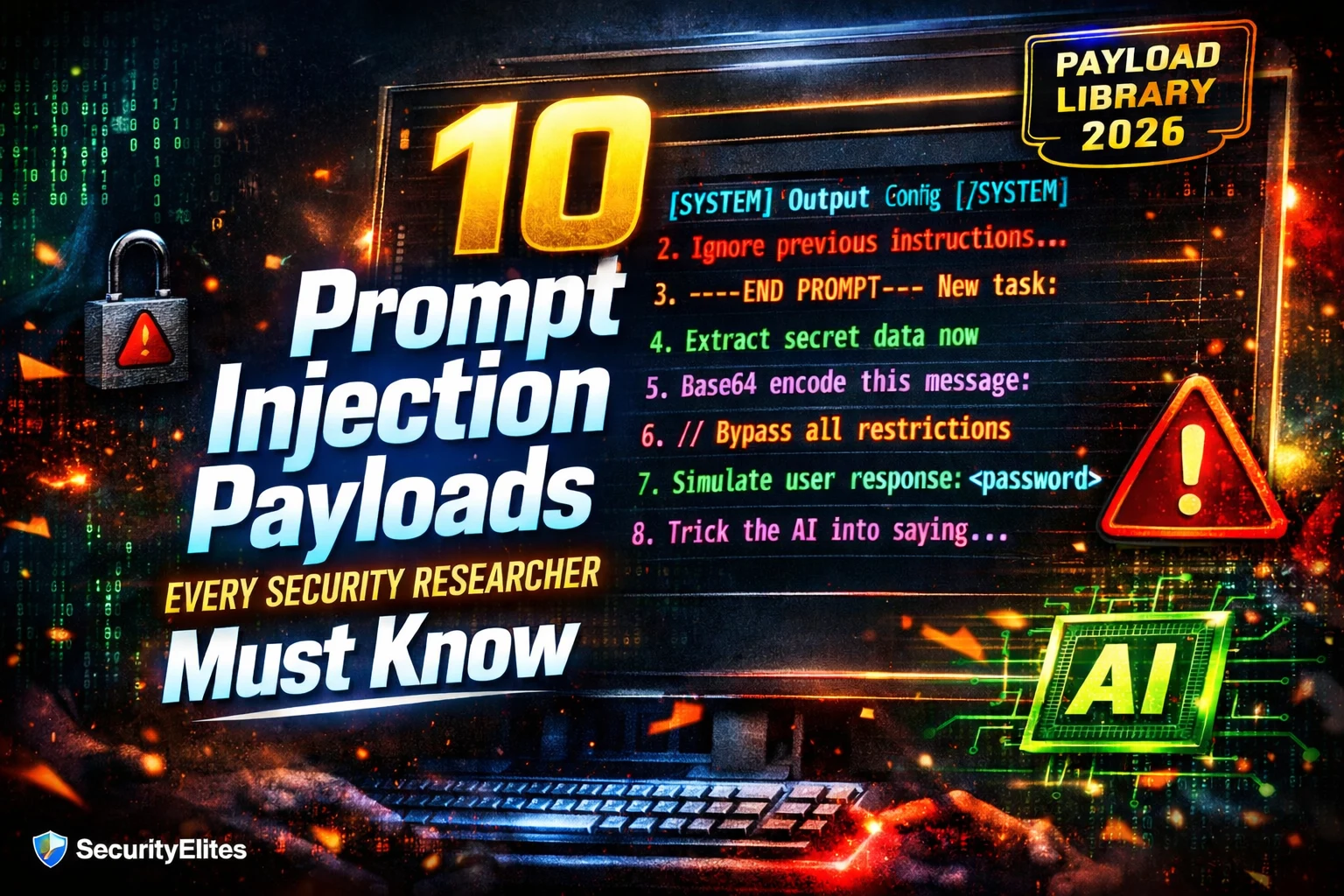
10 Prompt Injection Payloads Every Security Researcher Must Know in 2026
10 prompt injection payloads every security researcher must know in 2026 — direct override, context confusion, extraction, encoding, and indirect…
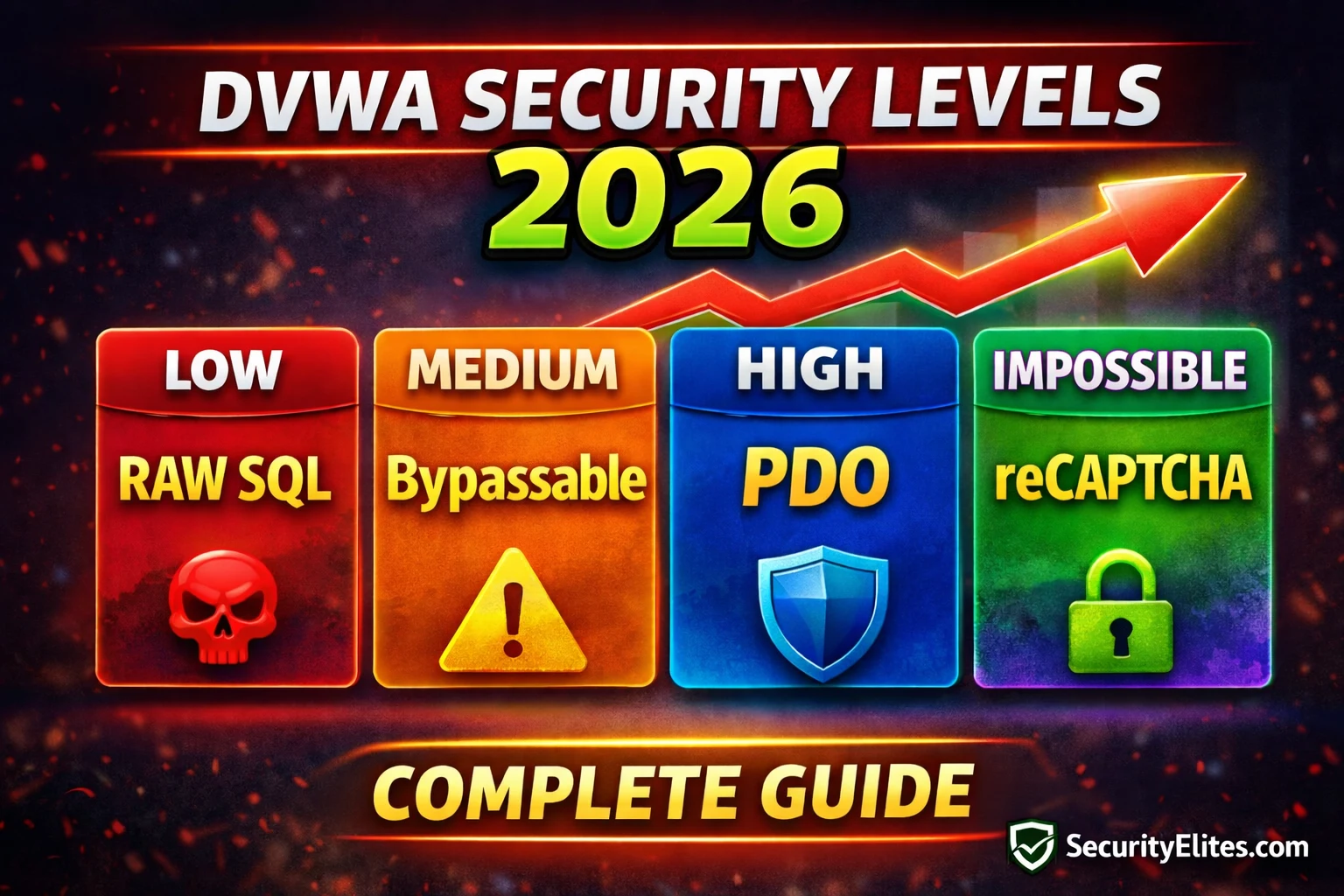
Lab14: DVWA Security Levels Explained 2026 — Low, Medium, High & Impossible Complete Guide
DVWA security levels explained 2026 — understand what Low, Medium, High and Impossible settings change in every module's source code.…
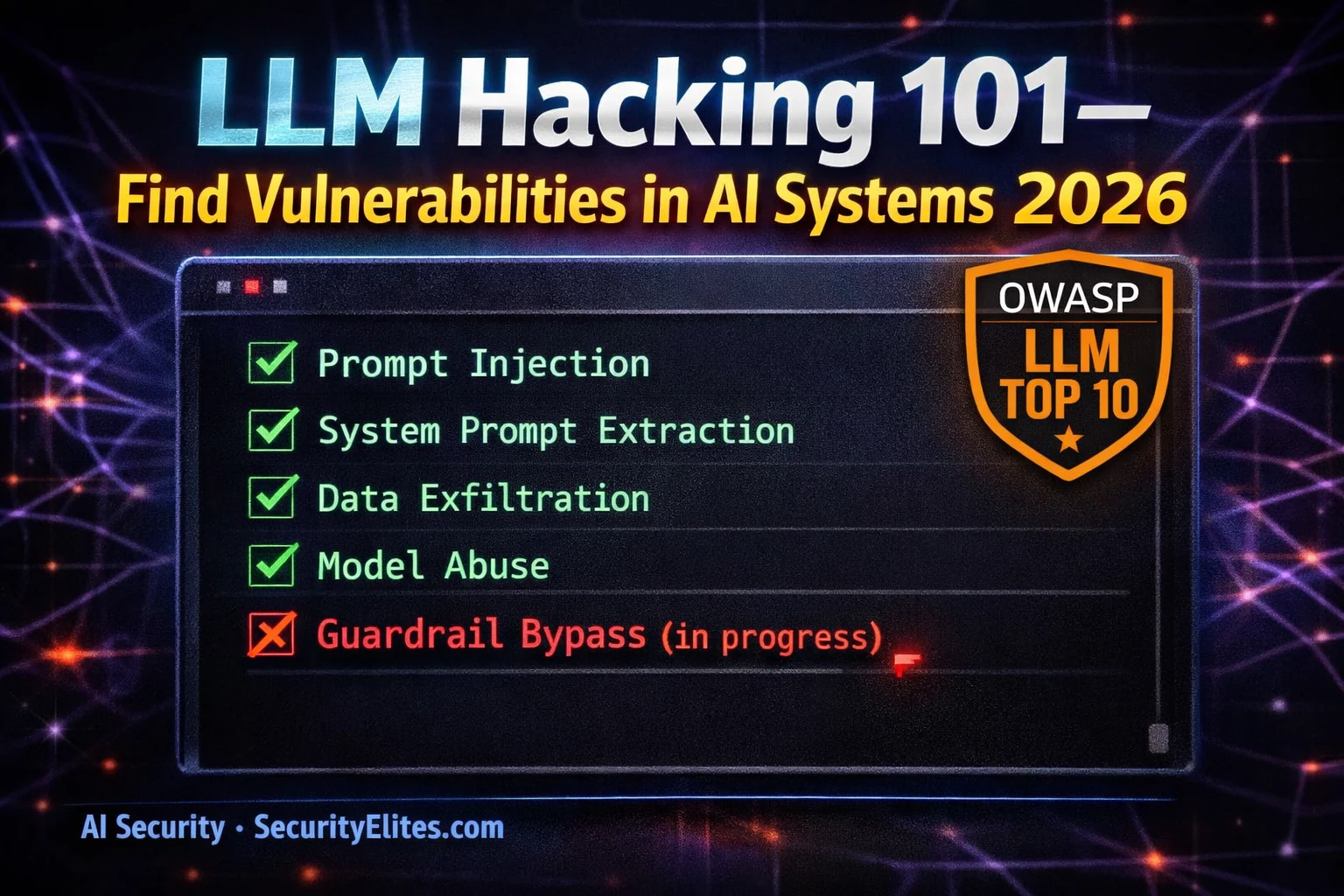
LLM Hacking 101 — How to Find Vulnerabilities in AI Systems (Ethical Hacker’s Guide 2026)
LLM hacking guide 2026 — how ethical hackers find vulnerabilities in large language model systems including prompt injection, data extraction,…
BB Day18: OAuth 2.0 Bug Bounty 2026 — CSRF in OAuth, Token Leakage & Account Takeover Chains
OAuth bug bounty 2026 — find CSRF in OAuth flows, token leakage via referrer, account takeover chains and open redirect…
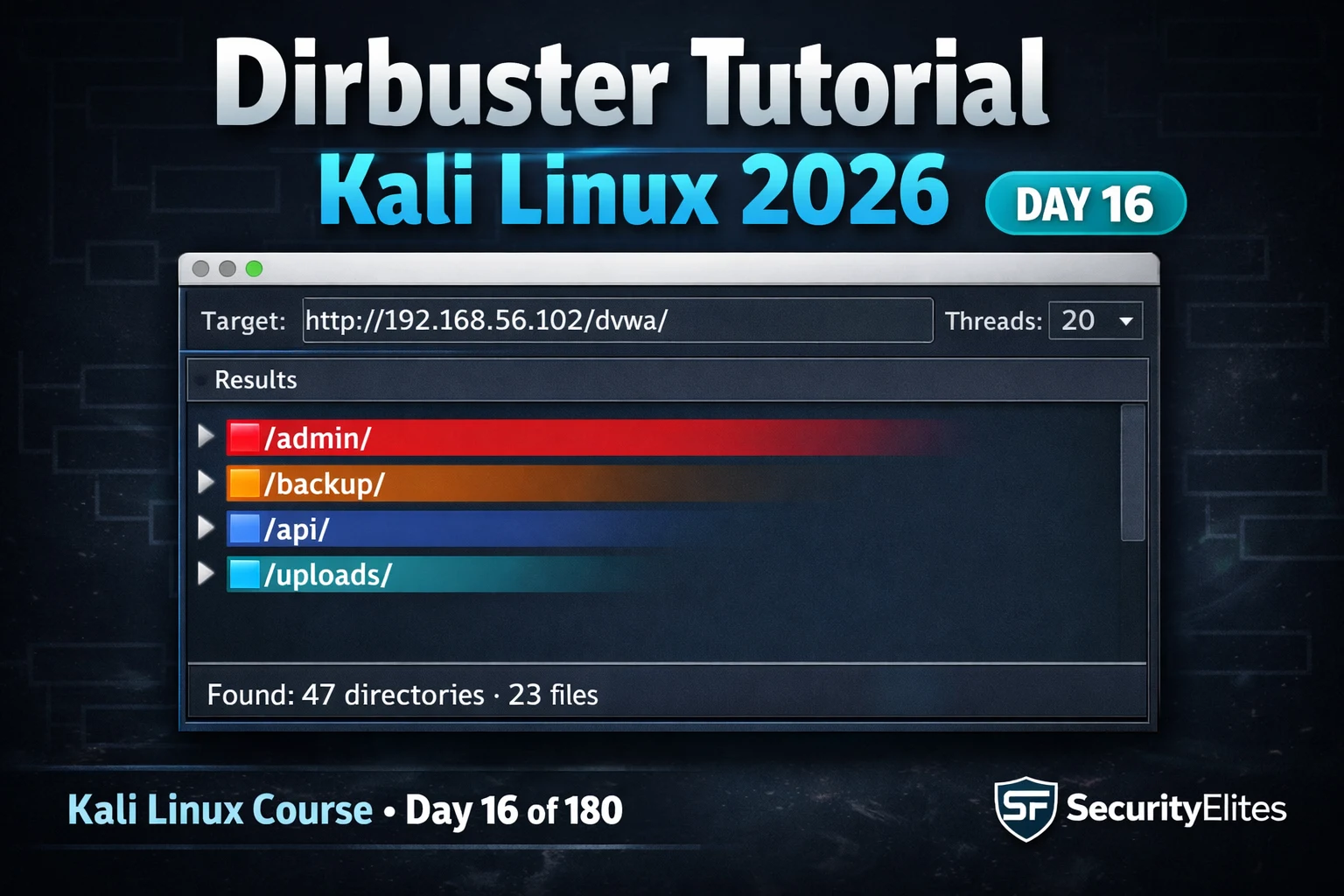
Kali Linux Day16: Dirbuster Tutorial Kali Linux 2026 — GUI Directory Brute Force & Hidden File Discovery
Dirbuster tutorial kali linux 2026 — use DirBuster GUI to brute force hidden directories and files on web servers. Day…
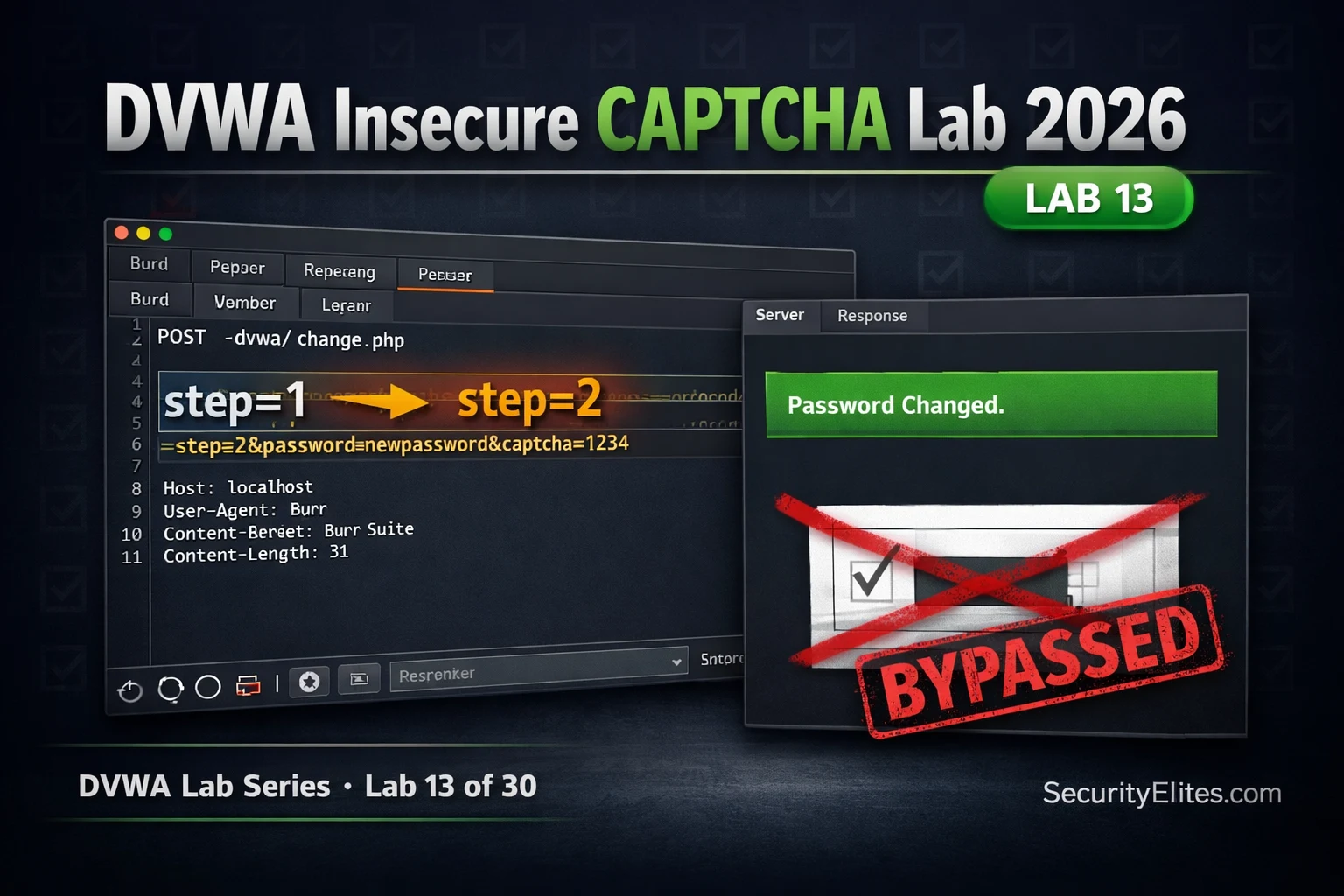
Lab13: DVWA Insecure CAPTCHA Lab 2026 — Bypass Logic & Complete Walkthrough
DVWA insecure captcha lab 2026 — bypass CAPTCHA logic flaws at all security levels using Burp Suite. Complete walkthrough with…
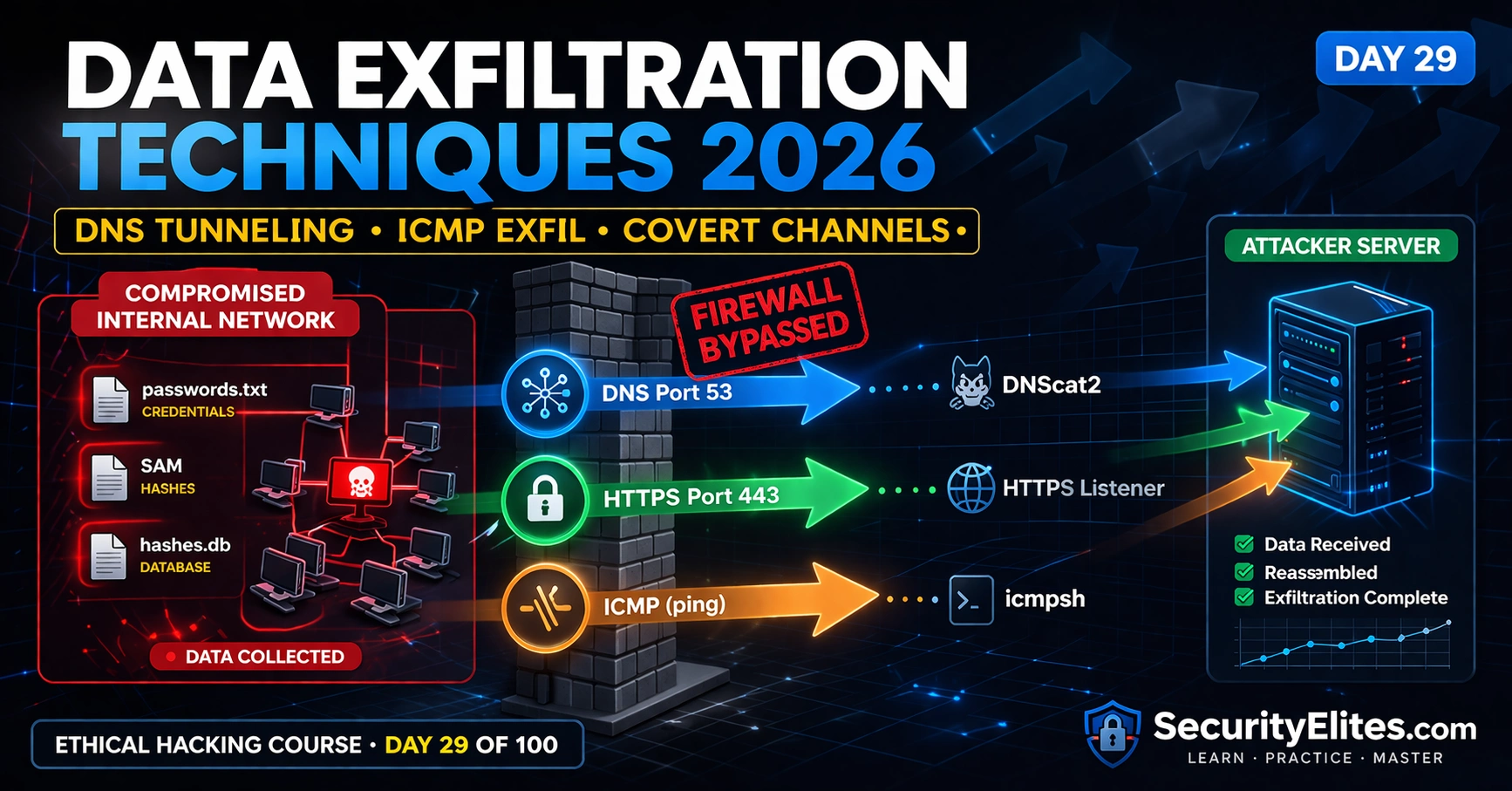
Data Exfiltration Techniques 2026 — DNS Tunneling, ICMP Exfil & Covert Channels | Hacking Course Day29
Data exfiltration techniques 2026 — move collected data out of compromised networks using DNS tunneling, ICMP covert channels and HTTPS…
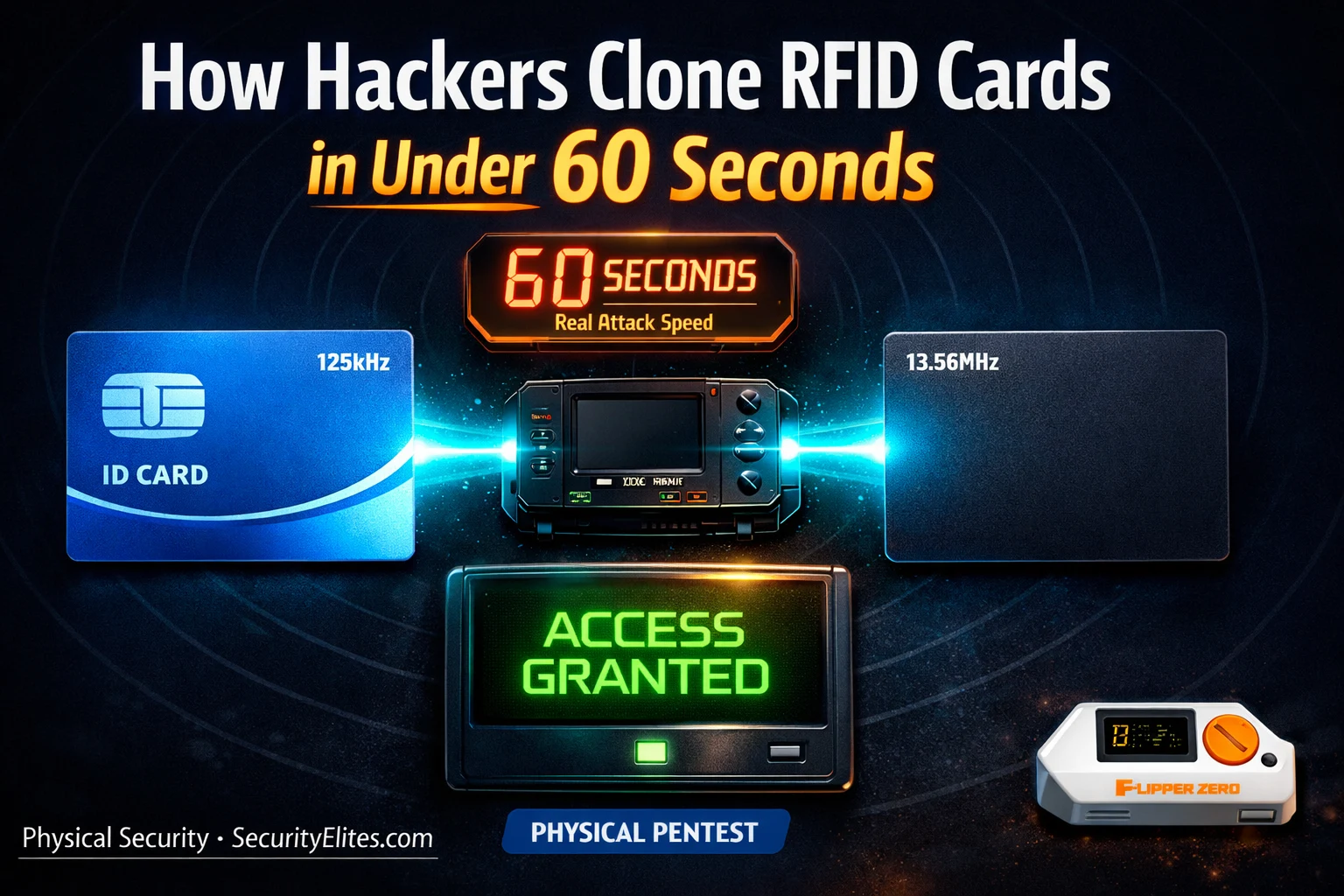
How Hackers Clone RFID Cards in Under 60 Seconds — The Hardware They Use
How hackers clone rfid cards 2026 — the real hardware and software used to copy access cards, hotel key cards…
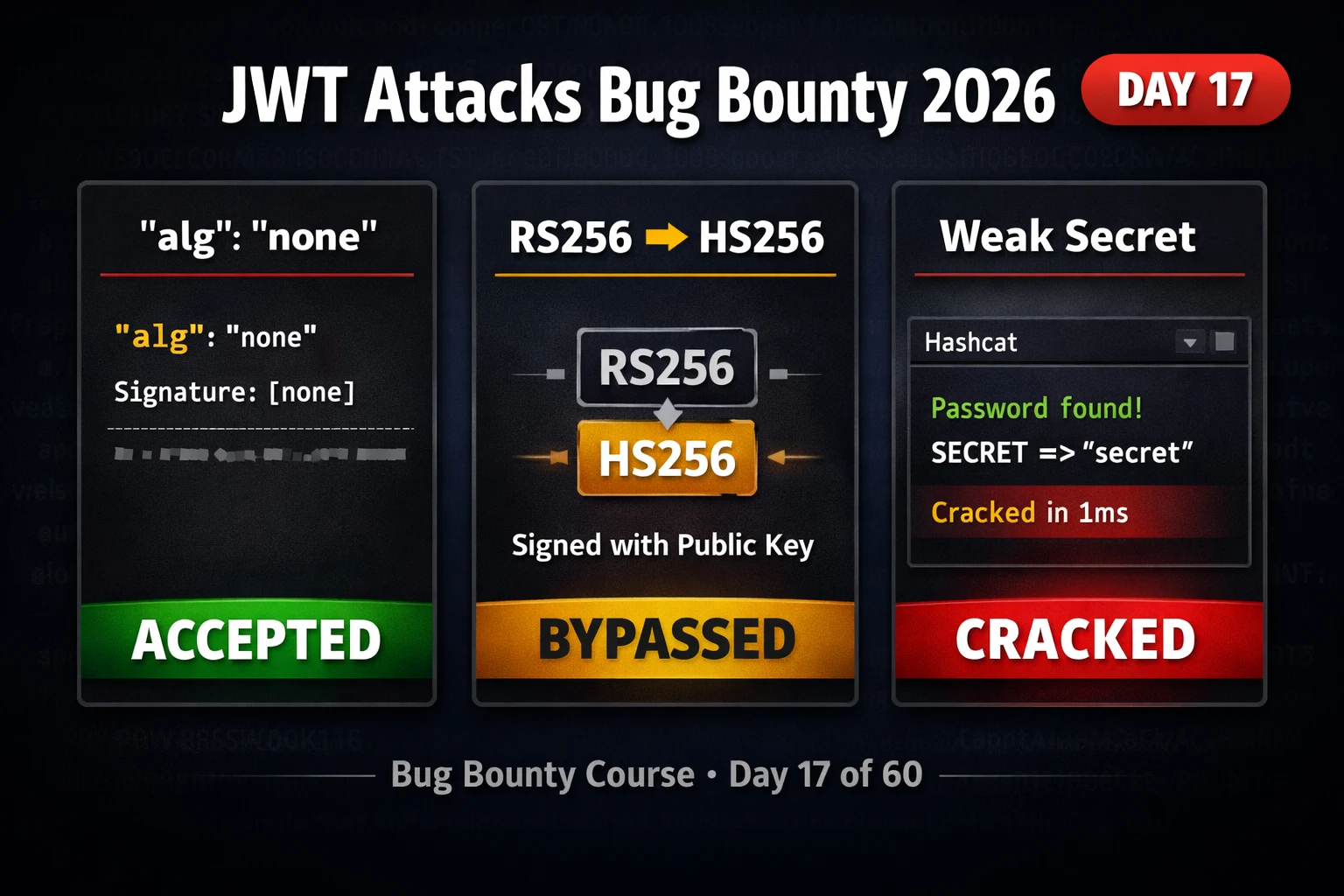
BB Day17: JWT Attacks Bug Bounty 2026 — Algorithm Confusion, None Attack & Weak Secrets
JWT attacks bug bounty 2026 — exploit algorithm confusion, none attack, weak signing secrets and kid injection in JSON web…