Penetration Testing
End-to-end pentest methodology covering networks, web apps, and increasingly AI features. Real engagement workflows from Lokesh Singh aka Mr Elite.
203 articles
Google Dorking for Hackers 2026 — 50 Dorks to Find Vulnerabilities and Exposed Data
Google dorking for hackers 2026 — 50 essential Google dorks to find exposed admin panels, config files, passwords, subdomains and…
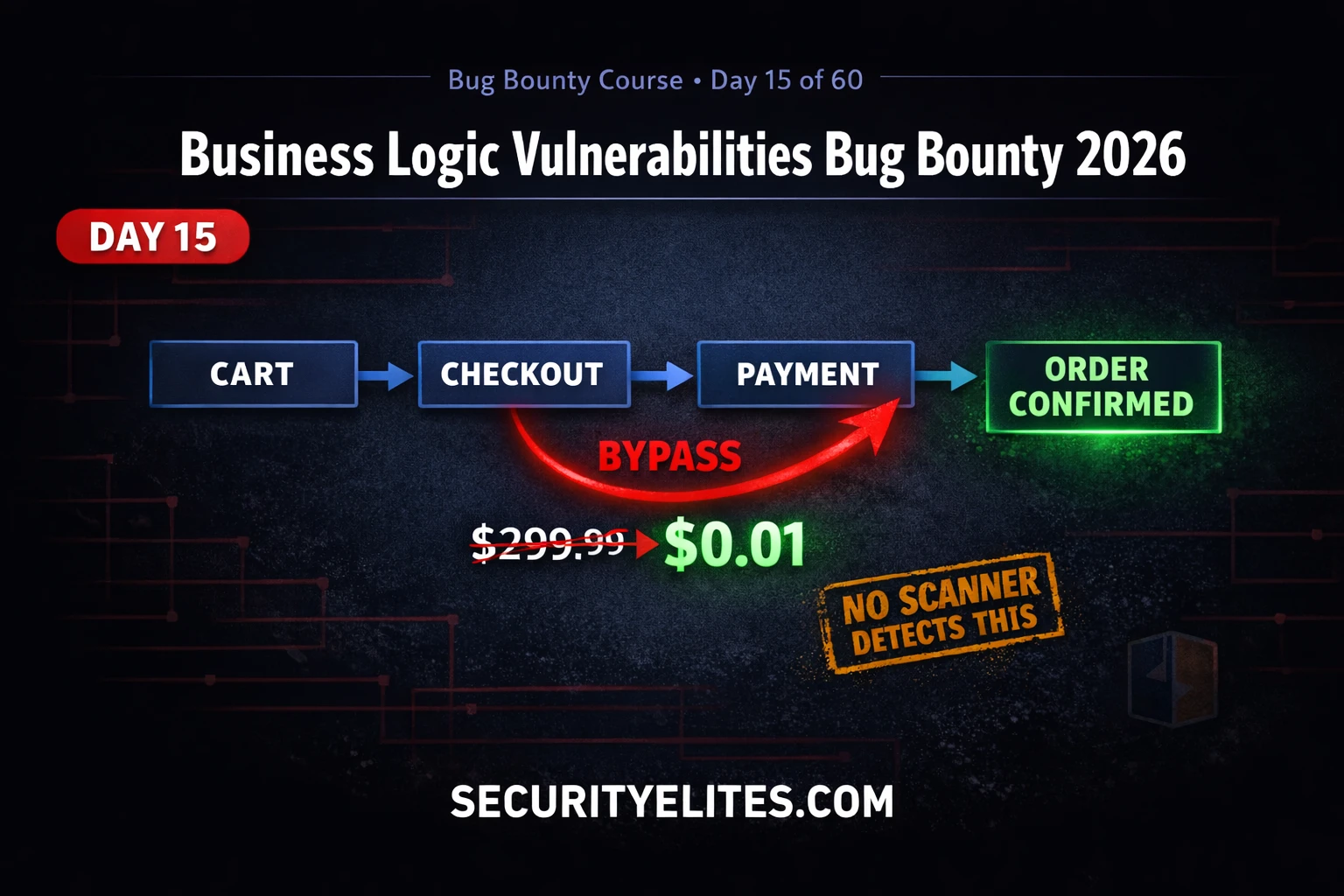
BB Day15: Business Logic Vulnerabilities Bug Bounty 2026 — Bypass Payment Like a Hacker
Business logic vulnerabilities bug bounty 2026 — find price manipulation, workflow bypass and privilege escalation flaws that scanners miss. Day…
Kali Linux Commands Cheat Sheet 2026 — 150 Tools, 2955 Commands, One Click
Kali linux commands cheat sheet 2026 — 150 tools, 2955+ ready-to-use commands across 13 categories. Filter by tool, copy any…
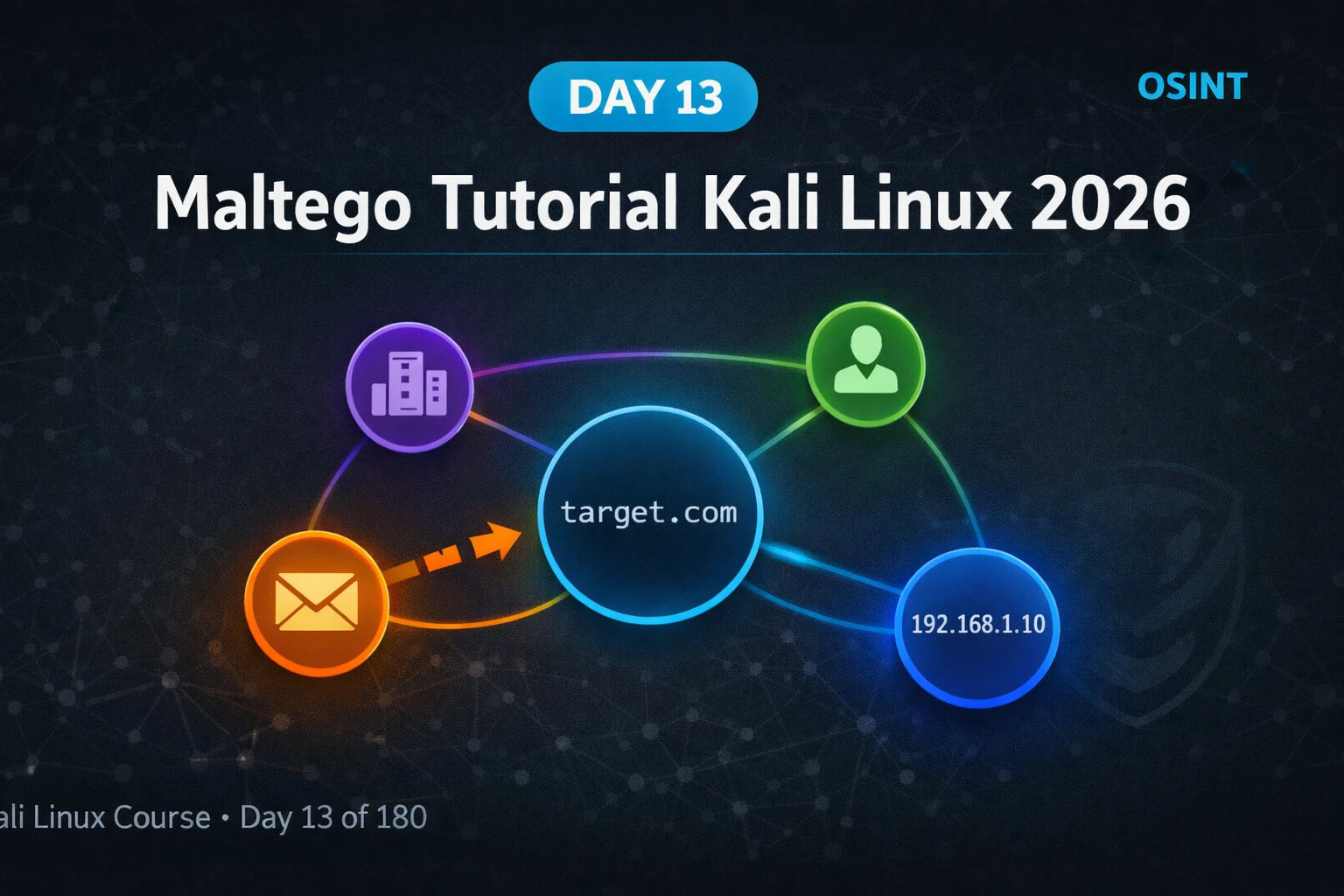
Kali Linux Day13: Maltego Tutorial Kali Linux 2026 — OSINT Link Analysis & Entity Mapping Guide
Maltego tutorial kali linux 2026 — install Community Edition, run transforms, map domains and emails, build entity graphs for OSINT…
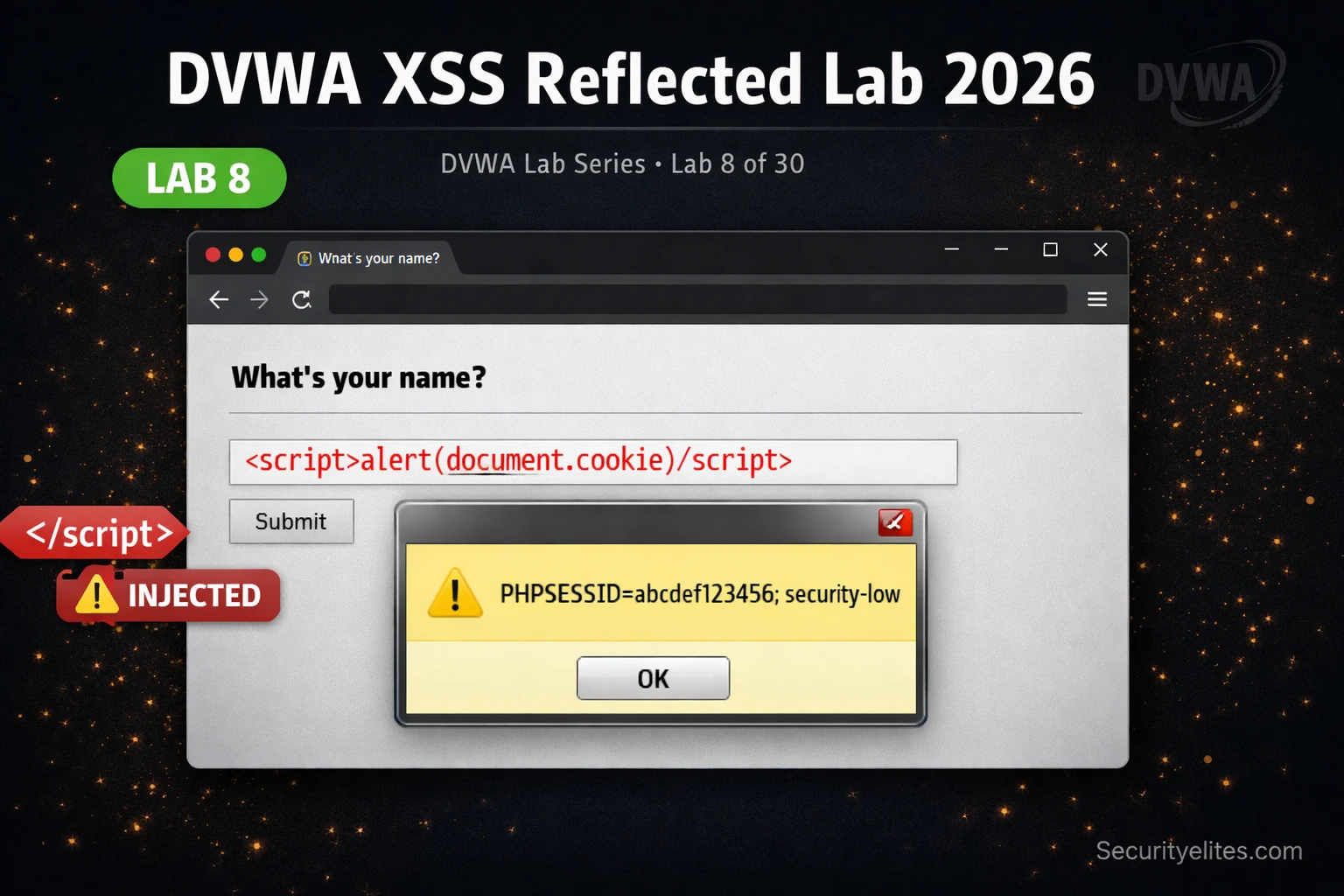
Lab 8: DVWA XSS Reflected Lab 2026 — Steal Cookies in Seconds & Bypass Filters Like a Hacker
DVWA xss reflected lab 2026 — inject JavaScript payloads at all 4 security levels, steal session cookies with Burp, bypass…
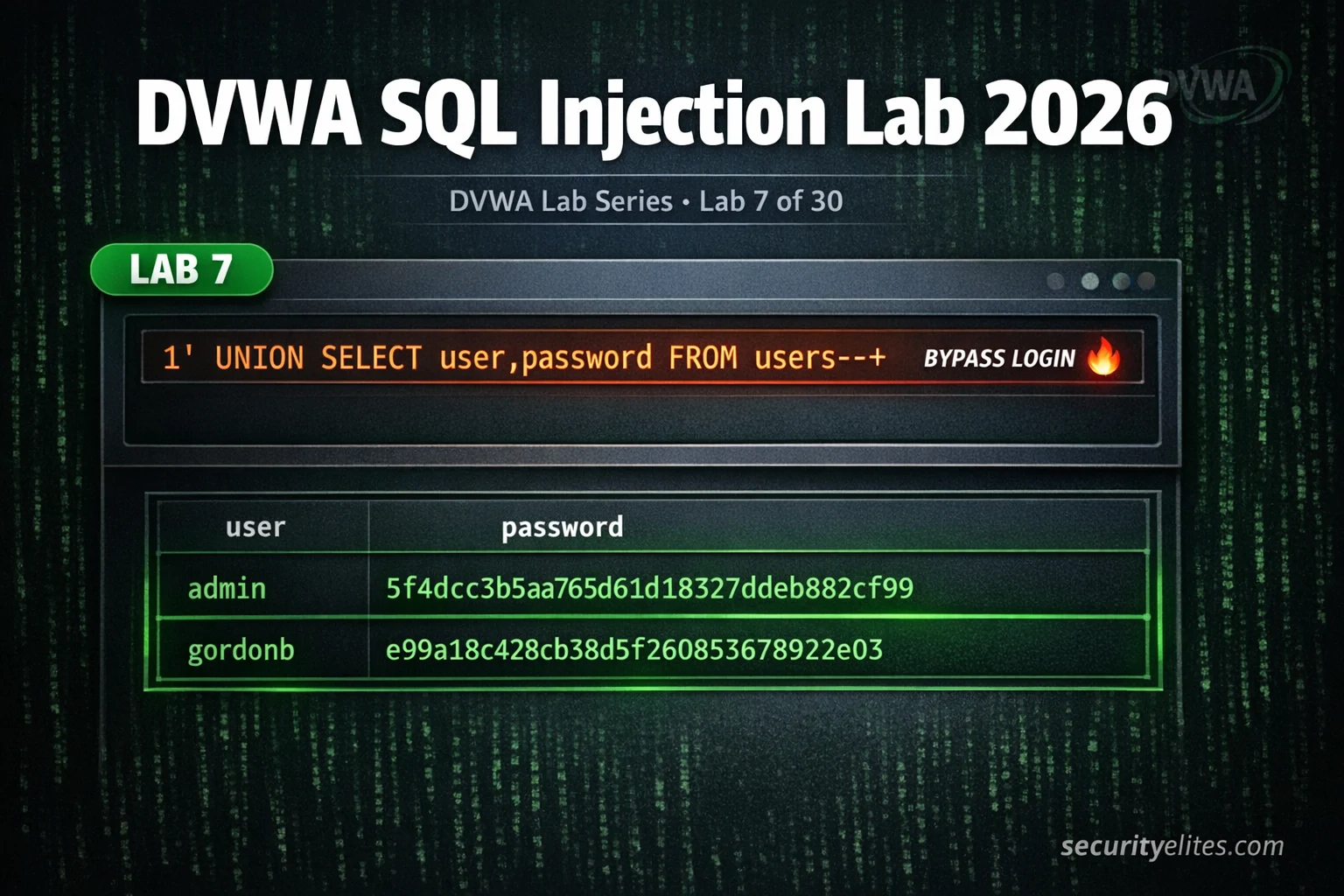
Lab 7: DVWA SQL Injection Lab 2026 — Manual Injection to Full Database Dump Complete Guide
DVWA sql injection lab 2026 — manual injection at all 4 security levels, extract usernames and passwords, bypass filters and…
How to Hack AWS S3 Buckets (Ethically) 2026 — 5 Real Misconfigurations Exposed
Hack aws s3 buckets ethically 2026 — discover 5 real S3 misconfigurations, enumerate public buckets, test ACL weaknesses and report…
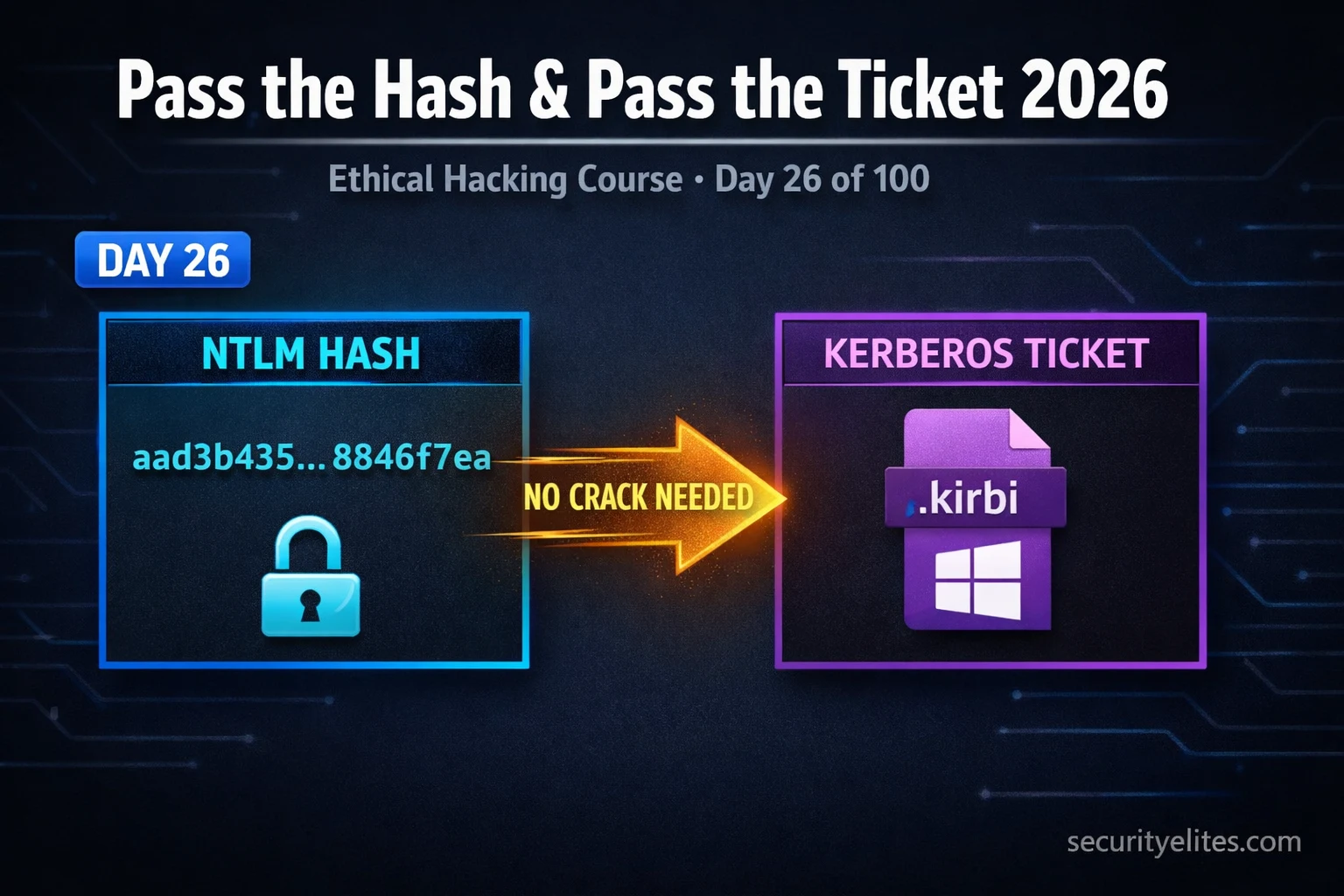
Day 26: Pass the Hash & Pass the Ticket 2026 — Lateral Movement With NTLM & Kerberos
Pass the hash & pass the ticket 2026 — exploit NTLM hashes and Kerberos tickets for lateral movement in Active…
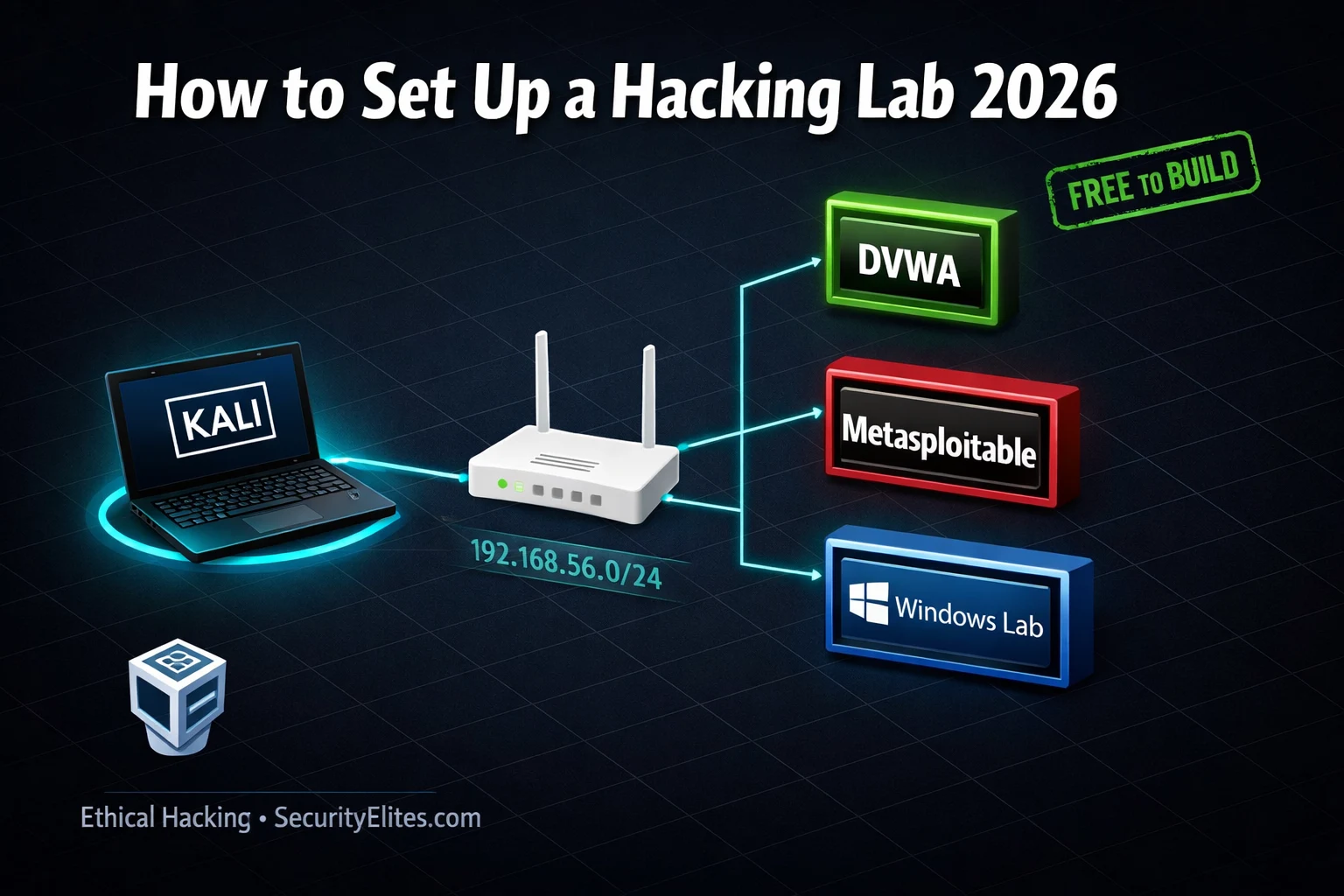
How to Set Up Hacking Lab in 2026 — Complete Home Lab Guide for Ethical Hackers
How to set up hacking lab 2026 — build a complete home ethical hacking lab with VMs, DVWA, Metasploitable and…