Penetration Testing
End-to-end pentest methodology covering networks, web apps, and increasingly AI features. Real engagement workflows from Lokesh Singh aka Mr Elite.
203 articles
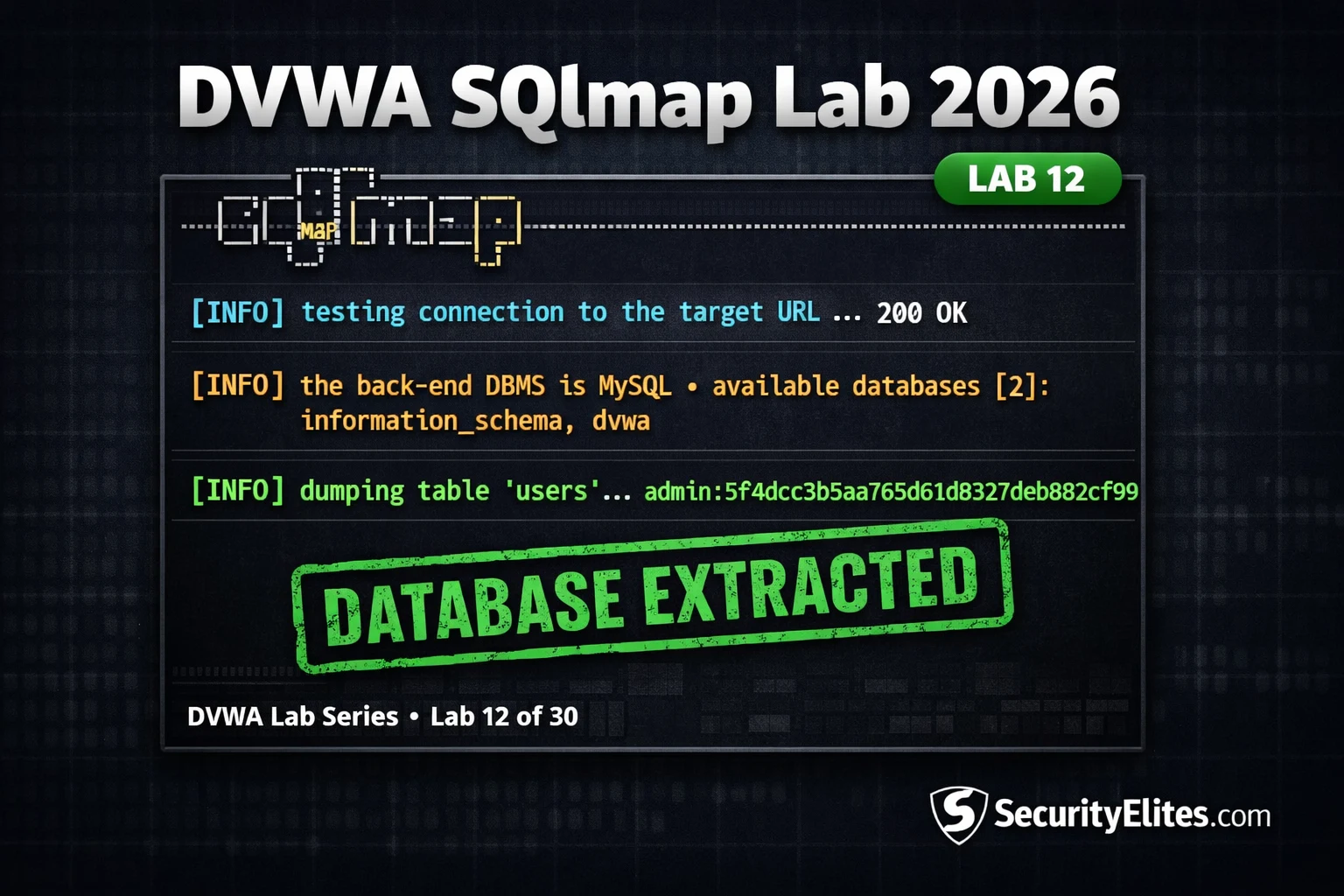
Lab12 : DVWA SQLmap Lab 2026 — The Exact SQLmap Workflow Hackers Use in 2026
DVWA SQLmap lab 2026 — automate complete database extraction using SQLmap against DVWA SQL injection. Tables, columns, data dump and…
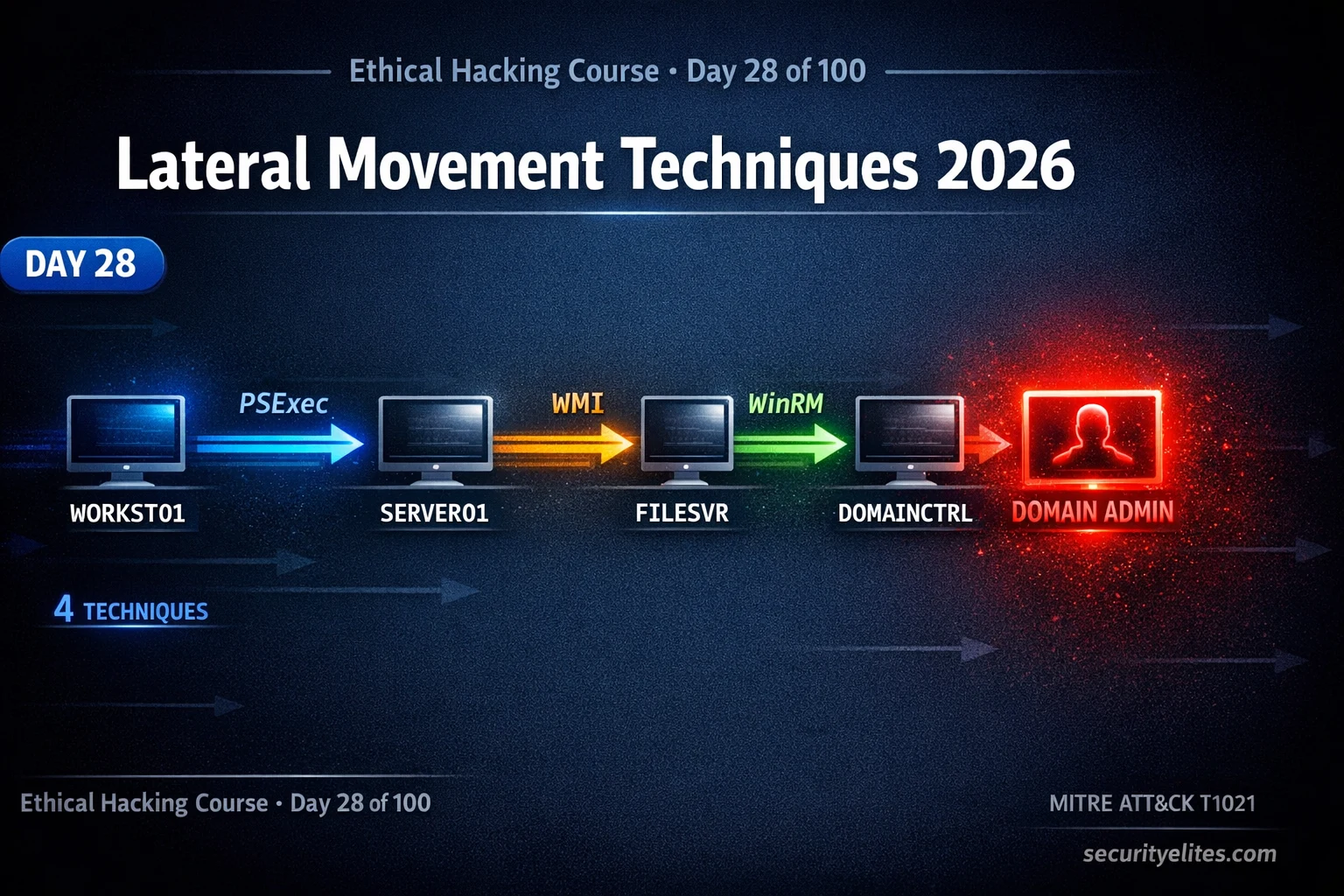
Lateral Movement Techniques 2026 — Execute Every BloodHound Attack Path in AD | Hacking Course Day 28
Lateral movement techniques 2026 — execute BloodHound attack paths using PSExec, WMI, WinRM and DCOM to move through Active Directory…
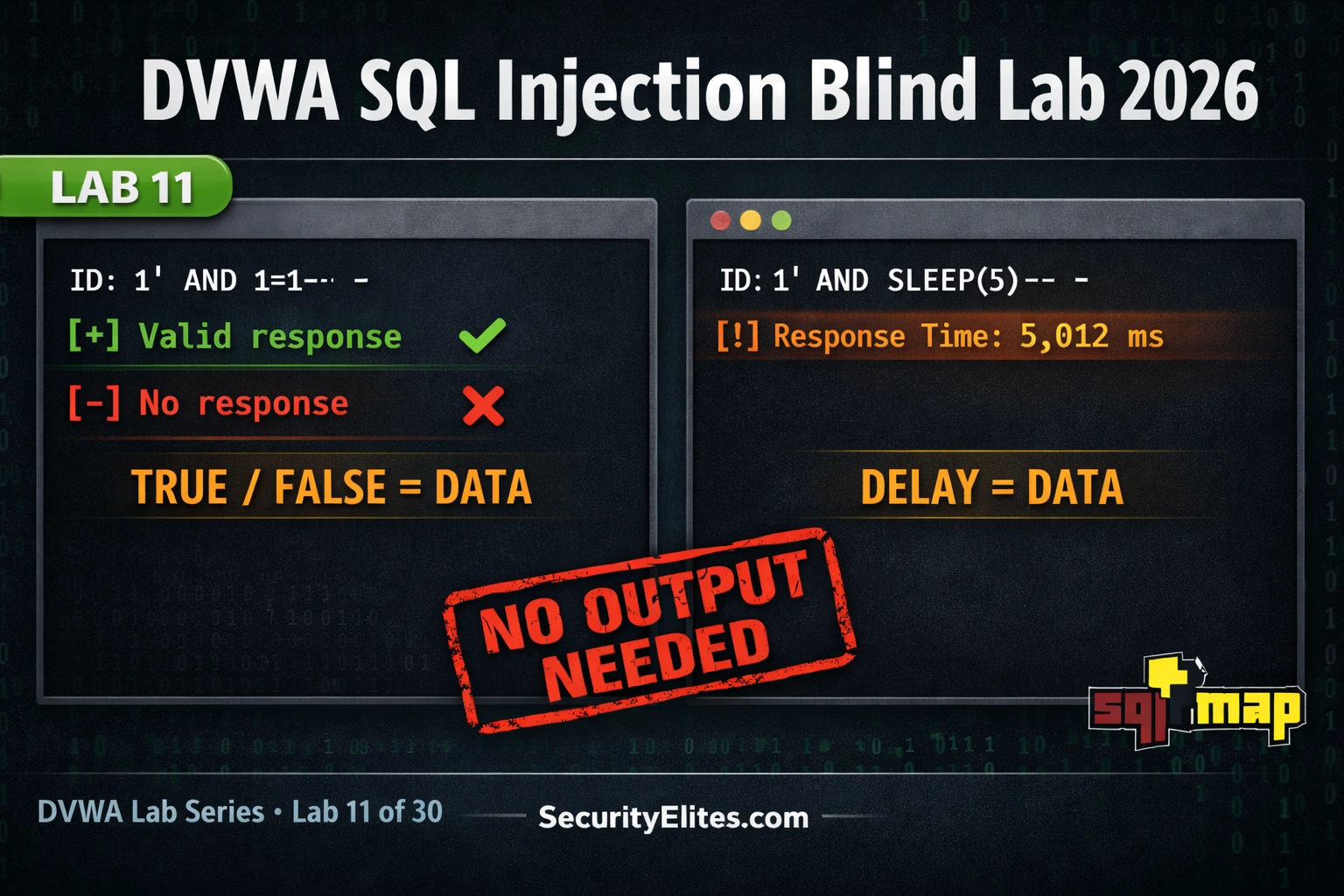
Lab11 : DVWA SQL Injection Blind Lab 2026 — Boolean and Time-Based Blind SQLi Guide
DVWA sql injection blind lab 2026 — extract database data using boolean-based and time-based blind techniques when no output is…
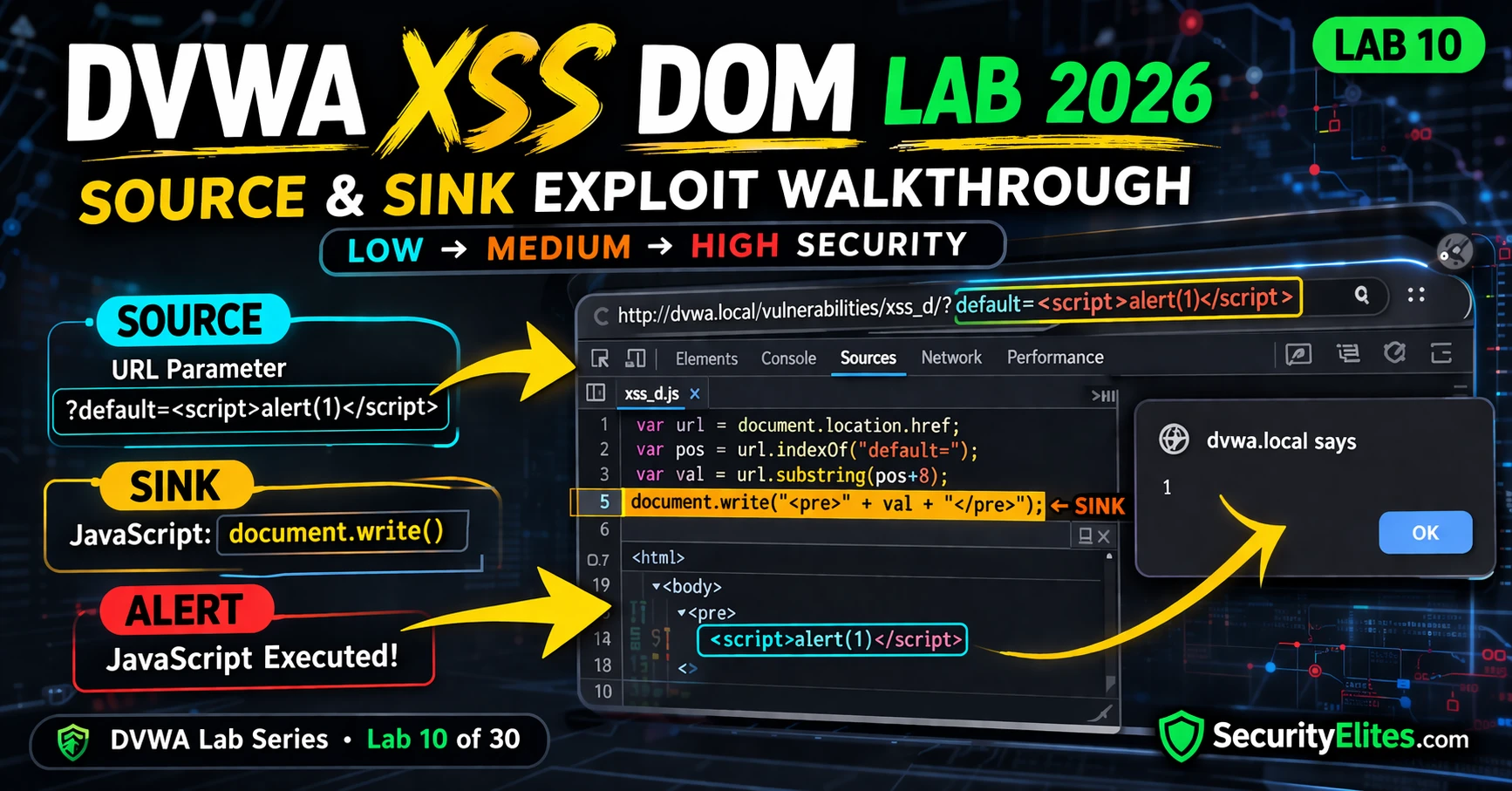
Lab 10: DVWA XSS DOM Lab 2026 — The Hidden Vulnerability You Can Exploit Instantly
DVWA XSS DOM lab 2026 — complete walkthrough for DOM-based cross-site scripting at Low, Medium and High security. Source and…
How to Use Shodan 2026 — The Hacker’s Search Engine Complete Guide
How to use shodan 2026 — search internet-connected devices, find exposed services, use Shodan dorks for bug bounty recon and…
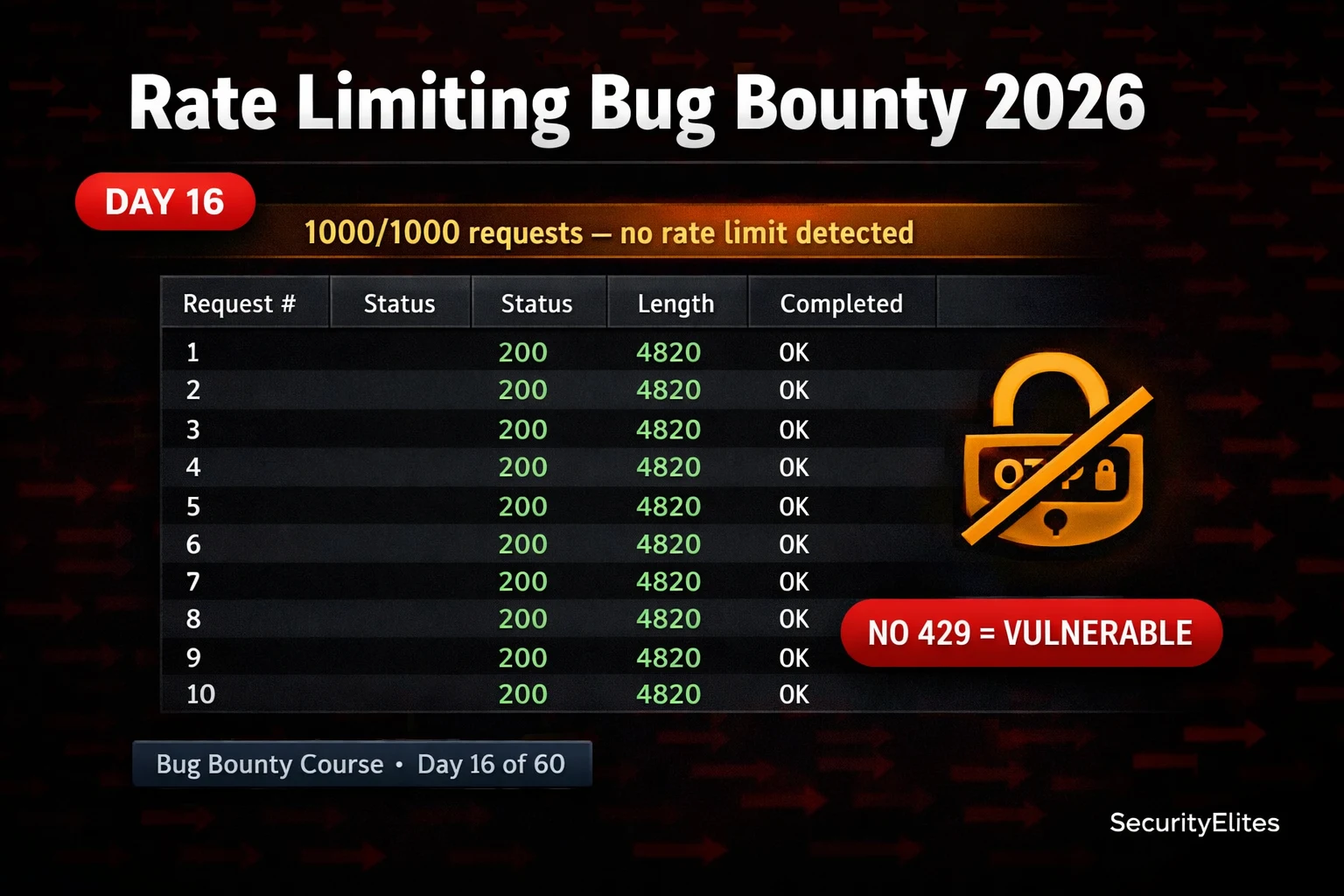
BB Day16: Rate Limiting Bug Bounty 2026 — Find Bypass Flaws in Login, OTP and API Endpoints
Rate limiting bug bounty 2026 — find and exploit missing or bypassable rate limits on login, OTP, password reset and…
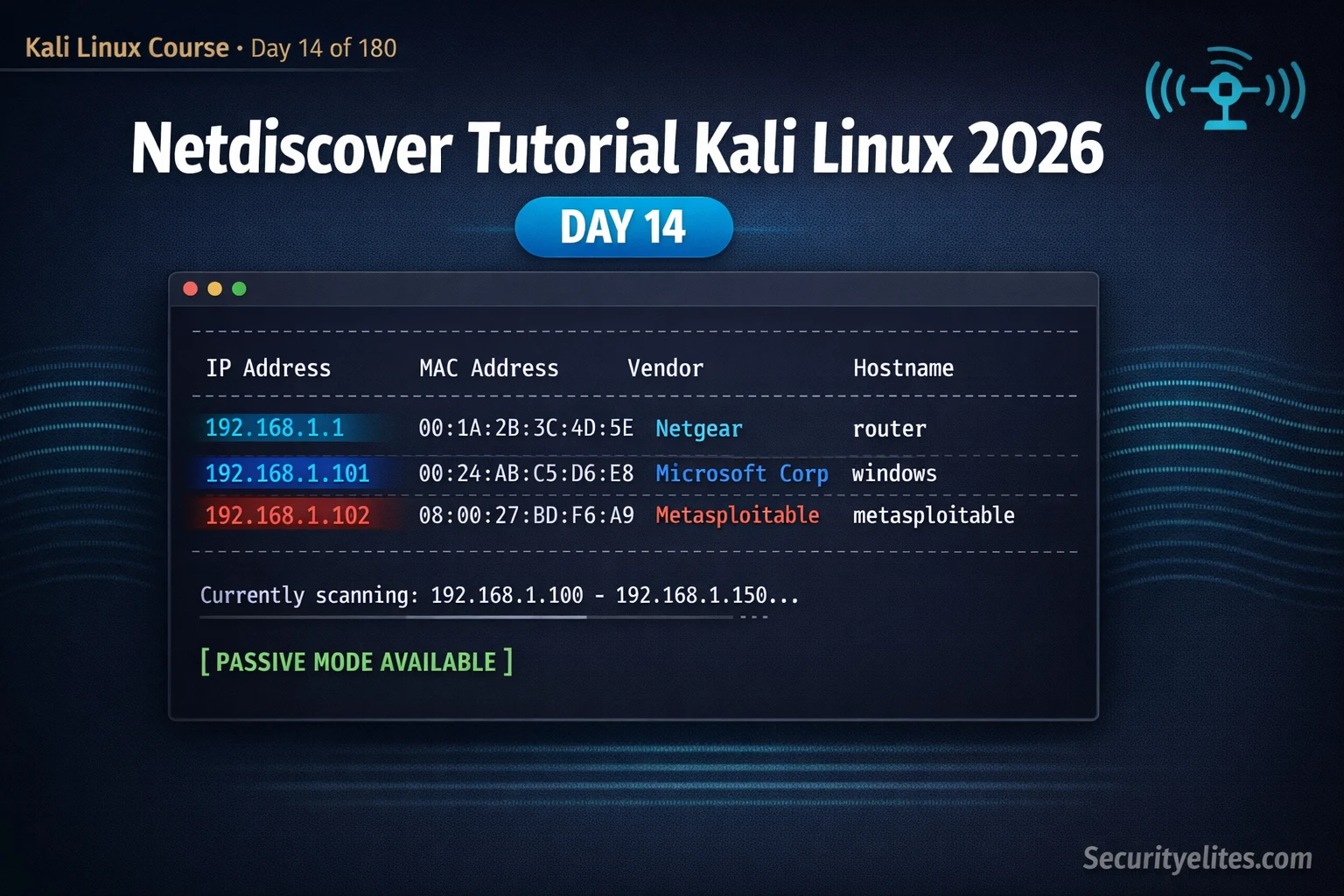
Kali Linux Day14: Netdiscover Tutorial Kali Linux 2026 — Instantly Discover Every Device on Your Network
Netdiscover tutorial kali linux 2026 — discover live hosts on local networks using ARP scanning, passive mode and IP range…
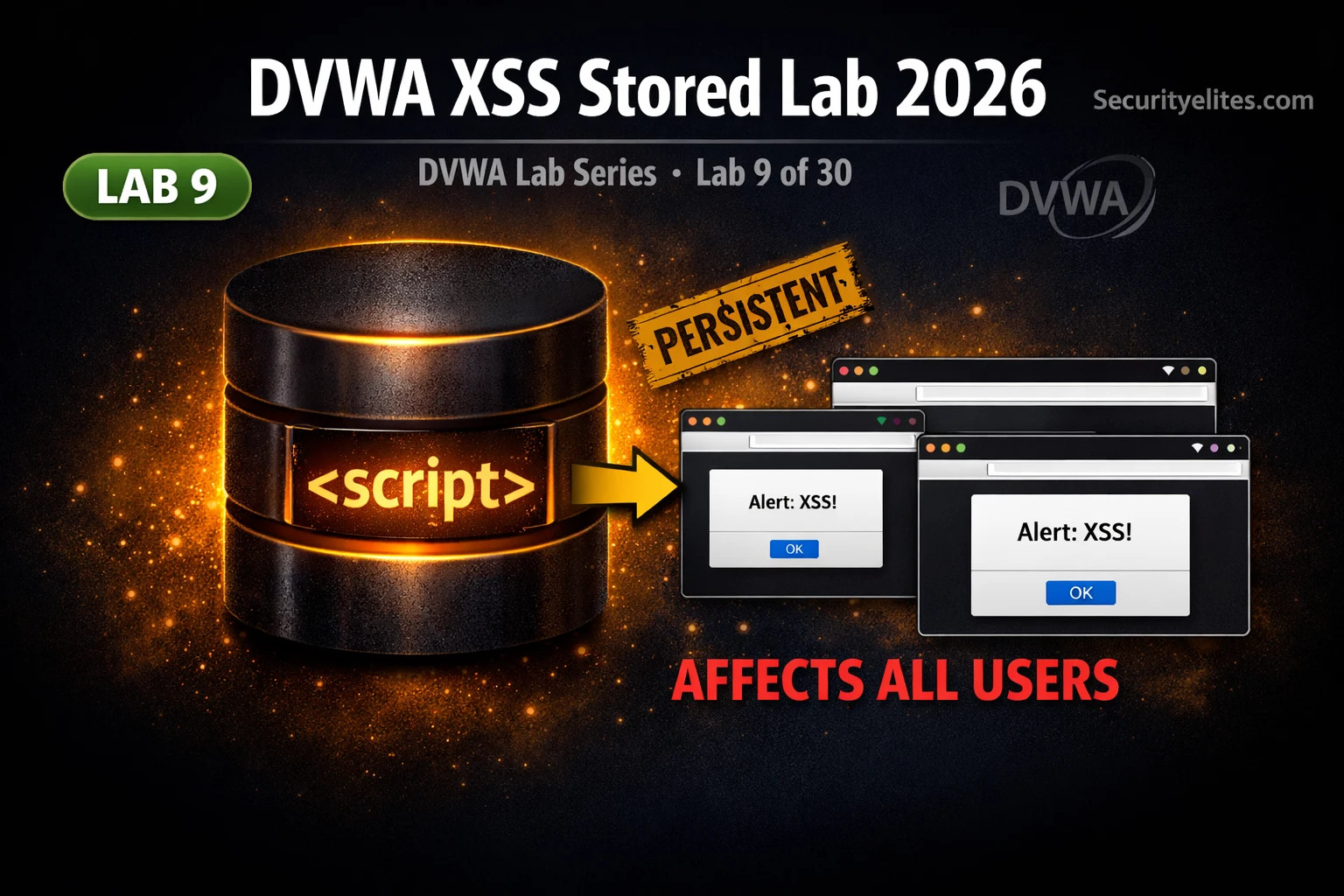
Lab 9: DVWA XSS Stored Lab 2026 — One Payload Hacks Every User (Persistent XSS Exploit Guide)
DVWA xss stored lab 2026 — inject persistent JavaScript payloads into the guestbook, escalate to cookie theft affecting all users,…
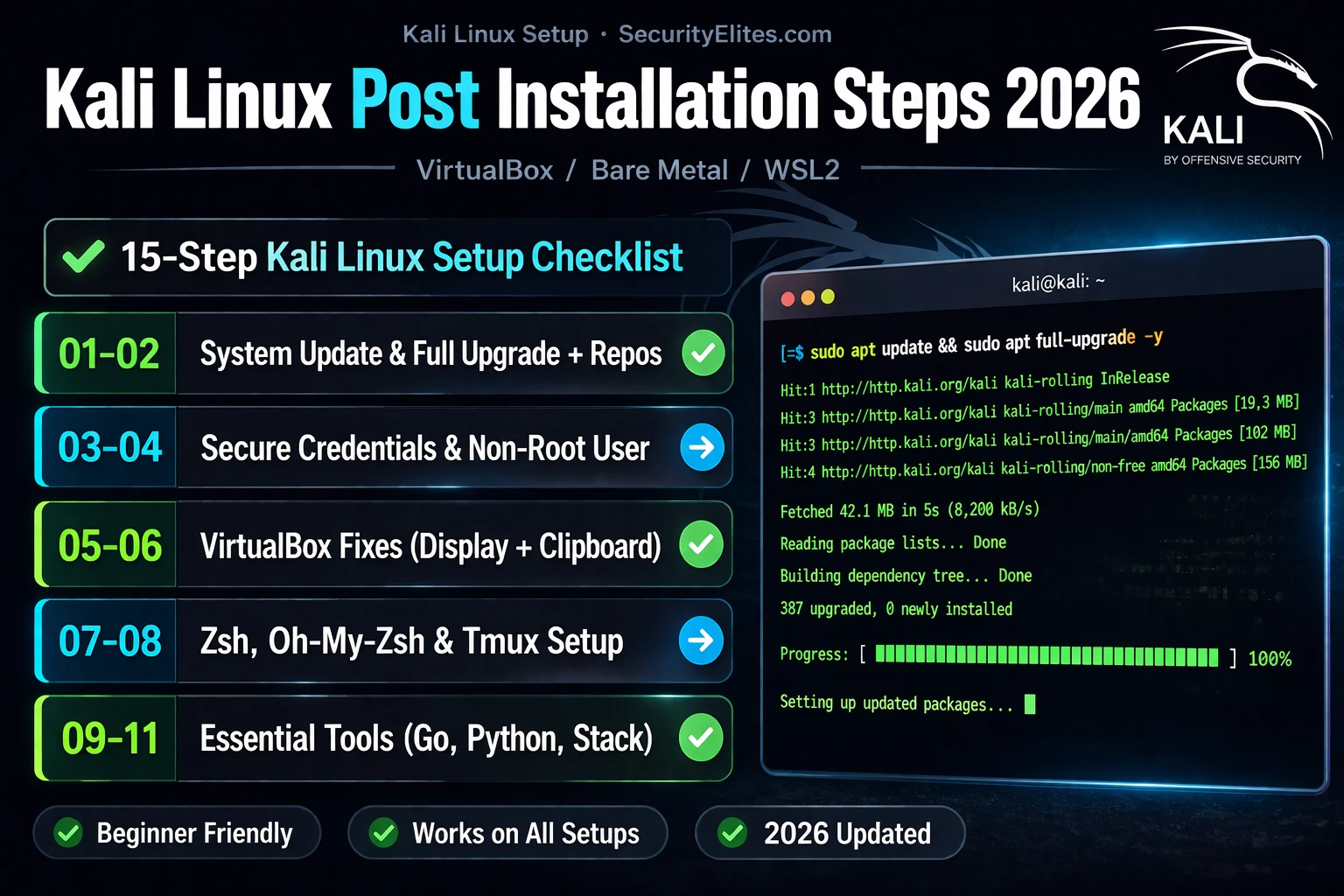
Kali Linux Post Installation Steps 2026 — 15 Things You Must Do After Installing Kali
Kali linux post installation steps 2026 — 15 essential setup tasks after installing Kali: update, configure tools, fix common issues…